DCAuth Class
Properties Methods Events Config Settings Errors
The DCAuth class represents the private key side of the SecureBlackbox distributed cryptography protocol.
Syntax
secureblackbox.Dcauth
Remarks
The purpose of DCAuth is to sign async requests produced by SignAsyncBegin calls. For each incoming async request containing a document hash, DCAuth produces the corresponding async response containing a signature over that hash.
Protocol Overview
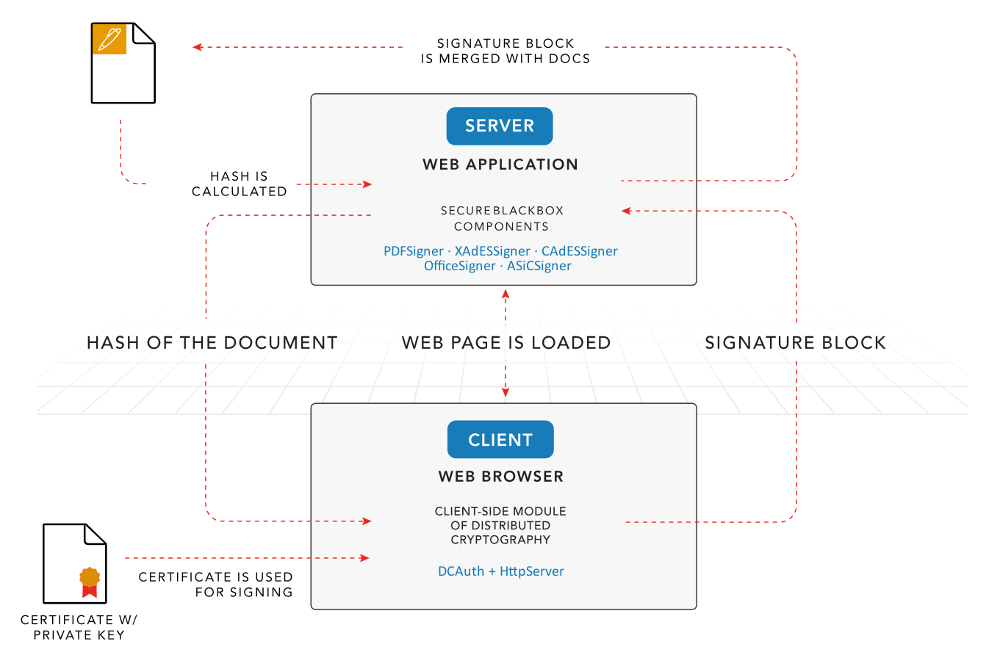
The distributed cryptography protocol involves two principal parties. The signing party, represented by classes such as PDFSigner, XAdESSigner, or OfficeSigner, pre-signs documents (such as PDF files), and encapsulates their hashes into what is called an async request. It then communicates the async request to the private key side, where the DCAuth class extracts the hash and signs it with a local private key. DCAuth then encapsulates the signature into an async response, which is sent back to the signing party. The signing party completes the signing operation by extracting the signature from the async response and embedding it into the pre-signed document.
The protocol supports a variety of uses. The scheme above describes the most typical of them, where the signing party is represented by a web application, and the private key side is represented by a workstation. In that particular scenario DC provides a mechanism for the web app to sign documents residing on the web server with private keys residing on the users workstations, perhaps in non-exportable form (e.g. a USB dongle). Other uses include creation of a signing server for a team of driver developers, or an automated signing gateway for outgoing official documents.
In the webapp-to-browser setting the DCAuth control would normally be used within a web server running on the users workstation. That web server would accept async requests from the web page running in the browser, use DCAuth to generate the matching async response, and feed that response back to the web page. The web page will then submit it back to the web server.
Configuring and Using DCAuth
To process an async request, you need to set up a DCAuth object first, and then call its ProcessRequest method:
- Set the KeyId and KeySecret properties so they match the credentials used by the signing party - e.g. those of PDFSigner object:
DCAuth.KeyId = "mykeyid"; DCAuth.KeySecret = "mykeysecret123";These two properties are used to verify the integrity of the incoming async requests. Keep them safe.
- Provide the signing certificate:
DCAuth.SigningCertificate = "C:\Certs\SigningCert.pfx"; DCAuth.CertPassword = "password789";Alternatively, use StorageId to provide a certificate residing elsewhere, such as a PKCS#11 device.
- Assign the async request to the Input property:
DCAuth.Input = Request;Make sure to provide the request in its original XML format. Some technologies and SecureBlackbox code samples may apply additional encoding when conveying async requests from their origin to the DCAuth endpoint. Please double check that you assign the request without any encodings applied. An async request is a properly formed XML document with the root element of SecureBlackboxAsyncState.
- Call the ProcessRequest method:
DCAuth.ProcessRequest;This method performs the actual signing of the hash. Make sure your code is prepared for potential signing errors.
- If the ProcessRequest call has succeeded, grab the async response from the Output property:
Result = DCAuth.Output;
Property List
The following is the full list of the properties of the class with short descriptions. Click on the links for further details.
| ClaimedSigningTime | The signing time from the signer's computer. |
| ExternalCrypto | Provides access to external signing and DC parameters. |
| FIPSMode | Reserved. |
| Input | Contains the signing request to process. |
| InputEncoding | Specifies request encoding. |
| KeyId | Specifies the KeyID of the pre-shared authentication key. |
| KeySecret | The pre-shared authentication key. |
| Output | Contains the output of the request processing. |
| OutputEncoding | Specifies response encoding. |
| Policies | Specifies the policies to use when processing requests. |
| Profile | Specifies a pre-defined profile to apply when creating the signature. |
| Proxy | The proxy server settings. |
| SigningCertificate | The certificate to be used for signing. |
| SigningChain | The signing certificate chain. |
| SocketSettings | Manages network connection settings. |
| StorageId | Specifies the signing certificate residing in an alternative location. |
| TimestampServer | The address of the timestamping server. |
| TLSClientChain | The TLS client certificate chain. |
| TLSServerChain | The TLS server's certificate chain. |
| TLSSettings | Manages TLS layer settings. |
Method List
The following is the full list of the methods of the class with short descriptions. Click on the links for further details.
| Config | Sets or retrieves a configuration setting. |
| DoAction | Performs an additional action. |
| ProcessRequest | Processes the request. |
Event List
The following is the full list of the events fired by the class with short descriptions. Click on the links for further details.
| CustomParametersReceived | Passes custom request parameters to the application. |
| Error | Reports information about errors during request processing or signing. |
| ExternalSign | Handles remote or external signing initiated by the SignExternal method or other source. |
| KeySecretNeeded | Requests the key secret from the application. |
| Notification | This event notifies the application about an underlying control flow event. |
| ParameterReceived | Passes a standard request parameter to the user code. |
| SignRequest | This event signifies the processing of an atomic signing request. |
| SignRequestCompleted | This event signifies completion of the processing of an atomic signing request. |
| TimestampRequest | Fires when the class is ready to request a timestamp from an external TSA. |
| TLSCertNeeded | Fires when a remote TLS party requests a client certificate. |
| TLSCertValidate | This event is fired upon receipt of the TLS server's certificate, allowing the user to control its acceptance. |
| TLSEstablished | Fires when a TLS handshake with Host successfully completes. |
| TLSHandshake | Fires when a new TLS handshake is initiated, before the handshake commences. |
| TLSShutdown | Reports the graceful closure of a TLS connection. |
Config Settings
The following is a list of config settings for the class with short descriptions. Click on the links for further details.
| DataURL | (obsolete) The DataURL parameter to pass to the signer. |
| GoURL | (obsolete) The GoURL parameter to pass to the signer. |
| RequireDefinedSignCert | (obsolete) The RequireDefinedSignCert parameter to pass to the signer. |
| SchemeParams | The algorithm scheme parameters to employ. |
| SessionID | (obsolete) The SessionID parameter to pass to the signer. |
| TokenName | The TokenName parameter to pass to the signer. |
| TokensLibraries | (obsolete) The TokensLibraries parameter to pass to the signer. |
| CheckKeyIntegrityBeforeUse | Enables or disable private key integrity check before use. |
| CookieCaching | Specifies whether a cookie cache should be used for HTTP(S) transports. |
| Cookies | Gets or sets local cookies for the class. |
| DefDeriveKeyIterations | Specifies the default key derivation algorithm iteration count. |
| EnableClientSideSSLFFDHE | Enables or disables finite field DHE key exchange support in TLS clients. |
| GlobalCookies | Gets or sets global cookies for all the HTTP transports. |
| HttpUserAgent | Specifies the user agent name to be used by all HTTP clients. |
| LogDestination | Specifies the debug log destination. |
| LogDetails | Specifies the debug log details to dump. |
| LogFile | Specifies the debug log filename. |
| LogFilters | Specifies the debug log filters. |
| LogFlushMode | Specifies the log flush mode. |
| LogLevel | Specifies the debug log level. |
| LogMaxEventCount | Specifies the maximum number of events to cache before further action is taken. |
| LogRotationMode | Specifies the log rotation mode. |
| MaxASN1BufferLength | Specifies the maximal allowed length for ASN.1 primitive tag data. |
| MaxASN1TreeDepth | Specifies the maximal depth for processed ASN.1 trees. |
| OCSPHashAlgorithm | Specifies the hash algorithm to be used to identify certificates in OCSP requests. |
| StaticDNS | Specifies whether static DNS rules should be used. |
| StaticIPAddress[domain] | Gets or sets an IP address for the specified domain name. |
| StaticIPAddresses | Gets or sets all the static DNS rules. |
| Tag | Allows to store any custom data. |
| TLSSessionGroup | Specifies the group name of TLS sessions to be used for session resumption. |
| TLSSessionLifetime | Specifies lifetime in seconds of the cached TLS session. |
| TLSSessionPurgeInterval | Specifies how often the session cache should remove the expired TLS sessions. |
| UseOwnDNSResolver | Specifies whether the client classes should use own DNS resolver. |
| UseSharedSystemStorages | Specifies whether the validation engine should use a global per-process copy of the system certificate stores. |
| UseSystemOAEPAndPSS | Enforces or disables the use of system-driven RSA OAEP and PSS computations. |
| UseSystemRandom | Enables or disables the use of the OS PRNG. |
ClaimedSigningTime Property (DCAuth Class)
The signing time from the signer's computer.
Syntax
public String getClaimedSigningTime(); public void setClaimedSigningTime(String claimedSigningTime);
Default Value
""
Remarks
Use this property to provide the signature production time. The claimed time is not supported by a trusted source; it may be inaccurate, forfeited, or wrong, and as such is usually taken for informational purposes only by verifiers. Use timestamp servers to embed verifiable trusted timestamps. The time is in UTC.
ExternalCrypto Property (DCAuth Class)
Provides access to external signing and DC parameters.
Syntax
public ExternalCrypto getExternalCrypto();
Remarks
Use this property to tune-up remote cryptography settings. SecureBlackbox supports two independent types of external cryptography: synchronous (based on the ExternalSign event) and asynchronous (based on the DC protocol and the DCAuth signing component).
This property is read-only.
Please refer to the ExternalCrypto type for a complete list of fields.FIPSMode Property (DCAuth Class)
Reserved.
Syntax
public boolean isFIPSMode(); public void setFIPSMode(boolean FIPSMode);
Default Value
False
Remarks
This property is reserved for future use.
Input Property (DCAuth Class)
Contains the signing request to process.
Syntax
public String getInput(); public void setInput(String input);
Default Value
""
Remarks
Assign the request you received from the counterparty to this property before calling the ProcessRequest method. Use Output to read the resulting signature response after ProcessRequest completes.
InputEncoding Property (DCAuth Class)
Specifies request encoding.
Syntax
public int getInputEncoding(); public void setInputEncoding(int inputEncoding); Enumerated values: public final static int encNone = 0; public final static int encAuto = 1; public final static int encBase64 = 2;
Default Value
0
Remarks
Use this property to specify the encoding to expect the requests to be in.
KeyId Property (DCAuth Class)
Specifies the KeyID of the pre-shared authentication key.
Syntax
public String getKeyId(); public void setKeyId(String keyId);
Default Value
""
Remarks
If processing requests from a single known party, assign the Id of the key you pre-shared with them to this property, and the key itself to the KeySecret property. If you expect to receive requests from many parties with different authentication keys, use KeySecretNeeded event instead.
KeySecret Property (DCAuth Class)
The pre-shared authentication key.
Syntax
public String getKeySecret(); public void setKeySecret(String keySecret);
Default Value
""
Remarks
If processing requests from a single known party, assign the key you pre-shared with them to this property. Use KeyId property to assign the ID of that key. If you expect to receive requests from many parties with different authentication keys, use KeySecretNeeded event instead.
Output Property (DCAuth Class)
Contains the output of the request processing.
Syntax
public String getOutput();
Default Value
""
Remarks
When ProcessRequest method completes it saves the processing output to this property. The output typically contains the response to be sent back to the requestor.
This property is read-only.
OutputEncoding Property (DCAuth Class)
Specifies response encoding.
Syntax
public int getOutputEncoding(); public void setOutputEncoding(int outputEncoding); Enumerated values: public final static int encNone = 0; public final static int encAuto = 1; public final static int encBase64 = 2;
Default Value
0
Remarks
Use this property to specify the encoding you want the response to be produced in.
Policies Property (DCAuth Class)
Specifies the policies to use when processing requests.
Syntax
public int getPolicies(); public void setPolicies(int policies);
Default Value
0
Remarks
This property lets you specify policies to apply blanketly to the requests. If this property does not give you enough flexibility - for example, if you need to cherry-pick requests basing on their content - please consider using the SignRequest (allows you to track individual requests) and/or ExternalSign (lets you perform the signing manually) events. This setting is a bit mask of the following flags:
| aspAcceptUnsignedRequests | 1 | Allows the component to accept unauthenticated messages (those not signed with KeyID/KeySecret). Use with extreme care. |
| aspIgnorePKCS1Requests | 2 | Ignore requests of PKCS1 type. |
| aspIgnorePKCS7Requests | 4 | Ignore requests of PKCS7 type. |
| aspIgnoreRequestTSA | 8 | Ignore the TSA URL provided in the request, and either stick with the service provided via TimestampServer property, or not timestamp the message altogether. |
| aspIgnoreRequestSigningTime | 16 | Ignore the signing time included in the request. |
| aspIgnoreRequestPKCS7Settings | 32 | Ignore auxiliary PKCS7 settings (content type, attributes) included in the request. |
| aspAlwaysTimestampSigs | 64 | Timestamp created signatures (PKCS7 only), even if the client did not request it. |
This property is not available at design time.
Profile Property (DCAuth Class)
Specifies a pre-defined profile to apply when creating the signature.
Syntax
public String getProfile(); public void setProfile(String profile);
Default Value
""
Remarks
Advanced signatures come in many variants, which are often defined by parties that needs to process them or by local standards. SecureBlackbox profiles are sets of pre-defined configurations which correspond to particular signature variants. By specifying a profile, you are pre-configuring the component to make it produce the signature that matches the configuration corresponding to that profile.
Proxy Property (DCAuth Class)
The proxy server settings.
Syntax
public ProxySettings getProxy();
Remarks
Use this property to tune up the proxy server settings.
This property is read-only.
Please refer to the ProxySettings type for a complete list of fields.SigningCertificate Property (DCAuth Class)
The certificate to be used for signing.
Syntax
public Certificate getSigningCertificate(); public void setSigningCertificate(Certificate signingCertificate);
Remarks
Use this property to specify the certificate that shall be used for signing the data. Note that this certificate should have a private key associated with it. Use SigningChain to supply the rest of the certificate chain for inclusion into the signature.
This property is not available at design time.
Please refer to the Certificate type for a complete list of fields.SigningChain Property (DCAuth Class)
The signing certificate chain.
Syntax
public CertificateList getSigningChain(); public void setSigningChain(CertificateList signingChain);
Remarks
Use this property to provide the chain for the signing certificate. Use the SigningCertificate property, if it is available, to provide the signing certificate itself.
This property is not available at design time.
Please refer to the Certificate type for a complete list of fields.SocketSettings Property (DCAuth Class)
Manages network connection settings.
Syntax
public SocketSettings getSocketSettings();
Remarks
Use this property to tune up network connection parameters.
This property is read-only.
Please refer to the SocketSettings type for a complete list of fields.StorageId Property (DCAuth Class)
Specifies the signing certificate residing in an alternative location.
Syntax
public String getStorageId(); public void setStorageId(String storageId);
Default Value
""
Remarks
Use this property to specify the signing certificate contained on alternative media, such as a hardware device or in a system certificate store.
Example 1: The certificate resides on a PKCS#11 device
pkcs11://user:pin@/c:/windows/system32/pkcsdriver.dll?slot=0&readonly=1
Example 2: The certificate resides in a system store
system://localmachine@/?store=MY
You can use the following URI modifiers to provide more accurate specifiers for the needed certificate:
- cn: the common name of the certificate subject.
- keyid: the unique identifier included in subject key identifier extension of the certificate.
- keyusage: a comma-separated list of enabled (+) or disabled (-) key usages. The following usages are supported: signature, nonrepudiation, keyencipherment, dataencipherment, keyagreement, keycertsign, crlsign, encipheronly, decipheronly, serverauth, clientauth, codesigning, emailprotection, timestamping, ocspsigning, smartcardlogon, keypurposeclientauth, keypurposekdc.
- fingerprint: the fingerprint of the certificate.
Example 3: selecting the certificate with a given fingerprint:
pkcs11://user:pin@/c:/windows/system32/pkcsdriver.dll?slot=0&readonly=1&fingerprint=001122334455667788aabbccddeeff0011223344
TimestampServer Property (DCAuth Class)
The address of the timestamping server.
Syntax
public String getTimestampServer(); public void setTimestampServer(String timestampServer);
Default Value
""
Remarks
Use this property to provide the address of the Time Stamping Authority (TSA) server to be used for timestamping the signature.
SecureBlackbox supports RFC3161-compliant timestamping servers, available via HTTP or HTTPS.
If your timestamping service enforces credential-based user authentication (basic or digest), you can provide the credentials in the same URL:
http://user:password@timestamp.server.com/TsaService
For TSAs using certificate-based TLS authentication, provide the client certificate via the TLSClientChain property.
If this property is left empty, no timestamp will be added to the signature.
Starting from summer 2021 update (Vol. 2), the virtual timestamping service is supported, which allows you to intervene in the timestamping routine and provide your own handling for the TSA exchange. This may be handy if the service that you are requesting timestamps from uses a non-standard TSP protocol or requires special authentication option.
To employ the virtual service, assign an URI of the following format to this property:
virtual://localhost?hashonly=true&includecerts=true&reqpolicy=1.2.3.4.5&halg=SHA256
Subscribe to Notification event to get notified about the virtualized timestamping event. The EventID of the timestamping event is TimestampRequest. Inside the event handler, read the base16-encoded request from the EventParam parameter and forward it to the timestamping authority. Upon receiving the response, pass it back to the component, encoded in base16, via the TimestampResponse config property:
component.Config("TimestampResponse=308208ab...");
Note that all the exchange with your custom TSA should take place within the same invocation of the Notification event.
The hashonly parameter of the virtual URI tells the component to only return the timestamp message imprint via the EventParam parameter. If set to false, EventParam will contain the complete RFC3161 timestamping request.
The includecerts parameter specifies that the requestCertificates parameter of the timestamping request should be set to true.
The reqpolicy parameter lets you specify the request policy, and the halg parameter specifies the hash algorithm to use for timestamping.
All the parameters are optional.
TLSClientChain Property (DCAuth Class)
The TLS client certificate chain.
Syntax
public CertificateList getTLSClientChain(); public void setTLSClientChain(CertificateList TLSClientChain);
Remarks
Assign a certificate chain to this property to enable TLS client authentication in the class. Note that the client's end-entity certificate should have a private key associated with it.
Use the CertificateStorage or CertificateManager components to import the certificate from a file, system store, or PKCS11 device.
This property is not available at design time.
Please refer to the Certificate type for a complete list of fields.TLSServerChain Property (DCAuth Class)
The TLS server's certificate chain.
Syntax
public CertificateList getTLSServerChain();
Remarks
Use this property to access the certificate chain sent by the TLS server. This property is ready to read when the TLSCertValidate event is fired by the client component.
This property is read-only and not available at design time.
Please refer to the Certificate type for a complete list of fields.TLSSettings Property (DCAuth Class)
Manages TLS layer settings.
Syntax
public TLSSettings getTLSSettings();
Remarks
Use this property to tune up the TLS layer parameters.
This property is read-only.
Please refer to the TLSSettings type for a complete list of fields.Config Method (Dcauth Class)
Sets or retrieves a configuration setting.
Syntax
public String config(String configurationString);
Remarks
Config is a generic method available in every class. It is used to set and retrieve configuration settings for the class.
These settings are similar in functionality to properties, but they are rarely used. In order to avoid "polluting" the property namespace of the class, access to these internal properties is provided through the Config method.
To set a configuration setting named PROPERTY, you must call Config("PROPERTY=VALUE"), where VALUE is the value of the setting expressed as a string. For boolean values, use the strings "True", "False", "0", "1", "Yes", or "No" (case does not matter).
To read (query) the value of a configuration setting, you must call Config("PROPERTY"). The value will be returned as a string.
DoAction Method (Dcauth Class)
Performs an additional action.
Syntax
public String doAction(String actionID, String actionParams);
Remarks
DoAction is a generic method available in every class. It is used to perform an additional action introduced after the product major release. The list of actions is not fixed, and may be flexibly extended over time.
The unique identifier (case insensitive) of the action is provided in the ActionID parameter.
ActionParams contains the value of a single parameter, or a list of multiple parameters for the action in the form of PARAM1=VALUE1;PARAM2=VALUE2;....
ProcessRequest Method (Dcauth Class)
Processes the request.
Syntax
public void processRequest();
Remarks
Use this method to process the request, sign the hashes, and produce the response. This is the main method of the class. Note that a single request received from the counterparty may contain more than one signature request. This method processes them all, reporting each atomic signature request with SignRequest and SignRequestCompleted events. Before calling this method, make sure you assign the request content to Input. Upon completion, read the response (containing all the signatures) from Output property.
CustomParametersReceived Event (Dcauth Class)
Passes custom request parameters to the application.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void customParametersReceived(DcauthCustomParametersReceivedEvent e) {} ... } public class DcauthCustomParametersReceivedEvent { public String value; }
Remarks
This event is only provided for backward compatibility and is not currently used.
Error Event (Dcauth Class)
Reports information about errors during request processing or signing.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void error(DcauthErrorEvent e) {} ... } public class DcauthErrorEvent { public int errorCode; public String description; }
Remarks
The event is fired if an error occurs during the request processing. Use the ErrorCode and Description parameters to get the details.
ExternalSign Event (Dcauth Class)
Handles remote or external signing initiated by the SignExternal method or other source.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void externalSign(DcauthExternalSignEvent e) {} ... } public class DcauthExternalSignEvent { public String operationId; public String hashAlgorithm; public String pars; public String methodPars; public String data; public String signedData; }
Remarks
Assign a handler to this event if you need to delegate a low-level signing operation to an external, remote, or custom signing engine. Depending on the settings, the handler will receive a hashed or unhashed value to be signed.
The event handler must pass the value of Data to the signer, obtain the signature, and pass it back to the class via the SignedData parameter.
OperationId provides a comment about the operation and its origin. It depends on the exact class being used, and may be empty. HashAlgorithm specifies the hash algorithm being used for the operation, and Pars contains algorithm-dependent parameters.
The class uses base16 (hex) encoding for the Data, SignedData, and Pars parameters. If your signing engine uses a different input and output encoding, you may need to decode and/or encode the data before and/or after the signing.
A sample MD5 hash encoded in base16: a0dee2a0382afbb09120ffa7ccd8a152 - lower case base16 A0DEE2A0382AFBB09120FFA7CCD8A152 - upper case base16
A sample event handler that uses the .NET RSACryptoServiceProvider class may look like the following:
signer.OnExternalSign += (s, e) =>
{
var cert = new X509Certificate2("cert.pfx", "", X509KeyStorageFlags.Exportable);
var key = (RSACryptoServiceProvider)cert.PrivateKey;
var dataToSign = e.Data.FromBase16String();
var signedData = key.SignHash(dataToSign, "2.16.840.1.101.3.4.2.1");
e.SignedData = signedData.ToBase16String();
};
The MethodPars parameter contains the method-specific parameters. For example, for PKCS7 requests it contains the requested parameters of the PKCS7 blob.
KeySecretNeeded Event (Dcauth Class)
Requests the key secret from the application.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void keySecretNeeded(DcauthKeySecretNeededEvent e) {} ... } public class DcauthKeySecretNeededEvent { public String keyId; public String keySecret; }
Remarks
Subscribe to this event to pass the key secret (a pre-shared request authentication code) to the signing component when it is needed. The authentication combination consists of the KeyId, a non-secret unique key identifier, and the KeySecret, shared by the parties, which should be kept private. This event is an alternative for KeySecret property. Use it when you expect to process requests from requestors with different KeyIds and secrets. If you only expect to receive requests from a single requestor with a known KeyId, providing the key secret via KeyId and KeySecret properties would be an easier route.
Notification Event (Dcauth Class)
This event notifies the application about an underlying control flow event.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void notification(DcauthNotificationEvent e) {} ... } public class DcauthNotificationEvent { public String eventID; public String eventParam; }
Remarks
The class fires this event to let the application know about some event, occurrence, or milestone in the class. For example, it may fire to report completion of the document processing. The list of events being reported is not fixed, and may be flexibly extended over time.
The unique identifier of the event is provided in the EventID parameter. EventParam contains any parameters accompanying the occurrence. Depending on the type of the class, the exact action it is performing, or the document being processed, one or both may be omitted.
ParameterReceived Event (Dcauth Class)
Passes a standard request parameter to the user code.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void parameterReceived(DcauthParameterReceivedEvent e) {} ... } public class DcauthParameterReceivedEvent { public String name; public String value; }
Remarks
This event is only provided for backward compatibility and is not currently used.
SignRequest Event (Dcauth Class)
This event signifies the processing of an atomic signing request.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void signRequest(DcauthSignRequestEvent e) {} ... } public class DcauthSignRequestEvent { public int method; public String hashAlgorithm; public byte[] hash; public String keyID; public String pars; public String methodPars; public boolean allow; }
Remarks
Subscribe to this event to be notified of every signature request processed by the DC server. Note that any one request coming from the requestor may contain multiple individual signature requests (so-called 'batching'). This event is a good mechanism to track signature requests for accountability purposes, and provide basic access control over the signing operations. The Method parameter specifies the async signing method requested by the client:
| asmdPKCS1 | 0 |
| asmdPKCS7 | 1 |
The Hash parameter contains the hash, made using HashAlgorithm, that needs to be signed. KeyID contains the key identifier of the requestor.
The Pars string contains a semicolon-separated string of the principal signature parameters. This has the same format and content that is passed to ExternalSign, if it is used. The MethodPars contains a similar parameter string, but for the specific async signing method used. For the PKCS1 method there are no defined method parameters, while the PKCS7 method supports a selection of settings that tune up the CMS blob.
Set Allow to false to stop the request from being served. Use the SignRequestCompleted event to track completion of the initiated operation.
SignRequestCompleted Event (Dcauth Class)
This event signifies completion of the processing of an atomic signing request.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void signRequestCompleted(DcauthSignRequestCompletedEvent e) {} ... } public class DcauthSignRequestCompletedEvent { public int method; public String hashAlgorithm; public byte[] hash; public String keyID; public String pars; public String methodPars; public byte[] signature; }
Remarks
Use this event to track completion of signing request processing. The Hash parameter contains the hash that is signed, as supplied by the requestor, and the Signature parameter contains the resulting cryptographic signature. The KeyID parameter matches the parameter in SignRequest event.
TimestampRequest Event (Dcauth Class)
Fires when the class is ready to request a timestamp from an external TSA.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void timestampRequest(DcauthTimestampRequestEvent e) {} ... } public class DcauthTimestampRequestEvent { public String TSA; public String timestampRequest; public String timestampResponse; public boolean suppressDefault; }
Remarks
Subscribe to this event to intercept timestamp requests. You can use it to override timestamping requests and perform them in your code.
The TSA parameter indicates the timestamping service being used. It matches the value passed to the TimestampServer property. Set the SuppressDefault parameter to false if you would like to stop the built-in TSA request from going ahead. The built-in TSA request is also not performed if the returned TimestampResponse parameter is not empty.
TLSCertNeeded Event (Dcauth Class)
Fires when a remote TLS party requests a client certificate.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void TLSCertNeeded(DcauthTLSCertNeededEvent e) {} ... } public class DcauthTLSCertNeededEvent { public String host; public String CANames; }
Remarks
This event fires to notify the implementation that a remote TLS server has requested a client certificate. The Host parameter identifies the host that makes a request, and the CANames parameter (optional, according to the TLS spec) advises on the accepted issuing CAs.
Use the TLSClientChain property in response to this event to provide the requested certificate. Please make sure the client certificate includes the associated private key. Note that you may set the certificates before the connection without waiting for this event to fire.
This event is preceded by the TLSHandshake event for the given host and, if the certificate was accepted, succeeded by the TLSEstablished event.
TLSCertValidate Event (Dcauth Class)
This event is fired upon receipt of the TLS server's certificate, allowing the user to control its acceptance.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void TLSCertValidate(DcauthTLSCertValidateEvent e) {} ... } public class DcauthTLSCertValidateEvent { public String serverHost; public String serverIP; public boolean accept; }
Remarks
This event is fired during a TLS handshake. Use the TLSServerChain property to access the certificate chain. In general, classes may contact a number of TLS endpoints during their work, depending on their configuration.
Accept is assigned in accordance with the outcome of the internal validation check performed by the class, and can be adjusted if needed.
TLSEstablished Event (Dcauth Class)
Fires when a TLS handshake with Host successfully completes.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void TLSEstablished(DcauthTLSEstablishedEvent e) {} ... } public class DcauthTLSEstablishedEvent { public String host; public String version; public String ciphersuite; public byte[] connectionId; public boolean abort; }
Remarks
The class uses this event to notify the application about a successful completion of a TLS handshake.
The Version, Ciphersuite, and ConnectionId parameters indicate the security parameters of the new connection. Use the Abort parameter if you need to terminate the connection at this stage.
TLSHandshake Event (Dcauth Class)
Fires when a new TLS handshake is initiated, before the handshake commences.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void TLSHandshake(DcauthTLSHandshakeEvent e) {} ... } public class DcauthTLSHandshakeEvent { public String host; public boolean abort; }
Remarks
The class uses this event to notify the application about the start of a new TLS handshake to Host. If the handshake is successful, this event will be followed by the TLSEstablished event. If the server chooses to request a client certificate, the TLSCertNeeded event will also be fired.
TLSShutdown Event (Dcauth Class)
Reports the graceful closure of a TLS connection.
Syntax
public class DefaultDcauthEventListener implements DcauthEventListener { ... public void TLSShutdown(DcauthTLSShutdownEvent e) {} ... } public class DcauthTLSShutdownEvent { public String host; }
Remarks
This event notifies the application about the closure of an earlier established TLS connection. Note that only graceful connection closures are reported.
Certificate Type
Provides details of an individual X.509 certificate.
Remarks
This type provides access to X.509 certificate details.
Fields
Bytes
byte[] (read-only)
Default Value: ""
Returns the raw certificate data in DER format.
CA
boolean
Default Value: False
Indicates whether the certificate has a CA capability (a setting in the BasicConstraints extension).
CAKeyID
byte[] (read-only)
Default Value: ""
A unique identifier (fingerprint) of the CA certificate's private key.
Authority Key Identifier is a (non-critical) X.509 certificate extension which allows the identification of certificates produced by the same issuer, but with different public keys.
CRLDistributionPoints
String
Default Value: ""
Locations of the CRL (Certificate Revocation List) distribution points used to check this certificate's validity.
Curve
String
Default Value: ""
Specifies the elliptic curve of the EC public key.
| SB_EC_SECP112R1 | SECP112R1 | |
| SB_EC_SECP112R2 | SECP112R2 | |
| SB_EC_SECP128R1 | SECP128R1 | |
| SB_EC_SECP128R2 | SECP128R2 | |
| SB_EC_SECP160K1 | SECP160K1 | |
| SB_EC_SECP160R1 | SECP160R1 | |
| SB_EC_SECP160R2 | SECP160R2 | |
| SB_EC_SECP192K1 | SECP192K1 | |
| SB_EC_SECP192R1 | SECP192R1 | |
| SB_EC_SECP224K1 | SECP224K1 | |
| SB_EC_SECP224R1 | SECP224R1 | |
| SB_EC_SECP256K1 | SECP256K1 | |
| SB_EC_SECP256R1 | SECP256R1 | |
| SB_EC_SECP384R1 | SECP384R1 | |
| SB_EC_SECP521R1 | SECP521R1 | |
| SB_EC_SECT113R1 | SECT113R1 | |
| SB_EC_SECT113R2 | SECT113R2 | |
| SB_EC_SECT131R1 | SECT131R1 | |
| SB_EC_SECT131R2 | SECT131R2 | |
| SB_EC_SECT163K1 | SECT163K1 | |
| SB_EC_SECT163R1 | SECT163R1 | |
| SB_EC_SECT163R2 | SECT163R2 | |
| SB_EC_SECT193R1 | SECT193R1 | |
| SB_EC_SECT193R2 | SECT193R2 | |
| SB_EC_SECT233K1 | SECT233K1 | |
| SB_EC_SECT233R1 | SECT233R1 | |
| SB_EC_SECT239K1 | SECT239K1 | |
| SB_EC_SECT283K1 | SECT283K1 | |
| SB_EC_SECT283R1 | SECT283R1 | |
| SB_EC_SECT409K1 | SECT409K1 | |
| SB_EC_SECT409R1 | SECT409R1 | |
| SB_EC_SECT571K1 | SECT571K1 | |
| SB_EC_SECT571R1 | SECT571R1 | |
| SB_EC_PRIME192V1 | PRIME192V1 | |
| SB_EC_PRIME192V2 | PRIME192V2 | |
| SB_EC_PRIME192V3 | PRIME192V3 | |
| SB_EC_PRIME239V1 | PRIME239V1 | |
| SB_EC_PRIME239V2 | PRIME239V2 | |
| SB_EC_PRIME239V3 | PRIME239V3 | |
| SB_EC_PRIME256V1 | PRIME256V1 | |
| SB_EC_C2PNB163V1 | C2PNB163V1 | |
| SB_EC_C2PNB163V2 | C2PNB163V2 | |
| SB_EC_C2PNB163V3 | C2PNB163V3 | |
| SB_EC_C2PNB176W1 | C2PNB176W1 | |
| SB_EC_C2TNB191V1 | C2TNB191V1 | |
| SB_EC_C2TNB191V2 | C2TNB191V2 | |
| SB_EC_C2TNB191V3 | C2TNB191V3 | |
| SB_EC_C2ONB191V4 | C2ONB191V4 | |
| SB_EC_C2ONB191V5 | C2ONB191V5 | |
| SB_EC_C2PNB208W1 | C2PNB208W1 | |
| SB_EC_C2TNB239V1 | C2TNB239V1 | |
| SB_EC_C2TNB239V2 | C2TNB239V2 | |
| SB_EC_C2TNB239V3 | C2TNB239V3 | |
| SB_EC_C2ONB239V4 | C2ONB239V4 | |
| SB_EC_C2ONB239V5 | C2ONB239V5 | |
| SB_EC_C2PNB272W1 | C2PNB272W1 | |
| SB_EC_C2PNB304W1 | C2PNB304W1 | |
| SB_EC_C2TNB359V1 | C2TNB359V1 | |
| SB_EC_C2PNB368W1 | C2PNB368W1 | |
| SB_EC_C2TNB431R1 | C2TNB431R1 | |
| SB_EC_NISTP192 | NISTP192 | |
| SB_EC_NISTP224 | NISTP224 | |
| SB_EC_NISTP256 | NISTP256 | |
| SB_EC_NISTP384 | NISTP384 | |
| SB_EC_NISTP521 | NISTP521 | |
| SB_EC_NISTB163 | NISTB163 | |
| SB_EC_NISTB233 | NISTB233 | |
| SB_EC_NISTB283 | NISTB283 | |
| SB_EC_NISTB409 | NISTB409 | |
| SB_EC_NISTB571 | NISTB571 | |
| SB_EC_NISTK163 | NISTK163 | |
| SB_EC_NISTK233 | NISTK233 | |
| SB_EC_NISTK283 | NISTK283 | |
| SB_EC_NISTK409 | NISTK409 | |
| SB_EC_NISTK571 | NISTK571 | |
| SB_EC_GOSTCPTEST | GOSTCPTEST | |
| SB_EC_GOSTCPA | GOSTCPA | |
| SB_EC_GOSTCPB | GOSTCPB | |
| SB_EC_GOSTCPC | GOSTCPC | |
| SB_EC_GOSTCPXCHA | GOSTCPXCHA | |
| SB_EC_GOSTCPXCHB | GOSTCPXCHB | |
| SB_EC_BRAINPOOLP160R1 | BRAINPOOLP160R1 | |
| SB_EC_BRAINPOOLP160T1 | BRAINPOOLP160T1 | |
| SB_EC_BRAINPOOLP192R1 | BRAINPOOLP192R1 | |
| SB_EC_BRAINPOOLP192T1 | BRAINPOOLP192T1 | |
| SB_EC_BRAINPOOLP224R1 | BRAINPOOLP224R1 | |
| SB_EC_BRAINPOOLP224T1 | BRAINPOOLP224T1 | |
| SB_EC_BRAINPOOLP256R1 | BRAINPOOLP256R1 | |
| SB_EC_BRAINPOOLP256T1 | BRAINPOOLP256T1 | |
| SB_EC_BRAINPOOLP320R1 | BRAINPOOLP320R1 | |
| SB_EC_BRAINPOOLP320T1 | BRAINPOOLP320T1 | |
| SB_EC_BRAINPOOLP384R1 | BRAINPOOLP384R1 | |
| SB_EC_BRAINPOOLP384T1 | BRAINPOOLP384T1 | |
| SB_EC_BRAINPOOLP512R1 | BRAINPOOLP512R1 | |
| SB_EC_BRAINPOOLP512T1 | BRAINPOOLP512T1 | |
| SB_EC_CURVE25519 | CURVE25519 | |
| SB_EC_CURVE448 | CURVE448 |
Fingerprint
byte[] (read-only)
Default Value: ""
Contains the fingerprint (a hash imprint) of this certificate.
FriendlyName
String (read-only)
Default Value: ""
Contains an associated alias (friendly name) of the certificate.
HashAlgorithm
String
Default Value: ""
Specifies the hash algorithm to be used in the operations on the certificate (such as key signing)
| SB_HASH_ALGORITHM_SHA1 | SHA1 | |
| SB_HASH_ALGORITHM_SHA224 | SHA224 | |
| SB_HASH_ALGORITHM_SHA256 | SHA256 | |
| SB_HASH_ALGORITHM_SHA384 | SHA384 | |
| SB_HASH_ALGORITHM_SHA512 | SHA512 | |
| SB_HASH_ALGORITHM_MD2 | MD2 | |
| SB_HASH_ALGORITHM_MD4 | MD4 | |
| SB_HASH_ALGORITHM_MD5 | MD5 | |
| SB_HASH_ALGORITHM_RIPEMD160 | RIPEMD160 | |
| SB_HASH_ALGORITHM_CRC32 | CRC32 | |
| SB_HASH_ALGORITHM_SSL3 | SSL3 | |
| SB_HASH_ALGORITHM_GOST_R3411_1994 | GOST1994 | |
| SB_HASH_ALGORITHM_WHIRLPOOL | WHIRLPOOL | |
| SB_HASH_ALGORITHM_POLY1305 | POLY1305 | |
| SB_HASH_ALGORITHM_SHA3_224 | SHA3_224 | |
| SB_HASH_ALGORITHM_SHA3_256 | SHA3_256 | |
| SB_HASH_ALGORITHM_SHA3_384 | SHA3_384 | |
| SB_HASH_ALGORITHM_SHA3_512 | SHA3_512 | |
| SB_HASH_ALGORITHM_BLAKE2S_128 | BLAKE2S_128 | |
| SB_HASH_ALGORITHM_BLAKE2S_160 | BLAKE2S_160 | |
| SB_HASH_ALGORITHM_BLAKE2S_224 | BLAKE2S_224 | |
| SB_HASH_ALGORITHM_BLAKE2S_256 | BLAKE2S_256 | |
| SB_HASH_ALGORITHM_BLAKE2B_160 | BLAKE2B_160 | |
| SB_HASH_ALGORITHM_BLAKE2B_256 | BLAKE2B_256 | |
| SB_HASH_ALGORITHM_BLAKE2B_384 | BLAKE2B_384 | |
| SB_HASH_ALGORITHM_BLAKE2B_512 | BLAKE2B_512 | |
| SB_HASH_ALGORITHM_SHAKE_128 | SHAKE_128 | |
| SB_HASH_ALGORITHM_SHAKE_256 | SHAKE_256 | |
| SB_HASH_ALGORITHM_SHAKE_128_LEN | SHAKE_128_LEN | |
| SB_HASH_ALGORITHM_SHAKE_256_LEN | SHAKE_256_LEN |
Issuer
String (read-only)
Default Value: ""
The common name of the certificate issuer (CA), typically a company name.
IssuerRDN
String
Default Value: ""
A collection of information, in the form of [OID, Value] pairs, uniquely identifying the certificate issuer.
KeyAlgorithm
String
Default Value: "0"
Specifies the public key algorithm of this certificate.
| SB_CERT_ALGORITHM_ID_RSA_ENCRYPTION | rsaEncryption | |
| SB_CERT_ALGORITHM_MD2_RSA_ENCRYPTION | md2withRSAEncryption | |
| SB_CERT_ALGORITHM_MD5_RSA_ENCRYPTION | md5withRSAEncryption | |
| SB_CERT_ALGORITHM_SHA1_RSA_ENCRYPTION | sha1withRSAEncryption | |
| SB_CERT_ALGORITHM_ID_DSA | id-dsa | |
| SB_CERT_ALGORITHM_ID_DSA_SHA1 | id-dsa-with-sha1 | |
| SB_CERT_ALGORITHM_DH_PUBLIC | dhpublicnumber | |
| SB_CERT_ALGORITHM_SHA224_RSA_ENCRYPTION | sha224WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA256_RSA_ENCRYPTION | sha256WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA384_RSA_ENCRYPTION | sha384WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA512_RSA_ENCRYPTION | sha512WithRSAEncryption | |
| SB_CERT_ALGORITHM_ID_RSAPSS | id-RSASSA-PSS | |
| SB_CERT_ALGORITHM_ID_RSAOAEP | id-RSAES-OAEP | |
| SB_CERT_ALGORITHM_RSASIGNATURE_RIPEMD160 | ripemd160withRSA | |
| SB_CERT_ALGORITHM_ID_ELGAMAL | elGamal | |
| SB_CERT_ALGORITHM_SHA1_ECDSA | ecdsa-with-SHA1 | |
| SB_CERT_ALGORITHM_RECOMMENDED_ECDSA | ecdsa-recommended | |
| SB_CERT_ALGORITHM_SHA224_ECDSA | ecdsa-with-SHA224 | |
| SB_CERT_ALGORITHM_SHA256_ECDSA | ecdsa-with-SHA256 | |
| SB_CERT_ALGORITHM_SHA384_ECDSA | ecdsa-with-SHA384 | |
| SB_CERT_ALGORITHM_SHA512_ECDSA | ecdsa-with-SHA512 | |
| SB_CERT_ALGORITHM_EC | id-ecPublicKey | |
| SB_CERT_ALGORITHM_SPECIFIED_ECDSA | ecdsa-specified | |
| SB_CERT_ALGORITHM_GOST_R3410_1994 | id-GostR3410-94 | |
| SB_CERT_ALGORITHM_GOST_R3410_2001 | id-GostR3410-2001 | |
| SB_CERT_ALGORITHM_GOST_R3411_WITH_R3410_1994 | id-GostR3411-94-with-GostR3410-94 | |
| SB_CERT_ALGORITHM_GOST_R3411_WITH_R3410_2001 | id-GostR3411-94-with-GostR3410-2001 | |
| SB_CERT_ALGORITHM_SHA1_ECDSA_PLAIN | ecdsa-plain-SHA1 | |
| SB_CERT_ALGORITHM_SHA224_ECDSA_PLAIN | ecdsa-plain-SHA224 | |
| SB_CERT_ALGORITHM_SHA256_ECDSA_PLAIN | ecdsa-plain-SHA256 | |
| SB_CERT_ALGORITHM_SHA384_ECDSA_PLAIN | ecdsa-plain-SHA384 | |
| SB_CERT_ALGORITHM_SHA512_ECDSA_PLAIN | ecdsa-plain-SHA512 | |
| SB_CERT_ALGORITHM_RIPEMD160_ECDSA_PLAIN | ecdsa-plain-RIPEMD160 | |
| SB_CERT_ALGORITHM_WHIRLPOOL_RSA_ENCRYPTION | whirlpoolWithRSAEncryption | |
| SB_CERT_ALGORITHM_ID_DSA_SHA224 | id-dsa-with-sha224 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA256 | id-dsa-with-sha256 | |
| SB_CERT_ALGORITHM_SHA3_224_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-512 | |
| SB_CERT_ALGORITHM_SHA3_224_ECDSA | id-ecdsa-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_ECDSA | id-ecdsa-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_ECDSA | id-ecdsa-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_ECDSA | id-ecdsa-with-sha3-512 | |
| SB_CERT_ALGORITHM_SHA3_224_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-512 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA3_224 | id-dsa-with-sha3-224 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA3_256 | id-dsa-with-sha3-256 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b512 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_ECDSA | id-ecdsa-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_ECDSA | id-ecdsa-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_ECDSA | id-ecdsa-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_ECDSA | id-ecdsa-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_ECDSA | id-ecdsa-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_ECDSA | id-ecdsa-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_ECDSA | id-ecdsa-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_ECDSA | id-ecdsa-with-blake2b512 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b512 | |
| SB_CERT_ALGORITHM_ID_DSA_BLAKE2S_224 | id-dsa-with-blake2s224 | |
| SB_CERT_ALGORITHM_ID_DSA_BLAKE2S_256 | id-dsa-with-blake2s256 | |
| SB_CERT_ALGORITHM_EDDSA_ED25519 | id-Ed25519 | |
| SB_CERT_ALGORITHM_EDDSA_ED448 | id-Ed448 | |
| SB_CERT_ALGORITHM_EDDSA_ED25519_PH | id-Ed25519ph | |
| SB_CERT_ALGORITHM_EDDSA_ED448_PH | id-Ed448ph | |
| SB_CERT_ALGORITHM_EDDSA | id-EdDSA | |
| SB_CERT_ALGORITHM_EDDSA_SIGNATURE | id-EdDSA-sig |
KeyBits
int (read-only)
Default Value: 0
Returns the length of the public key.
KeyFingerprint
byte[] (read-only)
Default Value: ""
Returns a fingerprint of the public key contained in the certificate.
KeyUsage
int
Default Value: 0
Indicates the purposes of the key contained in the certificate, in the form of an OR'ed flag set.
This value is a bit mask of the following values:
| ckuUnknown | 0x00000 | Unknown key usage |
| ckuDigitalSignature | 0x00001 | Digital signature |
| ckuNonRepudiation | 0x00002 | Non-repudiation |
| ckuKeyEncipherment | 0x00004 | Key encipherment |
| ckuDataEncipherment | 0x00008 | Data encipherment |
| ckuKeyAgreement | 0x00010 | Key agreement |
| ckuKeyCertSign | 0x00020 | Certificate signing |
| ckuCRLSign | 0x00040 | Revocation signing |
| ckuEncipherOnly | 0x00080 | Encipher only |
| ckuDecipherOnly | 0x00100 | Decipher only |
| ckuServerAuthentication | 0x00200 | Server authentication |
| ckuClientAuthentication | 0x00400 | Client authentication |
| ckuCodeSigning | 0x00800 | Code signing |
| ckuEmailProtection | 0x01000 | Email protection |
| ckuTimeStamping | 0x02000 | Timestamping |
| ckuOCSPSigning | 0x04000 | OCSP signing |
| ckuSmartCardLogon | 0x08000 | Smartcard logon |
| ckuKeyPurposeClientAuth | 0x10000 | Kerberos - client authentication |
| ckuKeyPurposeKDC | 0x20000 | Kerberos - KDC |
KeyValid
boolean (read-only)
Default Value: False
Returns True if the certificate's key is cryptographically valid, and False otherwise.
OCSPLocations
String
Default Value: ""
Locations of OCSP (Online Certificate Status Protocol) services that can be used to check this certificate's validity, as recorded by the CA.
OCSPNoCheck
boolean
Default Value: False
Accessor to the value of the certificate's ocsp-no-check extension.
Origin
int (read-only)
Default Value: 0
Returns the origin of this certificate.
PolicyIDs
String
Default Value: ""
Contains identifiers (OIDs) of the applicable certificate policies.
The Certificate Policies extension identifies a sequence of policies under which the certificate has been issued, and which regulate its usage.
PrivateKeyBytes
byte[] (read-only)
Default Value: ""
Contains the certificate's private key. It is normal for this property to be empty if the private key is non-exportable.
PrivateKeyExists
boolean (read-only)
Default Value: False
Indicates whether the certificate has an associated private key.
PrivateKeyExtractable
boolean (read-only)
Default Value: False
Indicates whether the private key is extractable.
PublicKeyBytes
byte[] (read-only)
Default Value: ""
Contains the certificate's public key in DER format.
QualifiedStatements
int
Default Value: 0
Returns the qualified status of the certificate.
SelfSigned
boolean (read-only)
Default Value: False
Indicates whether the certificate is self-signed (root) or signed by an external CA.
SerialNumber
byte[]
Default Value: ""
Returns the certificate's serial number.
SigAlgorithm
String (read-only)
Default Value: ""
Indicates the algorithm that was used by the CA to sign this certificate.
Subject
String (read-only)
Default Value: ""
The common name of the certificate holder, typically an individual's name, a URL, an e-mail address, or a company name.
SubjectAlternativeName
String
Default Value: ""
Returns or sets the value of the Subject Alternative Name extension of the certificate.
SubjectKeyID
byte[]
Default Value: ""
Contains a unique identifier (fingerprint) of the certificate's private key.
Subject Key Identifier is a (non-critical) X.509 certificate extension which allows the identification of certificates containing a particular public key. In SecureBlackbox, the unique identifier is represented with a SHA1 hash of the bit string of the subject public key.
SubjectRDN
String
Default Value: ""
A collection of information, in the form of [OID, Value] pairs, uniquely identifying the certificate holder (subject).
ValidFrom
String
Default Value: ""
The time point at which the certificate becomes valid, in UTC.
ValidTo
String
Default Value: ""
The time point at which the certificate expires, in UTC.
Constructors
public Certificate( bytes, startIndex, count, password);
Loads the X.509 certificate from a memory buffer. Bytes is a buffer containing the raw certificate data. StartIndex and Count specify the starting position and number of bytes to be read from the buffer, respectively. Password is a password encrypting the certificate.
public Certificate( certBytes, certStartIndex, certCount, keyBytes, keyStartIndex, keyCount, password);
Loads the X.509 certificate from a memory buffer. CertBytes is a buffer containing the raw certificate data. CertStartIndex and CertCount specify the number of bytes to be read from the buffer, respectively. KeyBytes is a buffer containing the private key data. KeyStartIndex and KeyCount specify the starting position and number of bytes to be read from the buffer, respectively. Password is a password encrypting the certificate.
public Certificate( bytes, startIndex, count);
Loads the X.509 certificate from a memory buffer. Bytes is a buffer containing the raw certificate data. StartIndex and Count specify the starting position and number of bytes to be read from the buffer, respectively.
public Certificate( path, password);
Loads the X.509 certificate from a file. Path specifies the full path to the file containing the certificate data. Password is a password encrypting the certificate.
public Certificate( certPath, keyPath, password);
Loads the X.509 certificate from a file. CertPath specifies the full path to the file containing the certificate data. KeyPath specifies the full path to the file containing the private key. Password is a password encrypting the certificate.
public Certificate( path);
Loads the X.509 certificate from a file. Path specifies the full path to the file containing the certificate data.
public Certificate( stream);
Loads the X.509 certificate from a stream. Stream is a stream containing the certificate data.
public Certificate( stream, password);
Loads the X.509 certificate from a stream. Stream is a stream containing the certificate data. Password is a password encrypting the certificate.
public Certificate( certStream, keyStream, password);
Loads the X.509 certificate from a stream. CertStream is a stream containing the certificate data. KeyStream is a stream containing the private key. Password is a password encrypting the certificate.
public Certificate();
Creates a new object with default field values.
ExternalCrypto Type
Specifies the parameters of external cryptographic calls.
Remarks
External cryptocalls are used in a Distributed Cryptography (DC) subsystem, which allows the delegation of security operations to the remote agent. For instance, it can be used to compute the signature value on the server, while retaining the client's private key locally.
Fields
AsyncDocumentID
String
Default Value: ""
Specifies an optional document ID for SignAsyncBegin() and SignAsyncEnd() calls.
Use this property when working with multi-signature DCAuth requests and responses to uniquely identify documents signed within a larger batch. On the completion stage, this value helps the signing component identify the correct signature in the returned batch of responses.
If using batched requests, make sure to set this property to the same value on both the pre-signing (SignAsyncBegin) and completion (SignAsyncEnd) stages.
CustomParams
String
Default Value: ""
Custom parameters to be passed to the signing service (uninterpreted).
Data
String
Default Value: ""
Additional data to be included in the async state and mirrored back by the requestor.
ExternalHashCalculation
boolean
Default Value: False
Specifies whether the message hash is to be calculated at the external endpoint. Please note that this mode is not supported by the DCAuth class.
If set to true, the class will pass a few kilobytes of to-be-signed data from the document to the OnExternalSign event. This only applies when SignExternal() is called.
HashAlgorithm
String
Default Value: "SHA256"
Specifies the request's signature hash algorithm.
| SB_HASH_ALGORITHM_SHA1 | SHA1 | |
| SB_HASH_ALGORITHM_SHA224 | SHA224 | |
| SB_HASH_ALGORITHM_SHA256 | SHA256 | |
| SB_HASH_ALGORITHM_SHA384 | SHA384 | |
| SB_HASH_ALGORITHM_SHA512 | SHA512 | |
| SB_HASH_ALGORITHM_MD2 | MD2 | |
| SB_HASH_ALGORITHM_MD4 | MD4 | |
| SB_HASH_ALGORITHM_MD5 | MD5 | |
| SB_HASH_ALGORITHM_RIPEMD160 | RIPEMD160 | |
| SB_HASH_ALGORITHM_CRC32 | CRC32 | |
| SB_HASH_ALGORITHM_SSL3 | SSL3 | |
| SB_HASH_ALGORITHM_GOST_R3411_1994 | GOST1994 | |
| SB_HASH_ALGORITHM_WHIRLPOOL | WHIRLPOOL | |
| SB_HASH_ALGORITHM_POLY1305 | POLY1305 | |
| SB_HASH_ALGORITHM_SHA3_224 | SHA3_224 | |
| SB_HASH_ALGORITHM_SHA3_256 | SHA3_256 | |
| SB_HASH_ALGORITHM_SHA3_384 | SHA3_384 | |
| SB_HASH_ALGORITHM_SHA3_512 | SHA3_512 | |
| SB_HASH_ALGORITHM_BLAKE2S_128 | BLAKE2S_128 | |
| SB_HASH_ALGORITHM_BLAKE2S_160 | BLAKE2S_160 | |
| SB_HASH_ALGORITHM_BLAKE2S_224 | BLAKE2S_224 | |
| SB_HASH_ALGORITHM_BLAKE2S_256 | BLAKE2S_256 | |
| SB_HASH_ALGORITHM_BLAKE2B_160 | BLAKE2B_160 | |
| SB_HASH_ALGORITHM_BLAKE2B_256 | BLAKE2B_256 | |
| SB_HASH_ALGORITHM_BLAKE2B_384 | BLAKE2B_384 | |
| SB_HASH_ALGORITHM_BLAKE2B_512 | BLAKE2B_512 | |
| SB_HASH_ALGORITHM_SHAKE_128 | SHAKE_128 | |
| SB_HASH_ALGORITHM_SHAKE_256 | SHAKE_256 | |
| SB_HASH_ALGORITHM_SHAKE_128_LEN | SHAKE_128_LEN | |
| SB_HASH_ALGORITHM_SHAKE_256_LEN | SHAKE_256_LEN |
KeyID
String
Default Value: ""
The ID of the pre-shared key used for DC request authentication.
Asynchronous DCAuth-driven communication requires that parties authenticate each other with a secret pre-shared cryptographic key. This provides an extra protection layer for the protocol and diminishes the risk of the private key becoming abused by foreign parties. Use this property to provide the pre-shared key identifier, and use KeySecret to pass the key itself.
The same KeyID/KeySecret pair should be used on the DCAuth side for the signing requests to be accepted.
Note: The KeyID/KeySecret scheme is very similar to the AuthKey scheme used in various Cloud service providers to authenticate users.
Example:
signer.ExternalCrypto.KeyID = "MainSigningKey";
signer.ExternalCrypto.KeySecret = "abcdef0123456789";
KeySecret
String
Default Value: ""
The pre-shared key used for DC request authentication. This key must be set and match the key used by the DCAuth counterpart for the scheme to work.
Read more about configuring authentication in the KeyID topic.
Method
int
Default Value: 0
Specifies the asynchronous signing method. This is typically defined by the DC server capabilities and setup.
Available options:
| asmdPKCS1 | 0 |
| asmdPKCS7 | 1 |
Mode
int
Default Value: 0
Specifies the external cryptography mode.
Available options:
| ecmDefault | The default value (0) |
| ecmDisabled | Do not use DC or external signing (1) |
| ecmGeneric | Generic external signing with the OnExternalSign event (2) |
| ecmDCAuth | DCAuth signing (3) |
| ecmDCAuthJSON | DCAuth signing in JSON format (4) |
PublicKeyAlgorithm
String
Default Value: ""
Provide the public key algorithm here if the certificate is not available on the pre-signing stage.
| SB_CERT_ALGORITHM_ID_RSA_ENCRYPTION | rsaEncryption | |
| SB_CERT_ALGORITHM_MD2_RSA_ENCRYPTION | md2withRSAEncryption | |
| SB_CERT_ALGORITHM_MD5_RSA_ENCRYPTION | md5withRSAEncryption | |
| SB_CERT_ALGORITHM_SHA1_RSA_ENCRYPTION | sha1withRSAEncryption | |
| SB_CERT_ALGORITHM_ID_DSA | id-dsa | |
| SB_CERT_ALGORITHM_ID_DSA_SHA1 | id-dsa-with-sha1 | |
| SB_CERT_ALGORITHM_DH_PUBLIC | dhpublicnumber | |
| SB_CERT_ALGORITHM_SHA224_RSA_ENCRYPTION | sha224WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA256_RSA_ENCRYPTION | sha256WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA384_RSA_ENCRYPTION | sha384WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA512_RSA_ENCRYPTION | sha512WithRSAEncryption | |
| SB_CERT_ALGORITHM_ID_RSAPSS | id-RSASSA-PSS | |
| SB_CERT_ALGORITHM_ID_RSAOAEP | id-RSAES-OAEP | |
| SB_CERT_ALGORITHM_RSASIGNATURE_RIPEMD160 | ripemd160withRSA | |
| SB_CERT_ALGORITHM_ID_ELGAMAL | elGamal | |
| SB_CERT_ALGORITHM_SHA1_ECDSA | ecdsa-with-SHA1 | |
| SB_CERT_ALGORITHM_RECOMMENDED_ECDSA | ecdsa-recommended | |
| SB_CERT_ALGORITHM_SHA224_ECDSA | ecdsa-with-SHA224 | |
| SB_CERT_ALGORITHM_SHA256_ECDSA | ecdsa-with-SHA256 | |
| SB_CERT_ALGORITHM_SHA384_ECDSA | ecdsa-with-SHA384 | |
| SB_CERT_ALGORITHM_SHA512_ECDSA | ecdsa-with-SHA512 | |
| SB_CERT_ALGORITHM_EC | id-ecPublicKey | |
| SB_CERT_ALGORITHM_SPECIFIED_ECDSA | ecdsa-specified | |
| SB_CERT_ALGORITHM_GOST_R3410_1994 | id-GostR3410-94 | |
| SB_CERT_ALGORITHM_GOST_R3410_2001 | id-GostR3410-2001 | |
| SB_CERT_ALGORITHM_GOST_R3411_WITH_R3410_1994 | id-GostR3411-94-with-GostR3410-94 | |
| SB_CERT_ALGORITHM_GOST_R3411_WITH_R3410_2001 | id-GostR3411-94-with-GostR3410-2001 | |
| SB_CERT_ALGORITHM_SHA1_ECDSA_PLAIN | ecdsa-plain-SHA1 | |
| SB_CERT_ALGORITHM_SHA224_ECDSA_PLAIN | ecdsa-plain-SHA224 | |
| SB_CERT_ALGORITHM_SHA256_ECDSA_PLAIN | ecdsa-plain-SHA256 | |
| SB_CERT_ALGORITHM_SHA384_ECDSA_PLAIN | ecdsa-plain-SHA384 | |
| SB_CERT_ALGORITHM_SHA512_ECDSA_PLAIN | ecdsa-plain-SHA512 | |
| SB_CERT_ALGORITHM_RIPEMD160_ECDSA_PLAIN | ecdsa-plain-RIPEMD160 | |
| SB_CERT_ALGORITHM_WHIRLPOOL_RSA_ENCRYPTION | whirlpoolWithRSAEncryption | |
| SB_CERT_ALGORITHM_ID_DSA_SHA224 | id-dsa-with-sha224 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA256 | id-dsa-with-sha256 | |
| SB_CERT_ALGORITHM_SHA3_224_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-512 | |
| SB_CERT_ALGORITHM_SHA3_224_ECDSA | id-ecdsa-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_ECDSA | id-ecdsa-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_ECDSA | id-ecdsa-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_ECDSA | id-ecdsa-with-sha3-512 | |
| SB_CERT_ALGORITHM_SHA3_224_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-512 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA3_224 | id-dsa-with-sha3-224 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA3_256 | id-dsa-with-sha3-256 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b512 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_ECDSA | id-ecdsa-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_ECDSA | id-ecdsa-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_ECDSA | id-ecdsa-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_ECDSA | id-ecdsa-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_ECDSA | id-ecdsa-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_ECDSA | id-ecdsa-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_ECDSA | id-ecdsa-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_ECDSA | id-ecdsa-with-blake2b512 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b512 | |
| SB_CERT_ALGORITHM_ID_DSA_BLAKE2S_224 | id-dsa-with-blake2s224 | |
| SB_CERT_ALGORITHM_ID_DSA_BLAKE2S_256 | id-dsa-with-blake2s256 | |
| SB_CERT_ALGORITHM_EDDSA_ED25519 | id-Ed25519 | |
| SB_CERT_ALGORITHM_EDDSA_ED448 | id-Ed448 | |
| SB_CERT_ALGORITHM_EDDSA_ED25519_PH | id-Ed25519ph | |
| SB_CERT_ALGORITHM_EDDSA_ED448_PH | id-Ed448ph | |
| SB_CERT_ALGORITHM_EDDSA | id-EdDSA | |
| SB_CERT_ALGORITHM_EDDSA_SIGNATURE | id-EdDSA-sig |
Constructors
public ExternalCrypto();
Creates a new ExternalCrypto object with default field values.
ProxySettings Type
A container for proxy server settings.
Remarks
This type exposes a collection of properties for tuning up the proxy server configuration.
Fields
Address
String
Default Value: ""
The IP address of the proxy server.
Authentication
int
Default Value: 0
The authentication type used by the proxy server.
| patNoAuthentication | 0 |
| patBasic | 1 |
| patDigest | 2 |
| patNTLM | 3 |
Password
String
Default Value: ""
The password to authenticate to the proxy server.
Port
int
Default Value: 0
The port on the proxy server to connect to.
ProxyType
int
Default Value: 0
The type of the proxy server.
The WebTunnel proxy is also known as HTTPS proxy. Unlike HTTP proxy, HTTPS proxy (WebTunnel) provides end-to-end security.
| cptNone | 0 |
| cptSocks4 | 1 |
| cptSocks5 | 2 |
| cptWebTunnel | 3 |
| cptHTTP | 4 |
RequestHeaders
String
Default Value: ""
Contains HTTP request headers for WebTunnel and HTTP proxy.
ResponseBody
String
Default Value: ""
Contains the HTTP or HTTPS (WebTunnel) proxy response body.
ResponseHeaders
String
Default Value: ""
Contains response headers received from an HTTP or HTTPS (WebTunnel) proxy server.
UseIPv6
boolean
Default Value: False
Specifies whether IPv6 should be used when connecting through the proxy.
UseProxy
boolean
Default Value: False
Enables or disables proxy-driven connection.
Username
String
Default Value: ""
Specifies the username credential for proxy authentication.
Constructors
public ProxySettings();
Creates a new ProxySettings object.
SocketSettings Type
A container for the socket settings.
Remarks
This type is a container for socket-layer parameters.
Fields
DNSMode
int
Default Value: 0
Selects the DNS resolver to use: the component's (secure) built-in one, or the one provided by the system.
| dmAuto | 0 |
| dmPlatform | 1 |
| dmOwn | 2 |
| dmOwnSecure | 3 |
DNSPort
int
Default Value: 0
Specifies the port number to be used for sending queries to the DNS server.
DNSQueryTimeout
int
Default Value: 0
The timeout (in milliseconds) for each DNS query. The value of 0 indicates an infinite timeout.
DNSServers
String
Default Value: ""
The addresses of DNS servers to use for address resolution, separated by commas or semicolons.
DNSTotalTimeout
int
Default Value: 0
The timeout (in milliseconds) for the whole resolution process. The value of 0 indicates an infinite timeout.
IncomingSpeedLimit
int
Default Value: 0
The maximum number of bytes to read from the socket, per second.
LocalAddress
String
Default Value: ""
The local network interface to bind the socket to.
LocalPort
int
Default Value: 0
The local port number to bind the socket to.
OutgoingSpeedLimit
int
Default Value: 0
The maximum number of bytes to write to the socket, per second.
Timeout
int
Default Value: 60000
The maximum period of waiting, in milliseconds, after which the socket operation is considered unsuccessful.
If Timeout is set to 0, a socket operation will expire after the system-default timeout (2 hrs 8 min for TCP stack).
UseIPv6
boolean
Default Value: False
Enables or disables IP protocol version 6.
Constructors
public SocketSettings();
Creates a new SocketSettings object.
TLSSettings Type
A container for TLS connection settings.
Remarks
The TLS (Transport Layer Security) protocol provides security for information exchanged over insecure connections such as TCP/IP.
Fields
AutoValidateCertificates
boolean
Default Value: True
Specifies whether server-side TLS certificates should be validated automatically using internal validation rules.
BaseConfiguration
int
Default Value: 0
Selects the base configuration for the TLS settings. Several profiles are offered and tuned up for different purposes, such as high security or higher compatibility.
| stpcDefault | 0 | |
| stpcCompatible | 1 | |
| stpcComprehensiveInsecure | 2 | |
| stpcHighlySecure | 3 |
Ciphersuites
String
Default Value: ""
A list of ciphersuites separated with commas or semicolons. Each ciphersuite in the list may be prefixed with a minus sign (-) to indicate that the ciphersuite should be disabled rather than enabled. Besides the specific ciphersuite modifiers, this property supports the all (and -all) aliases, allowing all ciphersuites to be blanketly enabled or disabled at once.
Note: the list of ciphersuites provided to this property alters the baseline list of ciphersuites as defined by BaseConfiguration. Remember to start your ciphersuite string with -all; if you need to only enable a specific fixed set of ciphersuites. The list of supported ciphersuites is provided below:
- NULL_NULL_NULL
- RSA_NULL_MD5
- RSA_NULL_SHA
- RSA_RC4_MD5
- RSA_RC4_SHA
- RSA_RC2_MD5
- RSA_IDEA_MD5
- RSA_IDEA_SHA
- RSA_DES_MD5
- RSA_DES_SHA
- RSA_3DES_MD5
- RSA_3DES_SHA
- RSA_AES128_SHA
- RSA_AES256_SHA
- DH_DSS_DES_SHA
- DH_DSS_3DES_SHA
- DH_DSS_AES128_SHA
- DH_DSS_AES256_SHA
- DH_RSA_DES_SHA
- DH_RSA_3DES_SHA
- DH_RSA_AES128_SHA
- DH_RSA_AES256_SHA
- DHE_DSS_DES_SHA
- DHE_DSS_3DES_SHA
- DHE_DSS_AES128_SHA
- DHE_DSS_AES256_SHA
- DHE_RSA_DES_SHA
- DHE_RSA_3DES_SHA
- DHE_RSA_AES128_SHA
- DHE_RSA_AES256_SHA
- DH_ANON_RC4_MD5
- DH_ANON_DES_SHA
- DH_ANON_3DES_SHA
- DH_ANON_AES128_SHA
- DH_ANON_AES256_SHA
- RSA_RC2_MD5_EXPORT
- RSA_RC4_MD5_EXPORT
- RSA_DES_SHA_EXPORT
- DH_DSS_DES_SHA_EXPORT
- DH_RSA_DES_SHA_EXPORT
- DHE_DSS_DES_SHA_EXPORT
- DHE_RSA_DES_SHA_EXPORT
- DH_ANON_RC4_MD5_EXPORT
- DH_ANON_DES_SHA_EXPORT
- RSA_CAMELLIA128_SHA
- DH_DSS_CAMELLIA128_SHA
- DH_RSA_CAMELLIA128_SHA
- DHE_DSS_CAMELLIA128_SHA
- DHE_RSA_CAMELLIA128_SHA
- DH_ANON_CAMELLIA128_SHA
- RSA_CAMELLIA256_SHA
- DH_DSS_CAMELLIA256_SHA
- DH_RSA_CAMELLIA256_SHA
- DHE_DSS_CAMELLIA256_SHA
- DHE_RSA_CAMELLIA256_SHA
- DH_ANON_CAMELLIA256_SHA
- PSK_RC4_SHA
- PSK_3DES_SHA
- PSK_AES128_SHA
- PSK_AES256_SHA
- DHE_PSK_RC4_SHA
- DHE_PSK_3DES_SHA
- DHE_PSK_AES128_SHA
- DHE_PSK_AES256_SHA
- RSA_PSK_RC4_SHA
- RSA_PSK_3DES_SHA
- RSA_PSK_AES128_SHA
- RSA_PSK_AES256_SHA
- RSA_SEED_SHA
- DH_DSS_SEED_SHA
- DH_RSA_SEED_SHA
- DHE_DSS_SEED_SHA
- DHE_RSA_SEED_SHA
- DH_ANON_SEED_SHA
- SRP_SHA_3DES_SHA
- SRP_SHA_RSA_3DES_SHA
- SRP_SHA_DSS_3DES_SHA
- SRP_SHA_AES128_SHA
- SRP_SHA_RSA_AES128_SHA
- SRP_SHA_DSS_AES128_SHA
- SRP_SHA_AES256_SHA
- SRP_SHA_RSA_AES256_SHA
- SRP_SHA_DSS_AES256_SHA
- ECDH_ECDSA_NULL_SHA
- ECDH_ECDSA_RC4_SHA
- ECDH_ECDSA_3DES_SHA
- ECDH_ECDSA_AES128_SHA
- ECDH_ECDSA_AES256_SHA
- ECDHE_ECDSA_NULL_SHA
- ECDHE_ECDSA_RC4_SHA
- ECDHE_ECDSA_3DES_SHA
- ECDHE_ECDSA_AES128_SHA
- ECDHE_ECDSA_AES256_SHA
- ECDH_RSA_NULL_SHA
- ECDH_RSA_RC4_SHA
- ECDH_RSA_3DES_SHA
- ECDH_RSA_AES128_SHA
- ECDH_RSA_AES256_SHA
- ECDHE_RSA_NULL_SHA
- ECDHE_RSA_RC4_SHA
- ECDHE_RSA_3DES_SHA
- ECDHE_RSA_AES128_SHA
- ECDHE_RSA_AES256_SHA
- ECDH_ANON_NULL_SHA
- ECDH_ANON_RC4_SHA
- ECDH_ANON_3DES_SHA
- ECDH_ANON_AES128_SHA
- ECDH_ANON_AES256_SHA
- RSA_NULL_SHA256
- RSA_AES128_SHA256
- RSA_AES256_SHA256
- DH_DSS_AES128_SHA256
- DH_RSA_AES128_SHA256
- DHE_DSS_AES128_SHA256
- DHE_RSA_AES128_SHA256
- DH_DSS_AES256_SHA256
- DH_RSA_AES256_SHA256
- DHE_DSS_AES256_SHA256
- DHE_RSA_AES256_SHA256
- DH_ANON_AES128_SHA256
- DH_ANON_AES256_SHA256
- RSA_AES128_GCM_SHA256
- RSA_AES256_GCM_SHA384
- DHE_RSA_AES128_GCM_SHA256
- DHE_RSA_AES256_GCM_SHA384
- DH_RSA_AES128_GCM_SHA256
- DH_RSA_AES256_GCM_SHA384
- DHE_DSS_AES128_GCM_SHA256
- DHE_DSS_AES256_GCM_SHA384
- DH_DSS_AES128_GCM_SHA256
- DH_DSS_AES256_GCM_SHA384
- DH_ANON_AES128_GCM_SHA256
- DH_ANON_AES256_GCM_SHA384
- ECDHE_ECDSA_AES128_SHA256
- ECDHE_ECDSA_AES256_SHA384
- ECDH_ECDSA_AES128_SHA256
- ECDH_ECDSA_AES256_SHA384
- ECDHE_RSA_AES128_SHA256
- ECDHE_RSA_AES256_SHA384
- ECDH_RSA_AES128_SHA256
- ECDH_RSA_AES256_SHA384
- ECDHE_ECDSA_AES128_GCM_SHA256
- ECDHE_ECDSA_AES256_GCM_SHA384
- ECDH_ECDSA_AES128_GCM_SHA256
- ECDH_ECDSA_AES256_GCM_SHA384
- ECDHE_RSA_AES128_GCM_SHA256
- ECDHE_RSA_AES256_GCM_SHA384
- ECDH_RSA_AES128_GCM_SHA256
- ECDH_RSA_AES256_GCM_SHA384
- PSK_AES128_GCM_SHA256
- PSK_AES256_GCM_SHA384
- DHE_PSK_AES128_GCM_SHA256
- DHE_PSK_AES256_GCM_SHA384
- RSA_PSK_AES128_GCM_SHA256
- RSA_PSK_AES256_GCM_SHA384
- PSK_AES128_SHA256
- PSK_AES256_SHA384
- PSK_NULL_SHA256
- PSK_NULL_SHA384
- DHE_PSK_AES128_SHA256
- DHE_PSK_AES256_SHA384
- DHE_PSK_NULL_SHA256
- DHE_PSK_NULL_SHA384
- RSA_PSK_AES128_SHA256
- RSA_PSK_AES256_SHA384
- RSA_PSK_NULL_SHA256
- RSA_PSK_NULL_SHA384
- RSA_CAMELLIA128_SHA256
- DH_DSS_CAMELLIA128_SHA256
- DH_RSA_CAMELLIA128_SHA256
- DHE_DSS_CAMELLIA128_SHA256
- DHE_RSA_CAMELLIA128_SHA256
- DH_ANON_CAMELLIA128_SHA256
- RSA_CAMELLIA256_SHA256
- DH_DSS_CAMELLIA256_SHA256
- DH_RSA_CAMELLIA256_SHA256
- DHE_DSS_CAMELLIA256_SHA256
- DHE_RSA_CAMELLIA256_SHA256
- DH_ANON_CAMELLIA256_SHA256
- ECDHE_ECDSA_CAMELLIA128_SHA256
- ECDHE_ECDSA_CAMELLIA256_SHA384
- ECDH_ECDSA_CAMELLIA128_SHA256
- ECDH_ECDSA_CAMELLIA256_SHA384
- ECDHE_RSA_CAMELLIA128_SHA256
- ECDHE_RSA_CAMELLIA256_SHA384
- ECDH_RSA_CAMELLIA128_SHA256
- ECDH_RSA_CAMELLIA256_SHA384
- RSA_CAMELLIA128_GCM_SHA256
- RSA_CAMELLIA256_GCM_SHA384
- DHE_RSA_CAMELLIA128_GCM_SHA256
- DHE_RSA_CAMELLIA256_GCM_SHA384
- DH_RSA_CAMELLIA128_GCM_SHA256
- DH_RSA_CAMELLIA256_GCM_SHA384
- DHE_DSS_CAMELLIA128_GCM_SHA256
- DHE_DSS_CAMELLIA256_GCM_SHA384
- DH_DSS_CAMELLIA128_GCM_SHA256
- DH_DSS_CAMELLIA256_GCM_SHA384
- DH_anon_CAMELLIA128_GCM_SHA256
- DH_anon_CAMELLIA256_GCM_SHA384
- ECDHE_ECDSA_CAMELLIA128_GCM_SHA256
- ECDHE_ECDSA_CAMELLIA256_GCM_SHA384
- ECDH_ECDSA_CAMELLIA128_GCM_SHA256
- ECDH_ECDSA_CAMELLIA256_GCM_SHA384
- ECDHE_RSA_CAMELLIA128_GCM_SHA256
- ECDHE_RSA_CAMELLIA256_GCM_SHA384
- ECDH_RSA_CAMELLIA128_GCM_SHA256
- ECDH_RSA_CAMELLIA256_GCM_SHA384
- PSK_CAMELLIA128_GCM_SHA256
- PSK_CAMELLIA256_GCM_SHA384
- DHE_PSK_CAMELLIA128_GCM_SHA256
- DHE_PSK_CAMELLIA256_GCM_SHA384
- RSA_PSK_CAMELLIA128_GCM_SHA256
- RSA_PSK_CAMELLIA256_GCM_SHA384
- PSK_CAMELLIA128_SHA256
- PSK_CAMELLIA256_SHA384
- DHE_PSK_CAMELLIA128_SHA256
- DHE_PSK_CAMELLIA256_SHA384
- RSA_PSK_CAMELLIA128_SHA256
- RSA_PSK_CAMELLIA256_SHA384
- ECDHE_PSK_CAMELLIA128_SHA256
- ECDHE_PSK_CAMELLIA256_SHA384
- ECDHE_PSK_RC4_SHA
- ECDHE_PSK_3DES_SHA
- ECDHE_PSK_AES128_SHA
- ECDHE_PSK_AES256_SHA
- ECDHE_PSK_AES128_SHA256
- ECDHE_PSK_AES256_SHA384
- ECDHE_PSK_NULL_SHA
- ECDHE_PSK_NULL_SHA256
- ECDHE_PSK_NULL_SHA384
- ECDHE_RSA_CHACHA20_POLY1305_SHA256
- ECDHE_ECDSA_CHACHA20_POLY1305_SHA256
- DHE_RSA_CHACHA20_POLY1305_SHA256
- PSK_CHACHA20_POLY1305_SHA256
- ECDHE_PSK_CHACHA20_POLY1305_SHA256
- DHE_PSK_CHACHA20_POLY1305_SHA256
- RSA_PSK_CHACHA20_POLY1305_SHA256
- AES128_GCM_SHA256
- AES256_GCM_SHA384
- CHACHA20_POLY1305_SHA256
- AES128_CCM_SHA256
- AES128_CCM8_SHA256
ECCurves
String
Default Value: ""
Defines the elliptic curves to enable.
Extensions
String
Default Value: ""
Provides access to TLS extensions.
ForceResumeIfDestinationChanges
boolean
Default Value: False
Whether to force TLS session resumption when the destination address changes.
PreSharedIdentity
String
Default Value: ""
Defines the identity used when the PSK (Pre-Shared Key) key-exchange mechanism is negotiated.
PreSharedKey
String
Default Value: ""
Contains the pre-shared key for the PSK (Pre-Shared Key) key-exchange mechanism, encoded with base16.
PreSharedKeyCiphersuite
String
Default Value: ""
Defines the ciphersuite used for PSK (Pre-Shared Key) negotiation.
RenegotiationAttackPreventionMode
int
Default Value: 0
Selects the renegotiation attack prevention mechanism.
The following options are available:
| crapmCompatible | 0 | TLS 1.0 and 1.1 compatibility mode (renegotiation indication extension is disabled). |
| crapmStrict | 1 | Renegotiation attack prevention is enabled and enforced. |
| crapmAuto | 2 | Automatically choose whether to enable or disable renegotiation attack prevention. |
RevocationCheck
int
Default Value: 1
Specifies the kind(s) of revocation check to perform.
Revocation checking is necessary to ensure the integrity of the chain and obtain up-to-date certificate validity and trustworthiness information.
| crcNone | 0 | No revocation checking. |
| crcAuto | 1 | Automatic mode selection. Currently this maps to crcAnyOCSPOrCRL, but it may change in the future. |
| crcAllCRL | 2 | All provided CRL endpoints will be checked, and all checks must succeed. |
| crcAllOCSP | 3 | All provided OCSP endpoints will be checked, and all checks must succeed. |
| crcAllCRLAndOCSP | 4 | All provided CRL and OCSP endpoints will be checked, and all checks must succeed. |
| crcAnyCRL | 5 | All provided CRL endpoints will be checked, and at least one check must succeed. |
| crcAnyOCSP | 6 | All provided OCSP endpoints will be checked, and at least one check must succeed. |
| crcAnyCRLOrOCSP | 7 | All provided CRL and OCSP endpoints will be checked, and at least one check must succeed. CRL endpoints are checked first. |
| crcAnyOCSPOrCRL | 8 | All provided CRL and OCSP endpoints will be checked, and at least one check must succeed. OCSP endpoints are checked first. |
This setting controls the way the revocation checks are performed for every certificate in the chain. Typically certificates come with two types of revocation information sources: CRL (certificate revocation lists) and OCSP responders. CRLs are static objects periodically published by the CA at some online location. OCSP responders are active online services maintained by the CA that can provide up-to-date information on certificate statuses in near real time.
There are some conceptual differences between the two. CRLs are normally larger in size. Their use involves some latency because there is normally some delay between the time when a certificate was revoked and the time the subsequent CRL mentioning that is published. The benefits of CRL is that the same object can provide statuses for all certificates issued by a particular CA, and that the whole technology is much simpler than OCSP (and thus is supported by more CAs).
This setting lets you adjust the validation course by including or excluding certain types of revocation sources from the validation process. The crcAnyOCSPOrCRL setting (give preference to the faster OCSP route and only demand one source to succeed) is a good choice for most typical validation environments. The "crcAll*" modes are much stricter, and may be used in scenarios where bulletproof validity information is essential.
Note: If no CRL or OCSP endpoints are provided by the CA, the revocation check will be considered successful. This is because the CA chose not to supply revocation information for its certificates, meaning they are considered irrevocable.
Note: Within each of the above settings, if any retrieved CRL or OCSP response indicates that the certificate has been revoked, the revocation check fails.
SSLOptions
int
Default Value: 16
Various SSL (TLS) protocol options, set of
| cssloExpectShutdownMessage | 0x001 | Wait for the close-notify message when shutting down the connection |
| cssloOpenSSLDTLSWorkaround | 0x002 | (DEPRECATED) Use a DTLS version workaround when talking to very old OpenSSL versions |
| cssloDisableKexLengthAlignment | 0x004 | Do not align the client-side PMS by the RSA modulus size. It is unlikely that you will ever need to adjust it. |
| cssloForceUseOfClientCertHashAlg | 0x008 | Enforce the use of the client certificate hash algorithm. It is unlikely that you will ever need to adjust it. |
| cssloAutoAddServerNameExtension | 0x010 | Automatically add the server name extension when known |
| cssloAcceptTrustedSRPPrimesOnly | 0x020 | Accept trusted SRP primes only |
| cssloDisableSignatureAlgorithmsExtension | 0x040 | Disable (do not send) the signature algorithms extension. It is unlikely that you will ever need to adjust it. |
| cssloIntolerateHigherProtocolVersions | 0x080 | (server option) Do not allow fallback from TLS versions higher than currently enabled |
| cssloStickToPrefCertHashAlg | 0x100 | Stick to preferred certificate hash algorithms |
| cssloNoImplicitTLS12Fallback | 0x200 | Disable implicit TLS 1.3 to 1.2 fallbacks |
| cssloUseHandshakeBatches | 0x400 | Send the handshake message as large batches rather than individually |
TLSMode
int
Default Value: 0
Specifies the TLS mode to use.
| smDefault | 0 | |
| smNoTLS | 1 | Do not use TLS |
| smExplicitTLS | 2 | Connect to the server without any encryption and then request an SSL session. |
| smImplicitTLS | 3 | Connect to the specified port, and establish the SSL session at once. |
| smMixedTLS | 4 | Connect to the specified port, and establish the SSL session at once, but allow plain data. |
UseExtendedMasterSecret
boolean
Default Value: False
Enables the Extended Master Secret Extension, as defined in RFC 7627.
UseSessionResumption
boolean
Default Value: False
Enables or disables the TLS session resumption capability.
Versions
int
Default Value: 16
The SSL/TLS versions to enable by default.
| csbSSL2 | 0x01 | SSL 2 |
| csbSSL3 | 0x02 | SSL 3 |
| csbTLS1 | 0x04 | TLS 1.0 |
| csbTLS11 | 0x08 | TLS 1.1 |
| csbTLS12 | 0x10 | TLS 1.2 |
| csbTLS13 | 0x20 | TLS 1.3 |
Constructors
public TLSSettings();
Creates a new TLSSettings object.
Config Settings (Dcauth Class)
The class accepts one or more of the following configuration settings. Configuration settings are similar in functionality to properties, but they are rarely used. In order to avoid "polluting" the property namespace of the class, access to these internal properties is provided through the Config method.DCAuth Config Settings
(obsolete) The DataURL parameter to pass to the signer.
(obsolete) The GoURL parameter to pass to the signer.
(obsolete) The RequireDefinedSignCert parameter to pass to the signer.
Use this property to specify the parameters of the algorithm scheme if needed.
This setting is used to provide parameters for some cryptographic schemes. Use the Name1=Value1;Name2=Value2;... syntax to encode the parameters. For example: Scheme=PSS;SaltSize=32;TrailerField=1.
(obsolete) The SessionID parameter to pass to the signer.
(obsolete) The TokenName parameter to pass to the signer.
(obsolete) The TokensLibraries parameter to pass to the signer.
Base Config Settings
This global property enables or disables private key material check before each signing operation. This slows down performance a bit, but prevents a selection of attacks on RSA keys where keys with unknown origins are used.
You can switch this property off to improve performance if your project only uses known, good private keys.
Set this property to enable or disable cookies caching for the class.
Supported values are:
| off | No caching (default) | |
| local | Local caching | |
| global | Global caching |
Use this property to get cookies from the internal cookie storage of the class and/or restore them back between application sessions.
This global property sets the default number of iterations for all supported key derivation algorithms. Note that you can provide the required number of iterations by using properties of the relevant key generation component; this global setting is used in scenarios where specific iteration count is not or cannot be provided.
This global property enables or disables support for finite field DHE key exchange methods in TLS clients. FF DHE is a slower algorithm if compared to EC DHE; enabling it may result in slower connections.
This setting only applies to sessions negotiated with TLS version 1.3.
Use this property to get cookies from the GLOBAL cookie storage or restore them back between application sessions. These cookies will be used by all the classes that have its CookieCaching property set to "global".
This global setting defines the User-Agent field of the HTTP request provides information about the software that initiates the request. This value will be used by all the HTTP clients including the ones used internally in other classes.
Contains a comma-separated list of values that specifies where debug log should be dumped.
Supported values are:
| file | File | |
| console | Console | |
| systemlog | System Log (supported for Android only) | |
| debugger | Debugger (supported for VCL for Windows and .Net) |
Contains a comma-separated list of values that specifies which debug log details to dump.
Supported values are:
| time | Current time | |
| level | Level | |
| package | Package name | |
| module | Module name | |
| class | Class name | |
| method | Method name | |
| threadid | Thread Id | |
| contenttype | Content type | |
| content | Content | |
| all | All details |
Use this property to provide a path to the log file.
Contains a comma-separated list of value pairs ("name:value") that describe filters.
Supported filter names are:
| exclude-package | Exclude a package specified in the value | |
| exclude-module | Exclude a module specified in the value | |
| exclude-class | Exclude a class specified in the value | |
| exclude-method | Exclude a method specified in the value | |
| include-package | Include a package specified in the value | |
| include-module | Include a module specified in the value | |
| include-class | Include a class specified in the value | |
| include-method | Include a method specified in the value |
Use this property to set the log flush mode. The following values are defined:
| none | No flush (caching only) | |
| immediate | Immediate flush (real-time logging) | |
| maxcount | Flush cached entries upon reaching LogMaxEventCount entries in the cache. |
Use this property to provide the desired debug log level.
Supported values are:
| none | None (by default) | |
| fatal | Severe errors that cause premature termination. | |
| error | Other runtime errors or unexpected conditions. | |
| warning | Use of deprecated APIs, poor use of API, 'almost' errors, other runtime situations that are undesirable or unexpected, but not necessarily "wrong". | |
| info | Interesting runtime events (startup/shutdown). | |
| debug | Detailed information on flow of through the system. | |
| trace | More detailed information. |
Use this property to specify the log event number threshold. This threshold may have different effects, depending on the rotation setting and/or the flush mode.
The default value of this setting is 100.
Use this property to set the log rotation mode. The following values are defined:
| none | No rotation | |
| deleteolder | Delete older entries from the cache upon reaching LogMaxEventCount | |
| keepolder | Keep older entries in the cache upon reaching LogMaxEventCount (newer entries are discarded) |
This global property limits the maximal allowed length for ASN.1 tag data for non-content-carrying structures, such as certificates, CRLs, or timestamps. It does not affect structures that can carry content, such as CMS/CAdES messages. This is a security property aiming at preventing DoS attacks.
This global property limits the maximal depth of ASN.1 trees that the component can handle without throwing an error. This is a security property aiming at preventing DoS attacks.
This global setting defines the hash algorithm to use in OCSP requests during chain validation. Some OCSP responders can only use older algorithms, in which case setting this property to SHA1 may be helpful.
Set this property to enable or disable static DNS rules for the class. Works only if UseOwnDNSResolver is set to true.
Supported values are:
| none | No static DNS rules (default) | |
| local | Local static DNS rules | |
| global | Global static DNS rules |
Use this property to get or set an IP address for the specified domain name in the internal (of the class) or global DNS rules storage depending on the StaticDNS value. The type of the IP address (IPv4 or IPv6) is determined automatically. If both addresses are available, they are devided by the | (pipe) character.
Use this property to get static DNS rules from the current rules storage or restore them back between application sessions. If StaticDNS of the class is set to "local", the property returns/restores the rules from/to the internal storage of the class. If StaticDNS of the class is set to "global", the property returns/restores the rules from/to the GLOBAL storage. The rules list is returned and accepted in JSON format.
Use this config property to store any custom data.
Use this property to limit the search of chached TLS sessions to the specified group. Sessions from other groups will be ignored. By default, all sessions are cached with an empty group name and available to all the classes.
Use this property to specify how much time the TLS session should be kept in the session cache. After this time, the session expires and will be automatically removed from the cache. Default value is 300 seconds (5 minutes).
Use this property to specify the time interval of purging the expired TLS sessions from the session cache. Default value is 60 seconds (1 minute).
Set this global property to false to force all the client components to use the DNS resolver provided by the target OS instead of using own one.
Set this global property to false to make each validation run use its own copy of system certificate stores.
This global setting defines who is responsible for performing RSA-OAEP and RSA-PSS computations where the private key is stored in a Windows system store and is exportable. If set to true, SBB will delegate the computations to Windows via a CryptoAPI call. Otherwise, it will export the key material and perform the computations using its own OAEP/PSS implementation.
This setting only applies to certificates originating from a Windows system store.
Use this global property to enable or disable the use of operating system-driven pseudorandom number generation.