Windows Users
Double click an entry on the users list or select an entry and click Edit... to bring up the Edit page with corresponding authentication options.
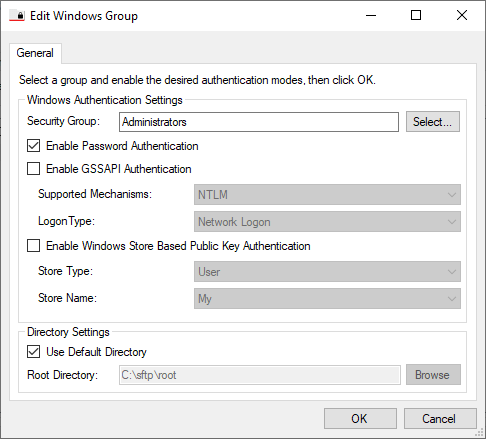
Below are the available options for this page:
- Security Group: This is the name of a Windows group used for authorizing access to the server. Only users who are members of this group will be allowed access. This can be a group in the local machine or a group on the domain.
- Enable Password Authentication: This specifies whether or not Password authentication is allowed. This is enabled by default.
Note that when using Password Authentication, the recommended format for user authentication is "DOMAIN\Username". - Enable GSSAPI Authentication: This allows GSSAPI authentication for connecting clients. This is enabled by default in licensed versions.
- Supported Mechanisms: Specifies the authentication mechanism used. Possible values are All, Kerberos, NTLM. The default value is NTLM.
- Windows Store Based Public Key Authentication: Controls whether Windows-based public key authentication is turned on. When selected, the server will look into the specified certificate store for a certificate with a public key matching the private key presented by the client connection. If one is found, the connection will be allowed; otherwise it will be denied.
- Store Type: Tells the server to look for client certificates in the Machine or User stores.
- Store Name: Tells the server to look for client certificates under the selected store.
Note: The server has no way to match the public keys stored in the certificate store with actual Windows local/domain users. Make sure that the selected certificate store does not contain certificates for people that should not be allowed access to the server.
- Logon Type: Controls the type of logon performed by the application when attempting to authenticate users.
Possible values are:
- Network Logon: Regular network logon is performed. This is more secure, but access to remote network resources is prohibited.
- Interactive Logon: Interactive logon is performed. This is less secure, but allows access to remote network resources.