SAMLSPServer Component
Properties Methods Events Config Settings Errors
The SAMLSPServer component represents a SAML service provider
Syntax
nsoftware.SecureBlackbox.SAMLSPServer
Remarks
The Service Provider in the SAML exchange flow represents the web server that receives and accepts authentication assertions issued by the Identity Provider for single sign-on (SSO). Most commonly, an SP server is part of the application responsible for communicating with an Identity Provider to establish the authenticity of application users.
SAMLSPServer provides easy means of integrating the SAML Service Provider functionality into your application. It presents a fully-features SP endpoint with its own HTTP(S) and assertion validation engines.
Please find below a step-by-step guide on setting up your own SAML SP endpoint.
- Register the IdP metadata using the ImportSettings method.
Most IDPs let you download their metadata in XML format. The metadata file contains general
parameters of the IdP endpoint, such as its web address and algorithm requirements.
server.ImportSettings(metadataBytes, false); // contains "<?xml version="1.0"?><md:EntityDescriptor ID="ab12" ... </md:EntityDescriptor>"; - Configure the main server capabilities:
// public server endpoint (use "https://" and/or port 443 if required) server.URL = "http://sp.myapp.com"; server.Port = 80; // IdP triggers this URL to pull metadata server.MetadataURL = '/sp/metadata'; // ACS is th "main" SP endpoint that receives assertions from the IdP server.AssertionConsumerService = '/sp/AssertionConsumerService'; server.SPToIDPBinding = csbtRedirect; // the SP will use HTTP redirect to forward the browser to the IdP when required server.AssertionConsumerServiceBindings = 'POST'; // and we want the IdP to use POST to submit its assertions server.PreferredIDPToSPBinding = csbtPOST; // Single logout service setup server.SingleLogoutService = '/sp/SingleLogoutService'; server.SingleLogoutServiceBindings = 'Redirect,POST,Artifact'; server.LogoutPage = '/sp/logout'; server.RedirectOnLogoutPage = 'https://www.nsoftware.com'; // The document root of the server on the local system server.BaseDir = "D:\\Inetpub\\SAMLSP"; // Security parameters: indicating that we want to sign both // the metadata and the requests server.SignAuthnRequests = true; server.SignMetadata = true; // We need to attach certificates to be able to sign. // Assume we have loaded our signing certificate into // a CertificateManager object. server.SigningCertificate = mgr.Certificate; server.MetaSigningCertificate = mgr.Certificate; - Personalize the server:
server.Config("OrganizationName=My Organization Ltd"); server.Config("OrganizationDisplayName=My Organization Pet Supplies"); server.Config("OrganizationURL=http://myorg.com"); server.Config("SigDigestMethod=http://www.w3.org/2001/04/xmlenc#sha256"); server.Config("SigMethod=http://www.w3.org/2001/04/xmldsig-more#rsa-sha256"); server.Config("WantAssertionsSigned=true"); - Optionally, save metadata to an XML file. This will let you send/upload it to the IdP,
so they could set your SP up. Some IdPs can download the metadata right from your SP
using the MetadataURL that you've provided above, in which case saving it to a file
is not necessary.
server.SaveMetadata("my_metadata.xml");
server.Start();
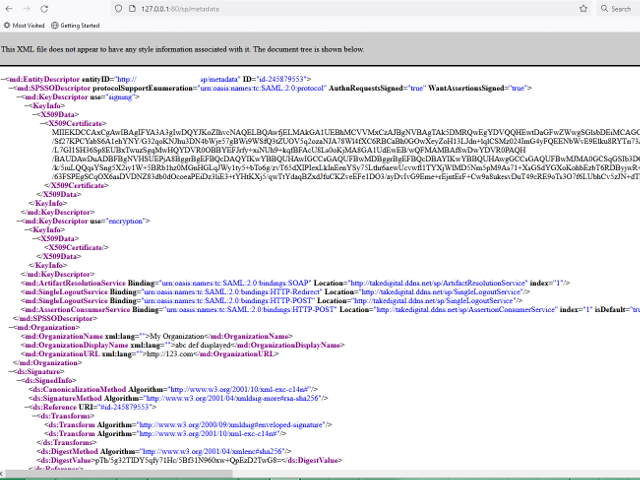
The server should now be running on the local system, listening to incoming connections on the port that you
have specified above (80). Use your browser to check if the server is responding by navigating
to the metadata URL (http://127.0.0.1:80/sp/metadata). If the server has been set up right,
you should see something like this:
Now let us actually try to use the SAML functionality. Copy an arbitrary file - for example, a recent photo of your cat - to the directory you provided earlier via the BaseDir property (D:\Inetpub\SAMLSP). Having copied the file (suppose it is called clifford.jpg), try to access it in your browser by navigating to http://127.0.0.1:80/clifford.jpg.
This is where SAML kicks in. Since you are not authenticated for the SP server yet (we have just launched it, so no one is), the server redirects your browser to the IdP endpoint for authentication. The address of the IdP is taken from the their_metadata.xml file that you have loaded at the very beginning.
Note: you can configure which resources to restrict access to using the ProtectedResources property. If ProtectedResources is empty, the server considers all the files in BaseDir and its subfolders to be protected.
It is now the IdP services turn to authenticate you. Most IdPs on this stage will present you with a login form. Yet, if you have signed in recently, the IdP may still remember you, in which case it will skip the form and proceed directly to the next step. After establishing and proving your identity, the IdP will generate an assertion, a signed proof that effectively states that the IdP knows who you are and have verified your identity rigorously. Think of the assertion as your unique pass to the resources protected by the SP. The IdP will then submit that assertion back to the SP at its AssertionConsumerService endpoint, again using your browser.
Note that the SP service knows nothing about how IdP authenticates you. All the SP is interested in is an assertion.
If the assertion is well-formed and its signature is valid, the SAML exchange completes. At this point the SP accepts the assertion and creates a session for you. You can now access the resources protected by the SP for as long as the session lasts. If this step succeeds, you should see the photo of your cat in your browser.
Property List
The following is the full list of the properties of the component with short descriptions. Click on the links for further details.
| Active | Tells whether the server is active and ready to process requests. |
| BaseDir | Base directory on the server. |
| BindingKey | Contains a private key to sign the redirect binding requests. |
| DecryptionCertificate | The certificate to be used to decrypt assertions. |
| ExternalCrypto | Provides access to external signing and DC parameters. |
| FIPSMode | Reserved. |
| HandshakeTimeout | Specifies the handshake timeout in milliseconds. |
| Host | Specifies the host address of the SP server. |
| IdPServices | Populates a list of services supported by the IdP. |
| IdPSettings | Populates a list of SAML IdP entity settings. |
| Issuer | Name identifier of the issuer of the SP's requests. |
| KnownCertificates | Additional certificates for chain validation. |
| KnownKeys | Public keys for low-level signature validation. |
| LogoutPage | Specifies the location of the logout page. |
| MetadataURL | The SP's metadata location. |
| MetaSigningCertificate | Specifies the metadata signing certificate. |
| OfflineMode | Enables the Offline mode. |
| PinnedClient | Populates the pinned client details. |
| PinnedClientChain | Contains the certificate chain of the pinned client. |
| Port | Specifies the listening port number. |
| ProtectedResources | Specifies the list of protected resources. |
| RedirectOnLogoutPage | Specifies the location to redirect the user on logout. |
| Security | Provides access to the SAML security properties. |
| SenderChain | Contains the certificate chain of the message sender. |
| SigningCertificate | The certificate for signing the SP requests. |
| SigningChain | The signing certificate chain. |
| SocketSettings | Manages network connection settings. |
| SPServices | Populates a list of services supported by the SP. |
| SPSettings | Populates a list of SAML SP entity settings. |
| TLSServerChain | The server's TLS certificates. |
| TLSSettings | Manages TLS layer settings. |
| URL | Specifies the base URL of this SP server. |
Method List
The following is the full list of the methods of the component with short descriptions. Click on the links for further details.
| AddIdPService | Registers an IdP service in the IdPServices list. |
| AddSPService | Registers an SP service in the SPServices list. |
| Cleanup | Cleans up the server environment by purging expired sessions and cleaning caches. |
| Config | Sets or retrieves a configuration setting. |
| DoAction | Performs an additional action. |
| DropClient | Terminates a client connection. |
| ExportSettings | Saves the SP or IdP configuration to an XML metadata file. |
| GetClientBuffer | Acquires a piece of operation data. |
| GetProviderProperty | Returns the value of a custom provider property. |
| GetRequestBytes | Returns the contents of the connected client's HTTP request. |
| GetRequestHeader | Returns a request header value. |
| GetResponseHeader | Returns a response header value. |
| GetSessionProperty | Returns the value of a custom session property. |
| ImportSettings | Loads the metadata required for information exchange with the identity provider. Both local (SP-side) and remote (IdP-side) metadata can be loaded with this call. |
| InitiateArtifactResolve | Initiates the artifact resolution protocol. |
| InitiateAttributeQuery | Initiates the attribute query. |
| InitiateAuth | Starts SP-initiated SAML authentication flow. |
| InitiateLogout | Starts SP-initiated SAML logout flow. |
| ListClients | Enumerates the connected clients. |
| PinClient | Takes a snapshot of the connection's properties. |
| ProcessArtifact | Processes an artifact request received from the IdP service at one of artifact receiver endpoints. |
| ProcessArtifactResolveRequest | Processes an artifact request received from the SP service at one of the ARS endpoints. |
| ProcessAssertion | Processes assertion received from the IdP service at one of the ACS endpoints. |
| ProcessGenericRequest | Processes a generic HTTP SAML request. |
| ProcessLogoutRequest | Processes logout request received from the IdP service at one of the SLS endpoints. |
| Reset | Resets the component settings. |
| SetClientBuffer | Commits a data buffer to the connection. |
| SetProviderProperty | Sets the value of a custom provider property. |
| SetResponseHeader | Sets a response header. |
| SetSessionProperty | Sets the value of a custom provider session property. |
| Start | Starts the SP server. |
| Stop | Stops the IdP server. |
Event List
The following is the full list of the events fired by the component with short descriptions. Click on the links for further details.
| Accept | Reports an incoming connection. |
| ArtifactReceived | The server fires this event upon receiving an Artifact message from the other side. |
| ArtifactResolveRequestPrepared | This event is fired when a new artifact resolution request message has been prepared by the component. |
| ArtifactResolveRequestReceived | Reports receipt of ArtifactResolveRequest message. |
| AssertionReceived | This event is fired when an assertion is received from the IdP. |
| AttributeQueryPrepared | Notifies the application of the preparation of an AttributeQuery. |
| AuthnRequestPrepared | This event is fired when a new authentication request message has been prepared. |
| Connect | Reports an accepted connection. |
| Disconnect | Fires to report a disconnected client. |
| Encrypted | Notifies the application that the assertion is encrypted and provides recipient certificate details. |
| Error | Information about errors during data delivery. |
| ExternalSign | Handles remote or external signing initiated by the server protocol. |
| LogoutRequestPrepared | This event is fired when a new logout request has been prepared. |
| LogoutRequestReceived | The component uses this event to notify the application about an incoming SAML Logout Request message. |
| LogoutResponsePrepared | The component uses this event to notify the application about the Logout Response message being ready to be sent. |
| LogoutResponseReceived | The component uses this event to notify the application about an incoming SAML LogoutResponse message. |
| Notification | This event notifies the application about an underlying control flow event. |
| ProcessingCompleted | This event notifies the application of the completion of request or response processing. |
| ReadArtifact | Requests content identified by an artifact from the application. |
| ResourceClose | Tells the application that it can close the opened resource. |
| ResourceOpen | Requests the application to open the requested resource. |
| ResourceRead | Requests the application to read from an opened resource. |
| ResourceRequest | Notifies the application that a server resource is requested. |
| ResourceWrite | Requests the application to write to an opened resource. |
| SAMLMessagePrepared | This event is fired when a SAML message has been prepared and is ready to be dispatched. |
| SAMLMessageReceived | The server fires this event for every SAML message it receives. |
| SessionCreated | This event is fired when a new session has been established. |
| SessionDestroyed | This event is fired when the SP server has closed a session. |
| SessionEvent | Notifies the application about SAML session events. |
| SessionInfoNeeded | This event is fired in OfflineMode to request the session ID for the current flow. |
| SessionStateRetrieve | This event fires to retrieve session state information from the application. |
| SessionStateSave | This event passes a session state object to the application for safekeeping. |
| SignatureFound | Signifies the start of signature validation. |
| SignatureValidated | Reports the signature validation result. |
| TLSCertValidate | Fires when a client certificate needs to be validated. |
| TLSEstablished | Reports the setup of a TLS session. |
| TLSHandshake | Fires when a newly established client connection initiates a TLS handshake. |
| TLSPSK | Requests a pre-shared key for TLS-PSK. |
| TLSShutdown | Reports closure of a TLS session. |
| UserAuthCompleted | Notifies the application about the success of user authentication flow. |
| UserAuthFailed | Notifies the application about failure of user authentication flow. |
| UserAuthStart | Notifies the application about the start of user authentication flow. |
| UserLogoutCompleted | Notifies the application about the completion of user logout flow. |
| UserLogoutStart | Notifies the application about the start of user logout flow. |
Config Settings
The following is a list of config settings for the component with short descriptions. Click on the links for further details.
| AllowOptionsResponseWithoutAuth | Enables unauthenticated responses to OPTIONS requests. |
| AttributeConsumingService | TBD. |
| AuthDigestExpire | Specifies digest expiration time for digest authentication. |
| BoundPort | The port that was bound by the server. |
| ContactPerson | The ContactPerson entry of the provider metadata. |
| DualStack | Allows the use of ip4 and ip6 simultaneously. |
| HandshakeTimeout | The HTTPS handshake timeout. |
| HomePage | Specifies the home page resource name. |
| IDPAQS | TBD. |
| IDPARS | TBD. |
| IDPSLS | TBD. |
| IDPSSO | TBD. |
| MaxIssueInstantTimeDiff | The maximum issue-instant time delta. |
| OAuthAllowAccessByDefault | Specifies whether access to a resource is allowed by default. |
| OAuthAutoValidateTokens | Allows to validate OAuth 2.0 access tokens automatically. |
| OAuthIntrospectionClientID | Specifies a client ID on the authentication service. |
| OAuthIntrospectionClientSecret | Specifies a client secret on the authentication service. |
| OAuthIntrospectionURL | Specifies the URL to be used to introspect access tokens. |
| OAuthTokenValidationKeys | Specifies JW keys in JSON format for validating access token signatures. |
| OrganizationDisplayName | The OrganizationDisplayName entry of the provider metadata. |
| OrganizationLang | The OrganizationLang key of the provider metadata. |
| OrganizationName | The OrganizationName element of the provider metadata. |
| OrganizationURL | The OrganizationURL element of the provider metadata. |
| PortRangeFrom | The lower bound of allowed port scope to listen on. |
| PortRangeTo | The higher bound of allowed port scope to listen on. |
| RequestFilter | The request string modifier. |
| SAMLAction | TBD. |
| SAMLBuffer | TBD. |
| SAMLResourceProtected | TBD. |
| SAMLResourceSpecial | TBD. |
| SAMLString | TBD. |
| SendBufferSize | The network send buffer size. |
| ServerName | Specifies the server name for the created responses. |
| SessionTimeout | The HTTP session timeout. |
| SessionTTL | The SAML session time-to-live value. |
| SignatureAlgorithm | TBD. |
| TempPath | Path for storing temporary files. |
| UseZeroIndexForDefaultServices | TBD. |
| WantAssertionsSigned | TBD. |
| ASN1UseGlobalTagCache | Controls whether ASN.1 module should use a global object cache. |
| AssignSystemSmartCardPins | Specifies whether CSP-level PINs should be assigned to CNG keys. |
| CheckKeyIntegrityBeforeUse | Enables or disable private key integrity check before use. |
| CookieCaching | Specifies whether a cookie cache should be used for HTTP(S) transports. |
| Cookies | Gets or sets local cookies for the component. |
| DefDeriveKeyIterations | Specifies the default key derivation algorithm iteration count. |
| DNSLocalSuffix | The suffix to assign for TLD names. |
| EnableClientSideSSLFFDHE | Enables or disables finite field DHE key exchange support in TLS clients. |
| GlobalCookies | Gets or sets global cookies for all the HTTP transports. |
| HardwareCryptoUsePolicy | The hardware crypto usage policy. |
| HttpUserAgent | Specifies the user agent name to be used by all HTTP clients. |
| HttpVersion | The HTTP version to use in any inner HTTP client components created. |
| IgnoreExpiredMSCTLSigningCert | Whether to tolerate the expired Windows Update signing certificate. |
| ListDelimiter | The delimiter character for multi-element lists. |
| LogDestination | Specifies the debug log destination. |
| LogDetails | Specifies the debug log details to dump. |
| LogFile | Specifies the debug log filename. |
| LogFilters | Specifies the debug log filters. |
| LogFlushMode | Specifies the log flush mode. |
| LogLevel | Specifies the debug log level. |
| LogMaxEventCount | Specifies the maximum number of events to cache before further action is taken. |
| LogRotationMode | Specifies the log rotation mode. |
| MaxASN1BufferLength | Specifies the maximal allowed length for ASN.1 primitive tag data. |
| MaxASN1TreeDepth | Specifies the maximal depth for processed ASN.1 trees. |
| OCSPHashAlgorithm | Specifies the hash algorithm to be used to identify certificates in OCSP requests. |
| OldClientSideRSAFallback | Specifies whether the SSH client should use a SHA1 fallback. |
| PKICache | Specifies which PKI elements (certificates, CRLs, OCSP responses) should be cached. |
| PKICachePath | Specifies the file system path where cached PKI data is stored. |
| ProductVersion | Returns the version of the SecureBlackbox library. |
| ServerSSLDHKeyLength | Sets the size of the TLS DHE key exchange group. |
| StaticDNS | Specifies whether static DNS rules should be used. |
| StaticIPAddress[domain] | Gets or sets an IP address for the specified domain name. |
| StaticIPAddresses | Gets or sets all the static DNS rules. |
| Tag | Allows to store any custom data. |
| TLSSessionGroup | Specifies the group name of TLS sessions to be used for session resumption. |
| TLSSessionLifetime | Specifies lifetime in seconds of the cached TLS session. |
| TLSSessionPurgeInterval | Specifies how often the session cache should remove the expired TLS sessions. |
| UseCRLObjectCaching | Specifies whether reuse of loaded CRL objects is enabled. |
| UseInternalRandom | Switches between SecureBlackbox-own and platform PRNGs. |
| UseLegacyAdESValidation | Enables legacy AdES validation mode. |
| UseOCSPResponseObjectCaching | Specifies whether reuse of loaded OCSP response objects is enabled. |
| UseOwnDNSResolver | Specifies whether the client components should use own DNS resolver. |
| UseSharedSystemStorages | Specifies whether the validation engine should use a global per-process copy of the system certificate stores. |
| UseSystemNativeSizeCalculation | An internal CryptoAPI access tweak. |
| UseSystemOAEPAndPSS | Enforces or disables the use of system-driven RSA OAEP and PSS computations. |
| UseSystemRandom | Enables or disables the use of the OS PRNG. |
| XMLRDNDescriptorName[OID] | Defines an OID mapping to descriptor names for the certificate's IssuerRDN or SubjectRDN. |
| XMLRDNDescriptorPriority[OID] | Specifies the priority of descriptor names associated with a specific OID. |
| XMLRDNDescriptorReverseOrder | Specifies whether to reverse the order of descriptors in RDN. |
| XMLRDNDescriptorSeparator | Specifies the separator used between descriptors in RDN. |
Active Property (SAMLSPServer Component)
Tells whether the server is active and ready to process requests.
Syntax
Default Value
False
Remarks
This property indicates whether the IdP server is in an active state.
This property is read-only and not available at design time.
BaseDir Property (SAMLSPServer Component)
Base directory on the server.
Syntax
Default Value
""
Remarks
Use this property to specify the base directory for the SP server.
BindingKey Property (SAMLSPServer Component)
Contains a private key to sign the redirect binding requests.
Syntax
Remarks
Use this property to set the signing key for the redirect binding object. This is used to sign the content of the redirect binding.
Note that when using the redirect binding, the outgoing SAML message must not be signed in parallel with a certificate. Any assertions may still be signed.
This property is not available at design time.
Please refer to the CryptoKey type for a complete list of fields.DecryptionCertificate Property (SAMLSPServer Component)
The certificate to be used to decrypt assertions.
Syntax
public Certificate DecryptionCertificate { get; set; }
Public Property DecryptionCertificate As Certificate
Remarks
Use this property to provide the certificate to be used for decrypting assertions included in IdP (Identity Provider) responses. This certificate should have a private key associated with it.
This property is not available at design time.
Please refer to the Certificate type for a complete list of fields.ExternalCrypto Property (SAMLSPServer Component)
Provides access to external signing and DC parameters.
Syntax
public ExternalCrypto ExternalCrypto { get; }
Public ReadOnly Property ExternalCrypto As ExternalCrypto
Remarks
Use this property to tune-up remote cryptography settings. SecureBlackbox supports two independent types of external cryptography: synchronous (based on the ExternalSign event) and asynchronous (based on the DC protocol and the DCAuth signing component).
This property is read-only.
Please refer to the ExternalCrypto type for a complete list of fields.FIPSMode Property (SAMLSPServer Component)
Reserved.
Syntax
Default Value
False
Remarks
This property is reserved for future use.
HandshakeTimeout Property (SAMLSPServer Component)
Specifies the handshake timeout in milliseconds.
Syntax
Default Value
20000
Remarks
Use this property to set the TLS handshake timeout.
Host Property (SAMLSPServer Component)
Specifies the host address of the SP server.
Syntax
Default Value
""
Remarks
Use this property to specify the IP address on which to listen to incoming connections. To specify the listening port number, use Port.
IdPServices Property (SAMLSPServer Component)
Populates a list of services supported by the IdP.
Syntax
public SAMLServiceInfoList IdPServices { get; }
Public ReadOnly Property IdPServices As SAMLServiceInfoList
Remarks
Use this property to access the list of services supported by the IdP. In the SAMLIdPServer, this is the list of services supported by the IdP. In the SAMLSPServer, this is the list of services advertised by the remote IdP server. These can be loaded from the respective IdP's metadata or set manually via AddIdPService method.
This property is read-only and not available at design time.
Please refer to the SAMLServiceInfo type for a complete list of fields.IdPSettings Property (SAMLSPServer Component)
Populates a list of SAML IdP entity settings.
Syntax
public SAMLEntity IdPSettings { get; }
Public ReadOnly Property IdPSettings As SAMLEntity
Remarks
Use this property to get or set properties of a SAML IdP entity. These properties can be adjusted manually or loaded from the respective metadata file.
This property is read-only and not available at design time.
Please refer to the SAMLEntity type for a complete list of fields.Issuer Property (SAMLSPServer Component)
Name identifier of the issuer of the SP's requests.
Syntax
Default Value
""
Remarks
Use this property to set the name identifier of this Service Provider (SP) to be used in its requests.
KnownCertificates Property (SAMLSPServer Component)
Additional certificates for chain validation.
Syntax
public CertificateList KnownCertificates { get; }
Public Property KnownCertificates As CertificateList
Remarks
Use this property to supply a list of additional certificates that might be needed for chain validation. An example of a scenario where you might want to do that is when intermediary CA certificates are absent from the standard system locations (or when there are no standard system locations), and therefore should be supplied to the component manually.
The purpose of the certificates to be added to this collection is roughly equivalent to that of the Intermediate Certification Authorities system store in Windows.
Do not add trust anchors or root certificates to this collection: add them to TrustedCertificates instead.
This property is not available at design time.
Please refer to the Certificate type for a complete list of fields.KnownKeys Property (SAMLSPServer Component)
Public keys for low-level signature validation.
Syntax
public CryptoKeyList KnownKeys { get; }
Public Property KnownKeys As CryptoKeyList
Remarks
Use this property to supply a list of public keys that might be needed for redirect binding signature validation.
This property is not available at design time.
Please refer to the CryptoKey type for a complete list of fields.LogoutPage Property (SAMLSPServer Component)
Specifies the location of the logout page.
Syntax
Default Value
"/sp/logout"
Remarks
Use this property to specify the relative URL of the logout page.
MetadataURL Property (SAMLSPServer Component)
The SP's metadata location.
Syntax
Default Value
"/sp/metadata"
Remarks
This property specifies the metadata URL of this Service Provider (SP).
MetaSigningCertificate Property (SAMLSPServer Component)
Specifies the metadata signing certificate.
Syntax
public Certificate MetaSigningCertificate { get; set; }
Public Property MetaSigningCertificate As Certificate
Remarks
Use this property to specify the certificate to be used to sign the SP's metadata. This certificate should have a private key associated with it.
This property is not available at design time.
Please refer to the Certificate type for a complete list of fields.OfflineMode Property (SAMLSPServer Component)
Enables the Offline mode.
Syntax
Default Value
True
Remarks
In the Offline mode the server does not open the listening port. Instead, it expects all incoming requests to be relayed by the application via calls to ProcessAssertion, ProcessLogoutRequest ProcessArtifactResolveRequest, and other similar methods.
The Offline mode is a handy mechanism for attaching the server to external web engines, such as IIS or Tomcat. It lets you leave the HTTP matters to the engine, and only be responsible for handling the actual SAML traffic.
PinnedClient Property (SAMLSPServer Component)
Populates the pinned client details.
Syntax
public TLSConnectionInfo PinnedClient { get; }
Public ReadOnly Property PinnedClient As TLSConnectionInfo
Remarks
Use this property to access the details of the client connection previously pinned with PinClient method.
This property is read-only and not available at design time.
Please refer to the TLSConnectionInfo type for a complete list of fields.PinnedClientChain Property (SAMLSPServer Component)
Contains the certificate chain of the pinned client.
Syntax
public CertificateList PinnedClientChain { get; }
Public ReadOnly Property PinnedClientChain As CertificateList
Remarks
Use this property to access the certificate chain of the client connection pinned previously with a PinClient call.
This property is read-only and not available at design time.
Please refer to the Certificate type for a complete list of fields.Port Property (SAMLSPServer Component)
Specifies the listening port number.
Syntax
Default Value
80
Remarks
Use this property to specify the port number on which the SP server should listen for incoming connections. To specify the server's IP address use Host.
ProtectedResources Property (SAMLSPServer Component)
Specifies the list of protected resources.
Syntax
Default Value
""
Remarks
This property contains a set of relative URLs of the protected resources offered by this Service Provider (SP).
RedirectOnLogoutPage Property (SAMLSPServer Component)
Specifies the location to redirect the user on logout.
Syntax
Default Value
"https://nsoftware.com"
Remarks
Use this property to specify the page where to redirect the user on logout.
Security Property (SAMLSPServer Component)
Provides access to the SAML security properties.
Syntax
public SAMLSecuritySettings Security { get; }
Public ReadOnly Property Security As SAMLSecuritySettings
Remarks
Use this property to access the security parameters of the server.
This property is read-only and not available at design time.
Please refer to the SAMLSecuritySettings type for a complete list of fields.SenderChain Property (SAMLSPServer Component)
Contains the certificate chain of the message sender.
Syntax
public CertificateList SenderChain { get; }
Public ReadOnly Property SenderChain As CertificateList
Remarks
Use this property to access the certificate chain of the creator of the signed message or entity that is currently being processed. This property is only available from SignatureFound and SignatureValidated events.
This property is read-only and not available at design time.
Please refer to the Certificate type for a complete list of fields.SigningCertificate Property (SAMLSPServer Component)
The certificate for signing the SP requests.
Syntax
public Certificate SigningCertificate { get; set; }
Public Property SigningCertificate As Certificate
Remarks
Use this property to designate a certificate for signing the SP requests. The provided certificate must have a private key associated with it.
This property is not available at design time.
Please refer to the Certificate type for a complete list of fields.SigningChain Property (SAMLSPServer Component)
The signing certificate chain.
Syntax
public CertificateList SigningChain { get; }
Public Property SigningChain As CertificateList
Remarks
Use this property to provide the chain for the signing certificate. Use the SigningCertificate property, if it is available, to provide the signing certificate itself.
This property is not available at design time.
Please refer to the Certificate type for a complete list of fields.SocketSettings Property (SAMLSPServer Component)
Manages network connection settings.
Syntax
public SocketSettings SocketSettings { get; }
Public ReadOnly Property SocketSettings As SocketSettings
Remarks
Use this property to tune up network connection parameters.
This property is read-only.
Please refer to the SocketSettings type for a complete list of fields.SPServices Property (SAMLSPServer Component)
Populates a list of services supported by the SP.
Syntax
public SAMLServiceInfoList SPServices { get; }
Public ReadOnly Property SPServices As SAMLServiceInfoList
Remarks
Use this property to access the list of services supported by the SP. In the SAMLSPServer, this is the list of services supported by the SP. In the SAMLIdPServer, this is the list of services advertised by the remote SP server. These can be loaded from the respective SP's metadata or set manually via AddSPService method.
This property is read-only and not available at design time.
Please refer to the SAMLServiceInfo type for a complete list of fields.SPSettings Property (SAMLSPServer Component)
Populates a list of SAML SP entity settings.
Syntax
public SAMLEntity SPSettings { get; }
Public ReadOnly Property SPSettings As SAMLEntity
Remarks
Use this property to get or set properties of a SAML SP entity. These properties can be adjusted manually or loaded from the respective metadata file.
This property is read-only and not available at design time.
Please refer to the SAMLEntity type for a complete list of fields.TLSServerChain Property (SAMLSPServer Component)
The server's TLS certificates.
Syntax
public CertificateList TLSServerChain { get; }
Public Property TLSServerChain As CertificateList
Remarks
Use this property to provide a list of TLS certificates for the server endpoint.
A TLS endpoint needs a certificate to be able to accept TLS connections. At least one of the certificates in the collection - the endpoint certificate - must have a private key associated with it.
The collection may include more than one endpoint certificate, and more than one chain. A typical usage scenario is to include two chains (ECDSA and RSA), to cater for clients with different cipher suite preferences.
This property is not available at design time.
Please refer to the Certificate type for a complete list of fields.TLSSettings Property (SAMLSPServer Component)
Manages TLS layer settings.
Syntax
public TLSSettings TLSSettings { get; }
Public ReadOnly Property TLSSettings As TLSSettings
Remarks
Use this property to tune up the TLS layer parameters.
This property is read-only.
Please refer to the TLSSettings type for a complete list of fields.URL Property (SAMLSPServer Component)
Specifies the base URL of this SP server.
Syntax
Default Value
""
Remarks
Use this property to set the base URL for this Service Provider (SP) server.
Please make sure the URL you provide here aligns well with the relative endpoint resource paths, such as AssertionConsumerService or ArtifactResolutionService. The two parts (the URL and the endpoint paths) are concatenated to produce full endpoint URLs. Please double check that only one of the parts includes the slash character in it: either the endpoint paths at the beginning (the default configuration), or the base URL at the end.
AddIdPService Method (SAMLSPServer Component)
Registers an IdP service in the IdPServices list.
Syntax
Remarks
Use this method to add an entry to the list of known external SAML services and their locations.
The service provider needs to be knowledgeable of the external IdP services that it needs to use. That information can either be provided in the form of a metadata file (see ImportSettings), or registered manually using this method.
When using this method, make sure to register all the services you expect to work with. Note that if the same IdP service is available through several different transports (bindings), you will need to register each (service, transport) pair individually:
sp.AddIdPService(spsSingleSignOnService, csbtPOST, "https://idp.identityserver/saml/sso", -1, -1);
sp.AddIdPService(spsSingleSignOnService, csbtRedirect, "https://idp.identityserver/saml/sso", -1, -1);
Use the Service parameter to specify the service to register:
| spsUnknown | 0 | The service is of unknown or unsupported type |
| spsAssertionConsumerService | 1 | The assertion consumer service (SP side only) |
| spsSingleLogoutService | 2 | The single logout service (SP or IdP sides) |
| spsArtifactResolutionService | 3 | The artifact resolution service (SP or IdP sides) |
| spsAttributeQueryService | 4 | The attribute query service (IdP side only) |
| spsSingleSignOnService | 5 | The single sign-on service (IdP side only) |
The BindingType specifies the transport type that the service being registered should use. Note that not every kind of service supports every kind of transport. It is typical for SSO and SLS services to use POST or Redirect bindings. This information is typically provided by the identity provider.
| csbtNone | 0 | TBD |
| csbtSOAP | 1 | TBD |
| csbtPAOS | 2 | TBD |
| csbtRedirect | 3 | TBD |
| csbtPOST | 4 | TBD |
| csbtArtifact | 5 | TBD |
The Location parameter specifies the absolute URL of the respective SAML web endpoint.
The Priority parameter specifies the relative priority of the transport among several identical services. The actual transport used may be different to the specified priority, as the request received from the SP (such as AuthnRequest) may explicitly request a specific transport to use.
The Index parameter specifies the index of the endpoint, which is a unique value assigned to each endpoint. Pass -1 unless you want to provide the index explicitly.
Note that this method registers a known service - something that the service provider should be aware of. This is different to the purpose of the AddSPService method, which registers the service provider's own service.
AddSPService Method (SAMLSPServer Component)
Registers an SP service in the SPServices list.
Syntax
Remarks
Use this method to add an entry to the list of SAML services and their locations provided by the SP.
A service provider can provide a variety of SAML services through a selection of endpoints, each supporting one or more transports (or bindings). Typical examples are an assertion consumer service or a single logout service, each of which can be served independently on the same or different endpoints, via a POST or Redirect transports (or both).
Each AddSPService call registers a single service offered via a single transport. If you would like to have the same service to be available using several different transports, you need to register each combination individually, even if the service runs at the same web endpoint:
sp.AddSPService(spsAssertionConsumerService, csbtPOST, '/saml/acs', -1, 1);
sp.AddSPService(spsAssertionConsumerService, csbtRedirect, '/saml/acs', -1, 2);
Use the Service parameter to specify the service to register:
| spsUnknown | 0 | The service is of unknown or unsupported type |
| spsAssertionConsumerService | 1 | The assertion consumer service (SP side only) |
| spsSingleLogoutService | 2 | The single logout service (SP or IdP sides) |
| spsArtifactResolutionService | 3 | The artifact resolution service (SP or IdP sides) |
| spsAttributeQueryService | 4 | The attribute query service (IdP side only) |
| spsSingleSignOnService | 5 | The single sign-on service (IdP side only) |
The BindingType specifies the transport type that the service being registered should use. Note that not every kind of service supports every kind of transport. It is typical for ACS service to use POST binding (due to the size of assertions), and SLS to either use POST or Redirect.
| csbtNone | 0 | TBD |
| csbtSOAP | 1 | TBD |
| csbtPAOS | 2 | TBD |
| csbtRedirect | 3 | TBD |
| csbtPOST | 4 | TBD |
| csbtArtifact | 5 | TBD |
The Location parameter specifies an absolute or relative path to the service within the SAML web service:
sp.AddSPService(spsAssertionConsumerService, csbtPOST, 'https://app.com/saml/acs', -1, 1); // absolute path
sp.AddSPService(spsAssertionConsumerService, csbtRedirect, '/saml/acs', -1, 2); // relative path
The Priority parameter is nominal as it only specifies the relative priority of the transport in the SP metadata. The actual transport used, among those supported, depends on the choice of the external identity provider. Pass -1 to stick with the default priority.
The Index parameter specifies the index of the endpoint, which is a unique value assigned to each endpoint. Pass -1 unless you want to provide the index explicitly.
Note that this method registers the service provider's own service - something that the service provider provides. This is different to AddIdPService method, which registers a foreign identity provider's service - something that the service provider should be aware of.
Cleanup Method (SAMLSPServer Component)
Cleans up the server environment by purging expired sessions and cleaning caches.
Syntax
public void Cleanup();
Public Sub Cleanup()
Remarks
Call this method while the server is active to clean up the environment allocated for the server by releasing unused resources and cleaning caches.
Config Method (SAMLSPServer Component)
Sets or retrieves a configuration setting.
Syntax
Remarks
Config is a generic method available in every component. It is used to set and retrieve configuration settings for the component.
These settings are similar in functionality to properties, but they are rarely used. In order to avoid "polluting" the property namespace of the component, access to these internal properties is provided through the Config method.
To set a configuration setting named PROPERTY, you must call Config("PROPERTY=VALUE"), where VALUE is the value of the setting expressed as a string. For boolean values, use the strings "True", "False", "0", "1", "Yes", or "No" (case does not matter).
To read (query) the value of a configuration setting, you must call Config("PROPERTY"). The value will be returned as a string.
DoAction Method (SAMLSPServer Component)
Performs an additional action.
Syntax
Remarks
DoAction is a generic method available in every component. It is used to perform an additional action introduced after the product major release. The list of actions is not fixed, and may be flexibly extended over time.
The unique identifier (case insensitive) of the action is provided in the ActionID parameter.
ActionParams contains the value of a single parameter, or a list of multiple parameters for the action in the form of PARAM1=VALUE1;PARAM2=VALUE2;....
Common ActionIDs:
| Action | Parameters | Returned value | Description |
| ResetTrustedListCache | none | none | Clears the cached list of trusted lists. |
| ResetCertificateCache | none | none | Clears the cached certificates. |
| ResetCRLCache | none | none | Clears the cached CRLs. |
| ResetOCSPResponseCache | none | none | Clears the cached OCSP responses. |
DropClient Method (SAMLSPServer Component)
Terminates a client connection.
Syntax
Remarks
Call this method to shut down a connected client. Forced indicates whether the connection should be closed in a graceful manner.
ExportSettings Method (SAMLSPServer Component)
Saves the SP or IdP configuration to an XML metadata file.
Syntax
Remarks
Use this method to save the Service Provider (SP) or Identity Provider (IdP) configuration in the form of XML metadata. The SP metadata file may then be transferred to identity providers (IdP) to let them know about the SP configuration.
Adjust the provider configuration as required in SPSettings or IdPSettings object before calling this method. Assign MetaSigningCertificate to enforce signing of the metadata XML.
GetClientBuffer Method (SAMLSPServer Component)
Acquires a piece of operation data.
Syntax
Remarks
Use this method to obtain a piece of data relevant to a transfer operation in a thread-safe way.
A typical place to call this method is inside the ResourceWrite event handler, when implementing customized file transfers.
GetProviderProperty Method (SAMLSPServer Component)
Returns the value of a custom provider property.
Syntax
Remarks
This method, together with SetProviderProperty, provides an extensible way of managing the Service Provider's settings that are not available through the primary properties of the component. As SAML usage scenarios evolve and new providers appear, the list of supported properties can be extended.
The following properties are currently supported:
- ContactPerson
- OrganizationName
- OrganizationDisplayName
- OrganizationURL
- OrganizationLang
GetRequestBytes Method (SAMLSPServer Component)
Returns the contents of the connected client's HTTP request.
Syntax
Remarks
Use this method to get the body of the client's HTTP request. Note that the body of GET and HEAD requests is empty. The method returns the requested content.
GetRequestHeader Method (SAMLSPServer Component)
Returns a request header value.
Syntax
Remarks
Use this method to get the value of a request header. A good place to call this method is a request-marking event, such as GetRequest or PostRequest.
GetResponseHeader Method (SAMLSPServer Component)
Returns a response header value.
Syntax
Remarks
Use this method to get the value of a response header. A good place to call this method is HeadersPrepared event. Call the method with empty HeaderName to get the whole response header.
GetSessionProperty Method (SAMLSPServer Component)
Returns the value of a custom session property.
Syntax
Remarks
This method, together with SetSessionProperty, provides an extensible way of managing the Service Provider's session properties that are not available through the primary properties and events of the component. These methods can be called on any active browser session. Use SessionCreated and SessionDestroyed events to get notifications about session creation and disposal.
The following properties are supported for SP sessions and can be passed to the Name parameter of this method:
- Authenticated: whether the session has been authenticated with the IdP service.
- AuthnRequestID: the AuthnRequest ID.
- Expires: the web session expiration time.
- LogoutRequestID: the LogoutRequest ID.
- NameID: the NameID of the user.
- NameIDFormat: the format of the NameID of the user.
- FormattedNameID: the formatted version of the NameID.
- RelayState: the current (last) relay state entry.
- Session: the session ID (the same as you pass as parameter).
- SAMLSession: the browser cookie that corresponds to the session.
- SessionIndex: a list of cross-network session indexes assigned to this session.
- URL: the current request's URL.
- UserData: the protocol-independent user data. Use this session property to store custom information associated with the session across contexts.
- Stage: the current session stage (or epoch).
ImportSettings Method (SAMLSPServer Component)
Loads the metadata required for information exchange with the identity provider. Both local (SP-side) and remote (IdP-side) metadata can be loaded with this call.
Syntax
Remarks
The Identity provider (IdP) may have different options and requirements for interactions with the Service Provider (SP). Usually all these options together with X.509 certificates needed for data exchange are stored in XML metadata files. Use this method to load metadata from a file generated by an IdP.
The Metadata parameter contains metadata in the form of byte array. Set SP parameter to true to indicate that it is the Service Provider's own settings that are being loaded.
The loaded metadata is populated in the SPSettings or IdPSettings object (depending on the value of the SP parameter).
InitiateArtifactResolve Method (SAMLSPServer Component)
Initiates the artifact resolution protocol.
Syntax
Remarks
Use this event to initiate the artifact resolution protocol for Artifact. Specify the desired SP service endpoint via the IdPServiceIndex parameter.
| sprUnknown | 0 | Unknown or undefined processing result |
| sprSuccess | 1 | The processing completed successfully. No tangible output has been generated (e.g. an artifact was resolved and acknowledged, but nothing needs to be sent to the browser). |
| sprSAMLMessage | 2 | The processing was fully or partially successful. The output contains a new SAML message that needs to be conveyed to the other SAML party. |
| sprSignOnPage | 3 | The processing was fully or partially successful. The output contains or redirects to a SAML login page. |
| sprResource | 4 | The processing was fully or partially successful. The output contains, or redirects to, a generic web resource. |
| sprSAMLError | 5 | The processing failed due to SAML-related issue (bad sign-on parameters, unknown principal etc.). The output contains a SAML error message. This still needs to be relayed to the other SAML party. |
| sprTransportError | 6 | The operation could not be completed due to an issue with configuration (e.g. non-existent SAML endpoint), permissions, or network. The SAML protocol could not commence. The output contains a transport-layer (HTTP) error message which can/should be displayed to the user in the browser. |
You can use this method with or without the OfflineMode.
Note: this method is currently in development and will be available in later SecureBlackbox updates.
InitiateAttributeQuery Method (SAMLSPServer Component)
Initiates the attribute query.
Syntax
public int InitiateAttributeQuery(long connectionID, string sessionID, int idPServiceIndex, string nameID, string nameIDFormat, string attributes, string attrNameFormats, string attrFriendlyNames, string tag);
Public Function InitiateAttributeQuery(ByVal ConnectionID As Long, ByVal SessionID As String, ByVal IdPServiceIndex As Integer, ByVal NameID As String, ByVal NameIDFormat As String, ByVal Attributes As String, ByVal AttrNameFormats As String, ByVal AttrFriendlyNames As String, ByVal Tag As String) As Integer
Remarks
Use this event to initiate the attribute query for user NameID. Specify the desired Attributes as a list of CRLF-separated attribute names. AttrNameFormats and AttrFriendlyNames can also be provided in the same way.
Specify the IdP AQS endpoint via the IdPServiceIndex parameter.
| sprUnknown | 0 | Unknown or undefined processing result |
| sprSuccess | 1 | The processing completed successfully. No tangible output has been generated (e.g. an artifact was resolved and acknowledged, but nothing needs to be sent to the browser). |
| sprSAMLMessage | 2 | The processing was fully or partially successful. The output contains a new SAML message that needs to be conveyed to the other SAML party. |
| sprSignOnPage | 3 | The processing was fully or partially successful. The output contains or redirects to a SAML login page. |
| sprResource | 4 | The processing was fully or partially successful. The output contains, or redirects to, a generic web resource. |
| sprSAMLError | 5 | The processing failed due to SAML-related issue (bad sign-on parameters, unknown principal etc.). The output contains a SAML error message. This still needs to be relayed to the other SAML party. |
| sprTransportError | 6 | The operation could not be completed due to an issue with configuration (e.g. non-existent SAML endpoint), permissions, or network. The SAML protocol could not commence. The output contains a transport-layer (HTTP) error message which can/should be displayed to the user in the browser. |
You can use this method with or without the OfflineMode.
Note: this method is currently in development and will be available in later SecureBlackbox updates.
InitiateAuth Method (SAMLSPServer Component)
Starts SP-initiated SAML authentication flow.
Syntax
Remarks
Use this method to initiate SAML authentication flow on the SP side. Pass the index of the single sign-on service that you want to use to the IdPServiceIndex parameter. Leave it empty to let the component pick up the best one automatically. Use RelayState to pass the callback URL to the IdP service. This will be mirrored back by the IDP in its response.
This method returns the processing result as one of the values given below. Right before it returns it passes the processing results back to the caller via the ProcessingCompleted event. This event fires independently of the processing outcome (success or failure), and contains the same ConnectionID that is passed to this call.
| sprUnknown | 0 | Unknown or undefined processing result |
| sprSuccess | 1 | The processing completed successfully. No tangible output has been generated (e.g. an artifact was resolved and acknowledged, but nothing needs to be sent to the browser). |
| sprSAMLMessage | 2 | The processing was fully or partially successful. The output contains a new SAML message that needs to be conveyed to the other SAML party. |
| sprSignOnPage | 3 | The processing was fully or partially successful. The output contains or redirects to a SAML login page. |
| sprResource | 4 | The processing was fully or partially successful. The output contains, or redirects to, a generic web resource. |
| sprSAMLError | 5 | The processing failed due to SAML-related issue (bad sign-on parameters, unknown principal etc.). The output contains a SAML error message. This still needs to be relayed to the other SAML party. |
| sprTransportError | 6 | The operation could not be completed due to an issue with configuration (e.g. non-existent SAML endpoint), permissions, or network. The SAML protocol could not commence. The output contains a transport-layer (HTTP) error message which can/should be displayed to the user in the browser. |
You can use this method with or without the OfflineMode.
InitiateLogout Method (SAMLSPServer Component)
Starts SP-initiated SAML logout flow.
Syntax
Remarks
Use this method to initiate SAML logout flow on the SP side. Pass the index of the single logout service that you want to use to the IdPServiceIndex parameter.
Use IdPServiceIndex to specify the identity provider's service that you want to use for signing out. Provide the existing SAML session details in one of the following ways:
- as an HTTP SessionID: in this case the component will try to pick the matching SAML session from its session cache.
- as a known NameID.
- as a known SAML SessionIndex.
You can use a combination of the above.
This method returns the processing result as one of the values given below. Right before it returns it passes the processing results back to the caller via the ProcessingCompleted event. This event fires independently of the processing outcome (success or failure), and contains the same ConnectionID that is passed to this call.
| sprUnknown | 0 | Unknown or undefined processing result |
| sprSuccess | 1 | The processing completed successfully. No tangible output has been generated (e.g. an artifact was resolved and acknowledged, but nothing needs to be sent to the browser). |
| sprSAMLMessage | 2 | The processing was fully or partially successful. The output contains a new SAML message that needs to be conveyed to the other SAML party. |
| sprSignOnPage | 3 | The processing was fully or partially successful. The output contains or redirects to a SAML login page. |
| sprResource | 4 | The processing was fully or partially successful. The output contains, or redirects to, a generic web resource. |
| sprSAMLError | 5 | The processing failed due to SAML-related issue (bad sign-on parameters, unknown principal etc.). The output contains a SAML error message. This still needs to be relayed to the other SAML party. |
| sprTransportError | 6 | The operation could not be completed due to an issue with configuration (e.g. non-existent SAML endpoint), permissions, or network. The SAML protocol could not commence. The output contains a transport-layer (HTTP) error message which can/should be displayed to the user in the browser. |
Use RelayState to pass a value to the IdP that you want to be mirrored back in the IdP's response. The Tag value will be similarly mirrored, but in the component's events, such as ProcessingCompleted.
You can use this method with or without the OfflineMode.
ListClients Method (SAMLSPServer Component)
Enumerates the connected clients.
Syntax
Remarks
This method enumerates the connected clients. It returns a list of strings, with each string being of 'ConnectionID|Address|Port' format, and representing a single connection.
PinClient Method (SAMLSPServer Component)
Takes a snapshot of the connection's properties.
Syntax
Remarks
Use this method to take a snapshot of a connected client. The captured properties are populated in PinnedClient and PinnedClientChain properties.
ProcessArtifact Method (SAMLSPServer Component)
Processes an artifact request received from the IdP service at one of artifact receiver endpoints.
Syntax
Remarks
Use this method to pass a SAML artifact received at one of the artifact endpoints.
Artifact messages are typically very simple:
https://idp.server.com/sso/artifact?SAMLart=artifact
In response to the artifact received, the server initiates an artifact resolution protocol to retrieve the SAML message identified by the artifact. This will typically expose itself via an invocation of the ArtifactResolveRequestPrepared event, and, later on, of an event matching the type of the actual message received - such as AssertionReceived.
| sprUnknown | 0 | Unknown or undefined processing result |
| sprSuccess | 1 | The processing completed successfully. No tangible output has been generated (e.g. an artifact was resolved and acknowledged, but nothing needs to be sent to the browser). |
| sprSAMLMessage | 2 | The processing was fully or partially successful. The output contains a new SAML message that needs to be conveyed to the other SAML party. |
| sprSignOnPage | 3 | The processing was fully or partially successful. The output contains or redirects to a SAML login page. |
| sprResource | 4 | The processing was fully or partially successful. The output contains, or redirects to, a generic web resource. |
| sprSAMLError | 5 | The processing failed due to SAML-related issue (bad sign-on parameters, unknown principal etc.). The output contains a SAML error message. This still needs to be relayed to the other SAML party. |
| sprTransportError | 6 | The operation could not be completed due to an issue with configuration (e.g. non-existent SAML endpoint), permissions, or network. The SAML protocol could not commence. The output contains a transport-layer (HTTP) error message which can/should be displayed to the user in the browser. |
You can use this method with or without the OfflineMode.
Note: this method is currently in development and will be available in later SecureBlackbox updates.
ProcessArtifactResolveRequest Method (SAMLSPServer Component)
Processes an artifact request received from the SP service at one of the ARS endpoints.
Syntax
Remarks
Use this method to pass a SAML artifact request received at one of the ArtifactResolutionService endpoints.
This method returns the processing result as one of the values given below. Right before it returns it passes the processing results back to the caller via the ProcessingCompleted event. This event fires independently of the processing outcome (success or failure), and contains the same ConnectionID that is passed to this call.
| sprUnknown | 0 | Unknown or undefined processing result |
| sprSuccess | 1 | The processing completed successfully. No tangible output has been generated (e.g. an artifact was resolved and acknowledged, but nothing needs to be sent to the browser). |
| sprSAMLMessage | 2 | The processing was fully or partially successful. The output contains a new SAML message that needs to be conveyed to the other SAML party. |
| sprSignOnPage | 3 | The processing was fully or partially successful. The output contains or redirects to a SAML login page. |
| sprResource | 4 | The processing was fully or partially successful. The output contains, or redirects to, a generic web resource. |
| sprSAMLError | 5 | The processing failed due to SAML-related issue (bad sign-on parameters, unknown principal etc.). The output contains a SAML error message. This still needs to be relayed to the other SAML party. |
| sprTransportError | 6 | The operation could not be completed due to an issue with configuration (e.g. non-existent SAML endpoint), permissions, or network. The SAML protocol could not commence. The output contains a transport-layer (HTTP) error message which can/should be displayed to the user in the browser. |
You can use this method with or without the OfflineMode.
Note: this method is currently in development and will be available in later SecureBlackbox updates.
ProcessAssertion Method (SAMLSPServer Component)
Processes assertion received from the IdP service at one of the ACS endpoints.
Syntax
Remarks
Use this method to pass a SAML assertion received at one of the AssertionConsumerService endpoints.
This method returns the processing result as one of the values given below. Right before it returns it passes the processing results back to the caller via the ProcessingCompleted event. This event fires independently of the processing outcome (success or failure), and contains the same ConnectionID that is passed to this call.
| sprUnknown | 0 | Unknown or undefined processing result |
| sprSuccess | 1 | The processing completed successfully. No tangible output has been generated (e.g. an artifact was resolved and acknowledged, but nothing needs to be sent to the browser). |
| sprSAMLMessage | 2 | The processing was fully or partially successful. The output contains a new SAML message that needs to be conveyed to the other SAML party. |
| sprSignOnPage | 3 | The processing was fully or partially successful. The output contains or redirects to a SAML login page. |
| sprResource | 4 | The processing was fully or partially successful. The output contains, or redirects to, a generic web resource. |
| sprSAMLError | 5 | The processing failed due to SAML-related issue (bad sign-on parameters, unknown principal etc.). The output contains a SAML error message. This still needs to be relayed to the other SAML party. |
| sprTransportError | 6 | The operation could not be completed due to an issue with configuration (e.g. non-existent SAML endpoint), permissions, or network. The SAML protocol could not commence. The output contains a transport-layer (HTTP) error message which can/should be displayed to the user in the browser. |
You can use this method with or without the OfflineMode.
ProcessGenericRequest Method (SAMLSPServer Component)
Processes a generic HTTP SAML request.
Syntax
Remarks
Use this method to process a generic well-formed HTTP SAML request obtained elsewhere. This is a handy mechanism to bind the SAML processor to an external web engine.
The Request parameter is expected to contain a full HTTP request, including the HTTP method string (GET, POST) and all the headers. The generated response contains a full HTTP response that should be supplied back to the requestor. You can edit some parts of the response (for example, by adding some custom HTTP headers).
You can use this method with or without the OfflineMode.
ProcessLogoutRequest Method (SAMLSPServer Component)
Processes logout request received from the IdP service at one of the SLS endpoints.
Syntax
Remarks
Use this method to pass a SAML logout request received at one of the SingleLogoutService endpoints.
An SLS endpoint may receive requests of two kinds: LogoutRequest and LogoutResponse. If Request contains a LogoutRequest, the content generated by this method will contain a corresponding LogoutResponse. If Request contains a LogoutResponse, the generated content is empty.
This method returns the processing result as one of the values given below. Right before it returns it passes the processing results back to the caller via the ProcessingCompleted event. This event fires independently of the processing outcome (success or failure), and contains the same ConnectionID that is passed to this call.
| sprUnknown | 0 | Unknown or undefined processing result |
| sprSuccess | 1 | The processing completed successfully. No tangible output has been generated (e.g. an artifact was resolved and acknowledged, but nothing needs to be sent to the browser). |
| sprSAMLMessage | 2 | The processing was fully or partially successful. The output contains a new SAML message that needs to be conveyed to the other SAML party. |
| sprSignOnPage | 3 | The processing was fully or partially successful. The output contains or redirects to a SAML login page. |
| sprResource | 4 | The processing was fully or partially successful. The output contains, or redirects to, a generic web resource. |
| sprSAMLError | 5 | The processing failed due to SAML-related issue (bad sign-on parameters, unknown principal etc.). The output contains a SAML error message. This still needs to be relayed to the other SAML party. |
| sprTransportError | 6 | The operation could not be completed due to an issue with configuration (e.g. non-existent SAML endpoint), permissions, or network. The SAML protocol could not commence. The output contains a transport-layer (HTTP) error message which can/should be displayed to the user in the browser. |
You can use this method with or without the OfflineMode.
Reset Method (SAMLSPServer Component)
Resets the component settings.
Syntax
public void Reset();
Public Sub Reset()
Remarks
Reset is a generic method available in every component.
SetClientBuffer Method (SAMLSPServer Component)
Commits a data buffer to the connection.
Syntax
Remarks
Use this method from your ReadFile event handler to commit a chunk of file data to the server component.
SetProviderProperty Method (SAMLSPServer Component)
Sets the value of a custom provider property.
Syntax
Remarks
This method, together with GetProviderProperty, provides an extensible way of managing the Service Provider's settings that are not available through the primary properties of the component. As SAML usage scenarios evolve and new providers appear, the list of supported properties can be extended.
The following properties are currently supported:
- ContactPerson
- OrganizationName
- OrganizationDisplayName
- OrganizationURL
- OrganizationLang
SetResponseHeader Method (SAMLSPServer Component)
Sets a response header.
Syntax
Remarks
Use this method to set a response header. A good place to call this method is a request-marking event, such as GetRequest or PostRequest.
SetSessionProperty Method (SAMLSPServer Component)
Sets the value of a custom provider session property.
Syntax
Remarks
This method, together with GetSessionProperty, provides an extensible way of managing the Service Provider's session settings that are not available through the primary properties and events of the component.
The following properties can be adjusted for each individual session:
- AuthnRequestID: the AuthnRequest ID.
- LogoutRequestID: the LogoutRequest ID.
- NameID: the NameID of the user.
- RelayState: the current (last) relay state entry.
- Session: the session ID (the same as you pass as parameter).
- SAMLSession: the browser cookie that corresponds to the session.
- SessionIndex: a collection of cross-network session indexes assigned to this session.
- URL: the current request's URL.
- UserData: the protocol-independent user data. Use this session property to store custom information associated with the session across contexts.
- Expires: the web session expiration time. Set it to a moment in the past to enforce immediate session expiration.
Note: setting a session property invokes a call to SessionStateSave. The component does that to update the session state kept externally.
Note: changing session properties mindlessly may break the protocol flow. For example, changing AuthnRequestID to a different value may cause the Service Provider to reject the subsequent assertion message, as the incoming assertion will contain a now-unmatching In-Response-To entry.
Start Method (SAMLSPServer Component)
Starts the SP server.
Syntax
public void Start();
Public Sub Start()
Remarks
Use this method to start listening for incoming connections.
Stop Method (SAMLSPServer Component)
Stops the IdP server.
Syntax
public void Stop();
Public Sub Stop()
Remarks
Call this method to stop listening for incoming connections.
Accept Event (SAMLSPServer Component)
Reports an incoming connection.
Syntax
public event OnAcceptHandler OnAccept; public delegate void OnAcceptHandler(object sender, SAMLSPServerAcceptEventArgs e); public class SAMLSPServerAcceptEventArgs : EventArgs { public string RemoteAddress { get; } public int RemotePort { get; } public bool Accept { get; set; } }
Public Event OnAccept As OnAcceptHandler Public Delegate Sub OnAcceptHandler(sender As Object, e As SAMLSPServerAcceptEventArgs) Public Class SAMLSPServerAcceptEventArgs Inherits EventArgs Public ReadOnly Property RemoteAddress As String Public ReadOnly Property RemotePort As Integer Public Property Accept As Boolean End Class
Remarks
This event is fired when a new connection from RemoteAddress:RemotePort is ready to be accepted. Use the Accept parameter to accept or decline it.
Subscribe to Connect event to be notified of every connection that has been set up.
ArtifactReceived Event (SAMLSPServer Component)
The server fires this event upon receiving an Artifact message from the other side.
Syntax
public event OnArtifactReceivedHandler OnArtifactReceived; public delegate void OnArtifactReceivedHandler(object sender, SAMLSPServerArtifactReceivedEventArgs e); public class SAMLSPServerArtifactReceivedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Issuer { get; } public string Artifact { get; } public int Action { get; set; } }
Public Event OnArtifactReceived As OnArtifactReceivedHandler Public Delegate Sub OnArtifactReceivedHandler(sender As Object, e As SAMLSPServerArtifactReceivedEventArgs) Public Class SAMLSPServerArtifactReceivedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Issuer As String Public ReadOnly Property Artifact As String Public Property Action As Integer End Class
Remarks
The Artifact message is very simple and only contains the actual artifact (an opaque string). Depending on the choice of the Action parameter, the further flow may go as following:
- fraAuto: the server will prepare an ArtifactResolve request and sent it to the other side to retrieve the artifact.
- fraCustom: the server will acknowledge the receipt of the artifact, but it is the task of your code to request the message and pass it on to the server via ProcessGenericRequest method.
- fraReject: the server will discard the artifact.
Note that you still can choose fraAuto to let the server proceed, but alter the flow as required in further events, such as ArtifactResolveRequestPrepared.
In OfflineMode this event would typically be fired from ProcessArtifact call.
ArtifactResolveRequestPrepared Event (SAMLSPServer Component)
This event is fired when a new artifact resolution request message has been prepared by the component.
Syntax
public event OnArtifactResolveRequestPreparedHandler OnArtifactResolveRequestPrepared; public delegate void OnArtifactResolveRequestPreparedHandler(object sender, SAMLSPServerArtifactResolveRequestPreparedEventArgs e); public class SAMLSPServerArtifactResolveRequestPreparedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Destination { get; } public string Artifact { get; } }
Public Event OnArtifactResolveRequestPrepared As OnArtifactResolveRequestPreparedHandler Public Delegate Sub OnArtifactResolveRequestPreparedHandler(sender As Object, e As SAMLSPServerArtifactResolveRequestPreparedEventArgs) Public Class SAMLSPServerArtifactResolveRequestPreparedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Destination As String Public ReadOnly Property Artifact As String End Class
Remarks
Subscribe to this event to be notified about preparation of artifact resolution requests. This is fired right after the resolution request has been prepared, and just before the component sends it out to the identity provider.
ArtifactResolveRequestReceived Event (SAMLSPServer Component)
Reports receipt of ArtifactResolveRequest message.
Syntax
public event OnArtifactResolveRequestReceivedHandler OnArtifactResolveRequestReceived; public delegate void OnArtifactResolveRequestReceivedHandler(object sender, SAMLSPServerArtifactResolveRequestReceivedEventArgs e); public class SAMLSPServerArtifactResolveRequestReceivedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Issuer { get; } public bool IsEncrypted { get; } public bool IsSigned { get; } public string Artifact { get; } public int Action { get; set; } }
Public Event OnArtifactResolveRequestReceived As OnArtifactResolveRequestReceivedHandler Public Delegate Sub OnArtifactResolveRequestReceivedHandler(sender As Object, e As SAMLSPServerArtifactResolveRequestReceivedEventArgs) Public Class SAMLSPServerArtifactResolveRequestReceivedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Issuer As String Public ReadOnly Property IsEncrypted As Boolean Public ReadOnly Property IsSigned As Boolean Public ReadOnly Property Artifact As String Public Property Action As Integer End Class
Remarks
The component fires this event to report receipt of incoming artifact resolution request. The Artifact parameter contains the artifact identifier received.
The application can choose to accept or reject the request, or process it manually, using the Action parameter:
| fraAuto | 1 | Handle the requested action automatically by the server |
| fraCustom | 2 | Override the action using the user code logic |
| fraAbort | 3 | Abort the requested action |
AssertionReceived Event (SAMLSPServer Component)
This event is fired when an assertion is received from the IdP.
Syntax
public event OnAssertionReceivedHandler OnAssertionReceived; public delegate void OnAssertionReceivedHandler(object sender, SAMLSPServerAssertionReceivedEventArgs e); public class SAMLSPServerAssertionReceivedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Issuer { get; } public string Body { get; } public bool IsEncrypted { get; } public bool IsSigned { get; } public string Auth { get; } public string NameID { get; } public string NameIDFormat { get; } public string SessionIndex { get; } public string Attributes { get; } public string ValidFrom { get; } public string ValidTo { get; } public string RelayState { get; } public int Action { get; set; } }
Public Event OnAssertionReceived As OnAssertionReceivedHandler Public Delegate Sub OnAssertionReceivedHandler(sender As Object, e As SAMLSPServerAssertionReceivedEventArgs) Public Class SAMLSPServerAssertionReceivedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Issuer As String Public ReadOnly Property Body As String Public ReadOnly Property IsEncrypted As Boolean Public ReadOnly Property IsSigned As Boolean Public ReadOnly Property Auth As String Public ReadOnly Property NameID As String Public ReadOnly Property NameIDFormat As String Public ReadOnly Property SessionIndex As String Public ReadOnly Property Attributes As String Public ReadOnly Property ValidFrom As String Public ReadOnly Property ValidTo As String Public ReadOnly Property RelayState As String Public Property Action As Integer End Class
Remarks
The AssertionReceived event notifies the application that an assertion has been received at the ACS endpoint. In OfflineMode this event may fire in response to a ProcessAssertion call. In online mode it can fire at any time while the server is active.
The ConnectionID and SessionID specify the IDs of the current client connection and HTTP session. The RequestID contains the ID of the original AuthnRequest message, if it was sent by the service provider. The IsEncrypted and IsSigned parameters indicate the security properties of the assertion. The NameID parameter contains the unique name identifier of the authenticated principal, and the SessionIndex contains the SAML session identifier. In rare cases SessionIndex may contain multiple indices, if the SP has more than one session at the IdP.
The application can choose to accept or reject the request, or process it manually, using the Action parameter:
| fraAuto | 1 | Handle the requested action automatically by the server |
| fraCustom | 2 | Override the action using the user code logic |
| fraAbort | 3 | Abort the requested action |
If the assertion is returned in response to this SP's AuthnRequest message, the RelayState parameter will contain the original relay state passed to the earlier InitiateAuth call.
AttributeQueryPrepared Event (SAMLSPServer Component)
Notifies the application of the preparation of an AttributeQuery.
Syntax
public event OnAttributeQueryPreparedHandler OnAttributeQueryPrepared; public delegate void OnAttributeQueryPreparedHandler(object sender, SAMLSPServerAttributeQueryPreparedEventArgs e); public class SAMLSPServerAttributeQueryPreparedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Destination { get; } public string NameID { get; } public string NameIDFormat { get; } public string Attributes { get; } }
Public Event OnAttributeQueryPrepared As OnAttributeQueryPreparedHandler Public Delegate Sub OnAttributeQueryPreparedHandler(sender As Object, e As SAMLSPServerAttributeQueryPreparedEventArgs) Public Class SAMLSPServerAttributeQueryPreparedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Destination As String Public ReadOnly Property NameID As String Public ReadOnly Property NameIDFormat As String Public ReadOnly Property Attributes As String End Class
Remarks
The component uses this event to notify the application of the completion of the preparation of the AttributeQuery message. The NameID and NameIDFormat parameters indicate the attribute subject, and the Attributes parameter contains a list of attributes being requested.
This event may be fired in response to a InitiateAttributeQuery call (in offline mode), or intermittently in online mode.
AuthnRequestPrepared Event (SAMLSPServer Component)
This event is fired when a new authentication request message has been prepared.
Syntax
public event OnAuthnRequestPreparedHandler OnAuthnRequestPrepared; public delegate void OnAuthnRequestPreparedHandler(object sender, SAMLSPServerAuthnRequestPreparedEventArgs e); public class SAMLSPServerAuthnRequestPreparedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Destination { get; } public string NameIDFormat { get; } public bool ForceAuthn { get; } public bool NonInteractive { get; } public string RelayState { get; set; } }
Public Event OnAuthnRequestPrepared As OnAuthnRequestPreparedHandler Public Delegate Sub OnAuthnRequestPreparedHandler(sender As Object, e As SAMLSPServerAuthnRequestPreparedEventArgs) Public Class SAMLSPServerAuthnRequestPreparedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Destination As String Public ReadOnly Property NameIDFormat As String Public ReadOnly Property ForceAuthn As Boolean Public ReadOnly Property NonInteractive As Boolean Public Property RelayState As String End Class
Remarks
Subscribe to this event to get notified about assertion requests prepared by the service provider. This event may fire from InitiateAuth method when working in OfflineMode, or at any time when working as a standalone live web server.
You can adjust the RelayState as required in the event handler to pass on a state to the IdP. The IdP will return this state back to you together with its authentication assertion.
Connect Event (SAMLSPServer Component)
Reports an accepted connection.
Syntax
public event OnConnectHandler OnConnect; public delegate void OnConnectHandler(object sender, SAMLSPServerConnectEventArgs e); public class SAMLSPServerConnectEventArgs : EventArgs { public long ConnectionId { get; } public string RemoteAddress { get; } public int RemotePort { get; } }
Public Event OnConnect As OnConnectHandler Public Delegate Sub OnConnectHandler(sender As Object, e As SAMLSPServerConnectEventArgs) Public Class SAMLSPServerConnectEventArgs Inherits EventArgs Public ReadOnly Property ConnectionId As Long Public ReadOnly Property RemoteAddress As String Public ReadOnly Property RemotePort As Integer End Class
Remarks
The component fires this event to report that a new connection has been established. ConnectionId indicates the unique ID assigned to this connection. The same ID will be supplied to any other events related to this connection, such as SessionClosed or SessionEstablished.
Disconnect Event (SAMLSPServer Component)
Fires to report a disconnected client.
Syntax
public event OnDisconnectHandler OnDisconnect; public delegate void OnDisconnectHandler(object sender, SAMLSPServerDisconnectEventArgs e); public class SAMLSPServerDisconnectEventArgs : EventArgs { public long ConnectionID { get; } }
Public Event OnDisconnect As OnDisconnectHandler Public Delegate Sub OnDisconnectHandler(sender As Object, e As SAMLSPServerDisconnectEventArgs) Public Class SAMLSPServerDisconnectEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long End Class
Remarks
The component fires this event when a connected client disconnects.
Encrypted Event (SAMLSPServer Component)
Notifies the application that the assertion is encrypted and provides recipient certificate details.
Syntax
public event OnEncryptedHandler OnEncrypted; public delegate void OnEncryptedHandler(object sender, SAMLSPServerEncryptedEventArgs e); public class SAMLSPServerEncryptedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string IssuerRDN { get; } public byte[] SerialNumber { get; } public byte[] SubjectKeyID { get; } public bool NeedCredential { get; } public bool SkipThis { get; set; } }
Public Event OnEncrypted As OnEncryptedHandler Public Delegate Sub OnEncryptedHandler(sender As Object, e As SAMLSPServerEncryptedEventArgs) Public Class SAMLSPServerEncryptedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property IssuerRDN As String Public ReadOnly Property SerialNumber As Byte() Public ReadOnly Property SubjectKeyID As Byte() Public ReadOnly Property NeedCredential As Boolean Public Property SkipThis As Boolean End Class
Remarks
The component fires this event when processing encrypted documents to report the fact of encryption and pass certificate parameters to the user.
This event fires repeatedly for each encryption mechanism used in the document until the user provides the correct credential via the DecryptionCertificate property (depending on encryption method used), or sets SkipThis to true.
The IssuerRDN, SerialNumber, and SubjectKeyID parameters provide the details of the encryption certificate. Note that the document can be encrypted with more than one certificate (or have "more than one recipient"), in which case each certificate will invoke its own OnEncrypted event loop.
The NeedCredential parameter specifies whether the correct credential is already available to the component or still needs to be set. One example where NeedCredential would be set to false is where it had been provided by the application prior to processing the document (e.g. by setting the DecryptionCertificate property to a known pre-defined value). If NeedCredential is set to true, you must provide the valid credential for the decryption process to succeed.
Error Event (SAMLSPServer Component)
Information about errors during data delivery.
Syntax
public event OnErrorHandler OnError; public delegate void OnErrorHandler(object sender, SAMLSPServerErrorEventArgs e); public class SAMLSPServerErrorEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public int ErrorCode { get; } public bool Fatal { get; } public bool Remote { get; } public string Description { get; } }
Public Event OnError As OnErrorHandler Public Delegate Sub OnErrorHandler(sender As Object, e As SAMLSPServerErrorEventArgs) Public Class SAMLSPServerErrorEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property ErrorCode As Integer Public ReadOnly Property Fatal As Boolean Public ReadOnly Property Remote As Boolean Public ReadOnly Property Description As String End Class
Remarks
The event is fired in case of exceptional conditions during message processing.
ErrorCode contains an error code and Description contains a textual description of the error. For a list of valid error codes and their descriptions, please refer to the section.
ExternalSign Event (SAMLSPServer Component)
Handles remote or external signing initiated by the server protocol.
Syntax
public event OnExternalSignHandler OnExternalSign; public delegate void OnExternalSignHandler(object sender, SAMLSPServerExternalSignEventArgs e); public class SAMLSPServerExternalSignEventArgs : EventArgs { public long ConnectionID { get; } public string OperationId { get; } public string HashAlgorithm { get; } public string Pars { get; } public string Data { get; } public string SignedData { get; set; } }
Public Event OnExternalSign As OnExternalSignHandler Public Delegate Sub OnExternalSignHandler(sender As Object, e As SAMLSPServerExternalSignEventArgs) Public Class SAMLSPServerExternalSignEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property OperationId As String Public ReadOnly Property HashAlgorithm As String Public ReadOnly Property Pars As String Public ReadOnly Property Data As String Public Property SignedData As String End Class
Remarks
Assign a handler to this event if you need to delegate a low-level signing operation to an external, remote, or custom signing engine. Depending on the settings, the handler will receive a hashed or unhashed value to be signed.
The event handler must pass the value of Data to the signer, obtain the signature, and pass it back to the component via the SignedData parameter.
OperationId provides a comment about the operation and its origin. It depends on the exact component being used, and may be empty. HashAlgorithm specifies the hash algorithm being used for the operation, and Pars contains algorithm-dependent parameters.
The component uses base16 (hex) encoding for the Data, SignedData, and Pars parameters. If your signing engine uses a different input and output encoding, you may need to decode and/or encode the data before and/or after the signing.
A sample MD5 hash encoded in base16: a0dee2a0382afbb09120ffa7ccd8a152 - lower case base16 A0DEE2A0382AFBB09120FFA7CCD8A152 - upper case base16
A sample event handler that uses the .NET RSACryptoServiceProvider class may look like the following:
signer.OnExternalSign += (s, e) =>
{
var cert = new X509Certificate2("cert.pfx", "", X509KeyStorageFlags.Exportable);
var key = (RSACryptoServiceProvider)cert.PrivateKey;
var dataToSign = e.Data.FromBase16String();
var signedData = key.SignHash(dataToSign, "2.16.840.1.101.3.4.2.1");
e.SignedData = signedData.ToBase16String();
};
LogoutRequestPrepared Event (SAMLSPServer Component)
This event is fired when a new logout request has been prepared.
Syntax
public event OnLogoutRequestPreparedHandler OnLogoutRequestPrepared; public delegate void OnLogoutRequestPreparedHandler(object sender, SAMLSPServerLogoutRequestPreparedEventArgs e); public class SAMLSPServerLogoutRequestPreparedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Destination { get; } public string NameID { get; } public string NameIDFormat { get; } public string SessionIndex { get; } public string RelayState { get; set; } }
Public Event OnLogoutRequestPrepared As OnLogoutRequestPreparedHandler Public Delegate Sub OnLogoutRequestPreparedHandler(sender As Object, e As SAMLSPServerLogoutRequestPreparedEventArgs) Public Class SAMLSPServerLogoutRequestPreparedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Destination As String Public ReadOnly Property NameID As String Public ReadOnly Property NameIDFormat As String Public ReadOnly Property SessionIndex As String Public Property RelayState As String End Class
Remarks
The component uses this event to report completion of the LogoutRequest preparation. The NameID, NameIDFormat, and SessionIndex parameters indicate the subject that is being logged out. The SP parameter references the service provider involved.
The RelayState contains the relay state value that is going to be passed with the LogoutRequest to the remote party and mirrored back (if the protocol supports it).
LogoutRequestReceived Event (SAMLSPServer Component)
The component uses this event to notify the application about an incoming SAML Logout Request message.
Syntax
public event OnLogoutRequestReceivedHandler OnLogoutRequestReceived; public delegate void OnLogoutRequestReceivedHandler(object sender, SAMLSPServerLogoutRequestReceivedEventArgs e); public class SAMLSPServerLogoutRequestReceivedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Issuer { get; } public bool IsEncrypted { get; } public bool IsSigned { get; } public string NameID { get; } public string NameIDFormat { get; } public string SessionIndex { get; } public int Action { get; set; } }
Public Event OnLogoutRequestReceived As OnLogoutRequestReceivedHandler Public Delegate Sub OnLogoutRequestReceivedHandler(sender As Object, e As SAMLSPServerLogoutRequestReceivedEventArgs) Public Class SAMLSPServerLogoutRequestReceivedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Issuer As String Public ReadOnly Property IsEncrypted As Boolean Public ReadOnly Property IsSigned As Boolean Public ReadOnly Property NameID As String Public ReadOnly Property NameIDFormat As String Public ReadOnly Property SessionIndex As String Public Property Action As Integer End Class
Remarks
The SAML SP server fires this event when a SAML logout request is received at a single logout service endpoint. The NameID, NameIDFormat, and SessionIndex parameters indicate the principal that is signing out.
The application can choose to accept or reject the request, or process it manually, using the Action parameter:
| fraAuto | 1 | Handle the requested action automatically by the server |
| fraCustom | 2 | Override the action using the user code logic |
| fraAbort | 3 | Abort the requested action |
LogoutResponsePrepared Event (SAMLSPServer Component)
The component uses this event to notify the application about the Logout Response message being ready to be sent.
Syntax
public event OnLogoutResponsePreparedHandler OnLogoutResponsePrepared; public delegate void OnLogoutResponsePreparedHandler(object sender, SAMLSPServerLogoutResponsePreparedEventArgs e); public class SAMLSPServerLogoutResponsePreparedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Destination { get; } public string Body { get; } public string NameID { get; } public string NameIDFormat { get; } public string SessionIndex { get; } }
Public Event OnLogoutResponsePrepared As OnLogoutResponsePreparedHandler Public Delegate Sub OnLogoutResponsePreparedHandler(sender As Object, e As SAMLSPServerLogoutResponsePreparedEventArgs) Public Class SAMLSPServerLogoutResponsePreparedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Destination As String Public ReadOnly Property Body As String Public ReadOnly Property NameID As String Public ReadOnly Property NameIDFormat As String Public ReadOnly Property SessionIndex As String End Class
Remarks
The IdP server fires this event when it has prepared a Logout Response message and is ready to send it out to the SP.
LogoutResponseReceived Event (SAMLSPServer Component)
The component uses this event to notify the application about an incoming SAML LogoutResponse message.
Syntax
public event OnLogoutResponseReceivedHandler OnLogoutResponseReceived; public delegate void OnLogoutResponseReceivedHandler(object sender, SAMLSPServerLogoutResponseReceivedEventArgs e); public class SAMLSPServerLogoutResponseReceivedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Issuer { get; } public bool IsEncrypted { get; } public bool IsSigned { get; } public string NameID { get; } public string NameIDFormat { get; } public string SessionIndex { get; } public string RelayState { get; } public int Action { get; set; } }
Public Event OnLogoutResponseReceived As OnLogoutResponseReceivedHandler Public Delegate Sub OnLogoutResponseReceivedHandler(sender As Object, e As SAMLSPServerLogoutResponseReceivedEventArgs) Public Class SAMLSPServerLogoutResponseReceivedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Issuer As String Public ReadOnly Property IsEncrypted As Boolean Public ReadOnly Property IsSigned As Boolean Public ReadOnly Property NameID As String Public ReadOnly Property NameIDFormat As String Public ReadOnly Property SessionIndex As String Public ReadOnly Property RelayState As String Public Property Action As Integer End Class
Remarks
The SAML SP server fires this event when a SAML logout response is received at a single logout service endpoint following the LogoutRequest sent earlier. The RelayState is a mirrored back value included in the request.
The NameID, NameIDFormat, and SessionIndex parameters indicate the principal that is signing out.
The application can choose to accept or reject the request, or process it manually, using the Action parameter:
| fraAuto | 1 | Handle the requested action automatically by the server |
| fraCustom | 2 | Override the action using the user code logic |
| fraAbort | 3 | Abort the requested action |
Notification Event (SAMLSPServer Component)
This event notifies the application about an underlying control flow event.
Syntax
public event OnNotificationHandler OnNotification; public delegate void OnNotificationHandler(object sender, SAMLSPServerNotificationEventArgs e); public class SAMLSPServerNotificationEventArgs : EventArgs { public string EventID { get; } public string EventParam { get; } }
Public Event OnNotification As OnNotificationHandler Public Delegate Sub OnNotificationHandler(sender As Object, e As SAMLSPServerNotificationEventArgs) Public Class SAMLSPServerNotificationEventArgs Inherits EventArgs Public ReadOnly Property EventID As String Public ReadOnly Property EventParam As String End Class
Remarks
The component fires this event to let the application know about some event, occurrence, or milestone in the component. For example, it may fire to report completion of the document processing. The list of events being reported is not fixed, and may be flexibly extended over time.
The unique identifier of the event is provided in the EventID parameter. EventParam contains any parameters accompanying the occurrence. Depending on the type of the component, the exact action it is performing, or the document being processed, one or both may be omitted.
This component can fire this event with the following EventID values:
| SAMLResponderError | TBD |
| SAMLSessionLogout | TBD |
| ListeningStarted | Notifies the application that the server has started listening for incoming connections. |
| ListeningStopped | Notifies the application that the server has stopped listening to incoming connections. |
ProcessingCompleted Event (SAMLSPServer Component)
This event notifies the application of the completion of request or response processing.
Syntax
public event OnProcessingCompletedHandler OnProcessingCompleted; public delegate void OnProcessingCompletedHandler(object sender, SAMLSPServerProcessingCompletedEventArgs e); public class SAMLSPServerProcessingCompletedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string Tag { get; } public int ProcessingResult { get; } public string Response { get; } public bool Redirect { get; } }
Public Event OnProcessingCompleted As OnProcessingCompletedHandler Public Delegate Sub OnProcessingCompletedHandler(sender As Object, e As SAMLSPServerProcessingCompletedEventArgs) Public Class SAMLSPServerProcessingCompletedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property Tag As String Public ReadOnly Property ProcessingResult As Integer Public ReadOnly Property Response As String Public ReadOnly Property Redirect As Boolean End Class
Remarks
The component fires ProcessingCompleted to notify the application about completion of an earlier initiated processing operation. It is only fired in OfflineMode in response to calls such as ProcessAssertion, ProcessLogoutRequest, or similar. The main purpose of this event is to notify the application of the outcomes of the processing and return any prepared SAML entity for subsequent relay to the browser.
This event is fired strictly once for each Process* call, with the ConnectionID matching the value passed to the Process* method.
The SessionID parameter contains the identifier of the current virtual session. It may differ to the value passed to the Process* method if the session information was provided on the fly via the SessionInfoNeeded event. The ProcessingResult indicates the type of deliverable that was created during the processing (see below for possible values). The Response parameter contains the body of the deliverable. This can take one of the forms:
- a self-submitting form containing a SAML message.
- a redirect URL.
- a SOAP XML response.
- an empty string if ProcessingResult is set to sprSuccess.
The Redirect parameter indicates whether the value of Response should be passed to the browser within the 302 Location header, or as a document body.
| sprUnknown | 0 | Unknown or undefined processing result |
| sprSuccess | 1 | The processing completed successfully. No tangible output has been generated (e.g. an artifact was resolved and acknowledged, but nothing needs to be sent to the browser). |
| sprSAMLMessage | 2 | The processing was fully or partially successful. The output contains a new SAML message that needs to be conveyed to the other SAML party. |
| sprSignOnPage | 3 | The processing was fully or partially successful. The output contains or redirects to a SAML login page. |
| sprResource | 4 | The processing was fully or partially successful. The output contains, or redirects to, a generic web resource. |
| sprSAMLError | 5 | The processing failed due to SAML-related issue (bad sign-on parameters, unknown principal etc.). The output contains a SAML error message. This still needs to be relayed to the other SAML party. |
| sprTransportError | 6 | The operation could not be completed due to an issue with configuration (e.g. non-existent SAML endpoint), permissions, or network. The SAML protocol could not commence. The output contains a transport-layer (HTTP) error message which can/should be displayed to the user in the browser. |
ReadArtifact Event (SAMLSPServer Component)
Requests content identified by an artifact from the application.
Syntax
public event OnReadArtifactHandler OnReadArtifact; public delegate void OnReadArtifactHandler(object sender, SAMLSPServerReadArtifactEventArgs e); public class SAMLSPServerReadArtifactEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RequestID { get; } public string Issuer { get; } public string Artifact { get; } public string Value { get; set; } public bool Skip { get; set; } }
Public Event OnReadArtifact As OnReadArtifactHandler Public Delegate Sub OnReadArtifactHandler(sender As Object, e As SAMLSPServerReadArtifactEventArgs) Public Class SAMLSPServerReadArtifactEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RequestID As String Public ReadOnly Property Issuer As String Public ReadOnly Property Artifact As String Public Property Value As String Public Property Skip As Boolean End Class
Remarks
The component fires this event to request the content matching Artifact from the application. This is normally happens within the artifact resolution protocol between the SP and the IdP server.
The application must provide the requested artifact content via the Value parameter. The application can choose not to provide the artifact content (for example, if it doesn't have it) by setting Skip to true.
ResourceClose Event (SAMLSPServer Component)
Tells the application that it can close the opened resource.
Syntax
public event OnResourceCloseHandler OnResourceClose; public delegate void OnResourceCloseHandler(object sender, SAMLSPServerResourceCloseEventArgs e); public class SAMLSPServerResourceCloseEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string Handle { get; } }
Public Event OnResourceClose As OnResourceCloseHandler Public Delegate Sub OnResourceCloseHandler(sender As Object, e As SAMLSPServerResourceCloseEventArgs) Public Class SAMLSPServerResourceCloseEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property Handle As String End Class
Remarks
The component uses this event to notify the application that it can now close the resource opened earlier in its ResourceOpen handler.
ResourceOpen Event (SAMLSPServer Component)
Requests the application to open the requested resource.
Syntax
public event OnResourceOpenHandler OnResourceOpen; public delegate void OnResourceOpenHandler(object sender, SAMLSPServerResourceOpenEventArgs e); public class SAMLSPServerResourceOpenEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string URL { get; } public string HttpMethod { get; } public int OperationStatus { get; set; } public string Handle { get; set; } }
Public Event OnResourceOpen As OnResourceOpenHandler Public Delegate Sub OnResourceOpenHandler(sender As Object, e As SAMLSPServerResourceOpenEventArgs) Public Class SAMLSPServerResourceOpenEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property URL As String Public ReadOnly Property HttpMethod As String Public Property OperationStatus As Integer Public Property Handle As String End Class
Remarks
The component fires this event in virtualized mode if the application had returned the fraCustom modifier from the earlier ResourceRequest event call. Your code is expected to open the requested resource and be prepared to read from it in subsequent ResourceRead event calls. Check the operation status, and alter it, if needed, through the OperationStatus parameter:
| ostOk | 1 | |
| ostNoSuchFile | 2 | |
| ostAccessDenied | 3 | |
| ostWriteProtect | 4 | |
| ostUnsupported | 5 | |
| ostInvalidParameter | 6 | |
| ostEOF | 7 |
ResourceRead Event (SAMLSPServer Component)
Requests the application to read from an opened resource.
Syntax
public event OnResourceReadHandler OnResourceRead; public delegate void OnResourceReadHandler(object sender, SAMLSPServerResourceReadEventArgs e); public class SAMLSPServerResourceReadEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string Handle { get; } public int Size { get; } public int OperationStatus { get; set; } }
Public Event OnResourceRead As OnResourceReadHandler Public Delegate Sub OnResourceReadHandler(sender As Object, e As SAMLSPServerResourceReadEventArgs) Public Class SAMLSPServerResourceReadEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property Handle As String Public ReadOnly Property Size As Integer Public Property OperationStatus As Integer End Class
Remarks
The component fires this event in virtualized mode to request another chunk of data from the resource opened earlier. The handler of this event should read up to Size bytes from the object, and pass them to the component with a SetClientBuffer call.
Use the OperationStatus parameter to return the operation result back to the server. When the file has been read up to its end, set OperationStatus to ostEOF to tell the components that no more ResourceRead calls are needed.
Set OperationStatus to one of the following values:
| ostOk | 1 | |
| ostNoSuchFile | 2 | |
| ostAccessDenied | 3 | |
| ostWriteProtect | 4 | |
| ostUnsupported | 5 | |
| ostInvalidParameter | 6 | |
| ostEOF | 7 |
ResourceRequest Event (SAMLSPServer Component)
Notifies the application that a server resource is requested.
Syntax
public event OnResourceRequestHandler OnResourceRequest; public delegate void OnResourceRequestHandler(object sender, SAMLSPServerResourceRequestEventArgs e); public class SAMLSPServerResourceRequestEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string URL { get; } public string HttpMethod { get; } public bool ResProtected { get; set; } public bool ResSpecial { get; set; } public bool AllowWriting { get; set; } public int Action { get; set; } }
Public Event OnResourceRequest As OnResourceRequestHandler Public Delegate Sub OnResourceRequestHandler(sender As Object, e As SAMLSPServerResourceRequestEventArgs) Public Class SAMLSPServerResourceRequestEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property URL As String Public ReadOnly Property HttpMethod As String Public Property ResProtected As Boolean Public Property ResSpecial As Boolean Public Property AllowWriting As Boolean Public Property Action As Integer End Class
Remarks
The component uses this event to notify the application that the connection has requested a server resource.
The URL parameter specifies the resource requested. ResProtected is set to true if the resource is protected by SAML. ResSpecial is set to true if the request is a SAML resource, such as the metadata or an Assertion Consumer Service page. ConnectionID identifies the connected client.
Set Action to fraAuto to let the server handle the request automatically, or to fraCustom to handle the request in your code ('virtualize' the request).
Choose Action as one of the following values:
| fraAuto | 1 | Handle the requested action automatically by the server |
| fraCustom | 2 | Override the action using the user code logic |
| fraAbort | 3 | Abort the requested action |
ResourceWrite Event (SAMLSPServer Component)
Requests the application to write to an opened resource.
Syntax
public event OnResourceWriteHandler OnResourceWrite; public delegate void OnResourceWriteHandler(object sender, SAMLSPServerResourceWriteEventArgs e); public class SAMLSPServerResourceWriteEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string Handle { get; } public int OperationStatus { get; set; } }
Public Event OnResourceWrite As OnResourceWriteHandler Public Delegate Sub OnResourceWriteHandler(sender As Object, e As SAMLSPServerResourceWriteEventArgs) Public Class SAMLSPServerResourceWriteEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property Handle As String Public Property OperationStatus As Integer End Class
Remarks
The component fires this event in virtualized mode to pass another chunk of data to a resource opened earlier. This event is called for write-enabled requests, such as POST or PUT. The handler of this event should read the pending data using the GetClientBuffer method and write them to the opened file descriptor.
Use the OperationStatus parameter to return the operation result back to the server:
| ostOk | 1 | |
| ostNoSuchFile | 2 | |
| ostAccessDenied | 3 | |
| ostWriteProtect | 4 | |
| ostUnsupported | 5 | |
| ostInvalidParameter | 6 | |
| ostEOF | 7 |
SAMLMessagePrepared Event (SAMLSPServer Component)
This event is fired when a SAML message has been prepared and is ready to be dispatched.
Syntax
public event OnSAMLMessagePreparedHandler OnSAMLMessagePrepared; public delegate void OnSAMLMessagePreparedHandler(object sender, SAMLSPServerSAMLMessagePreparedEventArgs e); public class SAMLSPServerSAMLMessagePreparedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string MessageID { get; } public string Destination { get; } public string IssueInstant { get; } public string InResponseTo { get; } public string RequestBody { get; } public string MessageType { get; } public string MessageBody { get; set; } public string RelayState { get; set; } public bool Success { get; set; } }
Public Event OnSAMLMessagePrepared As OnSAMLMessagePreparedHandler Public Delegate Sub OnSAMLMessagePreparedHandler(sender As Object, e As SAMLSPServerSAMLMessagePreparedEventArgs) Public Class SAMLSPServerSAMLMessagePreparedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property MessageID As String Public ReadOnly Property Destination As String Public ReadOnly Property IssueInstant As String Public ReadOnly Property InResponseTo As String Public ReadOnly Property RequestBody As String Public ReadOnly Property MessageType As String Public Property MessageBody As String Public Property RelayState As String Public Property Success As Boolean End Class
Remarks
Subscribe to this event to be notified about every SAML message that has been prepared by the server. This event is fired for every type of the outgoing message (e.g. SAMLResponse or LogoutRequest). The InResponseTo contains the ID of the message in response to which the current message is sent (if applicable). The RequestBody parameter contains the body of such request.
The MessageType parameter indicates the type of the message that has been prepared, such as SAMLResponse. The MessageBody contains the XML body of the message. The Success parameter indicates whether the message contains a positive statement or an error. Both the MessageBody and Success parameters are adjustable.
SAMLMessageReceived Event (SAMLSPServer Component)
The server fires this event for every SAML message it receives.
Syntax
public event OnSAMLMessageReceivedHandler OnSAMLMessageReceived; public delegate void OnSAMLMessageReceivedHandler(object sender, SAMLSPServerSAMLMessageReceivedEventArgs e); public class SAMLSPServerSAMLMessageReceivedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string MessageID { get; } public string Issuer { get; } public string IssueInstant { get; } public string InResponseTo { get; } public string RequestBody { get; } public string MessageType { get; } public string MessageBody { get; } public bool IsSigned { get; } public string RelayState { get; } public int Action { get; set; } }
Public Event OnSAMLMessageReceived As OnSAMLMessageReceivedHandler Public Delegate Sub OnSAMLMessageReceivedHandler(sender As Object, e As SAMLSPServerSAMLMessageReceivedEventArgs) Public Class SAMLSPServerSAMLMessageReceivedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property MessageID As String Public ReadOnly Property Issuer As String Public ReadOnly Property IssueInstant As String Public ReadOnly Property InResponseTo As String Public ReadOnly Property RequestBody As String Public ReadOnly Property MessageType As String Public ReadOnly Property MessageBody As String Public ReadOnly Property IsSigned As Boolean Public ReadOnly Property RelayState As String Public Property Action As Integer End Class
Remarks
Subscribe to this event to be notified about incoming SAML messages.
The MessageType, MessageID, Issuer, and MessageBody parameters provide the details of the message received. The RequestBody and InResponseTo contain a reference to the request that this message is a response to (if any).
Set Action property as required to let the component know how to proceed.
| fraAuto | 1 | Handle the requested action automatically by the server |
| fraCustom | 2 | Override the action using the user code logic |
| fraAbort | 3 | Abort the requested action |
SessionCreated Event (SAMLSPServer Component)
This event is fired when a new session has been established.
Syntax
public event OnSessionCreatedHandler OnSessionCreated; public delegate void OnSessionCreatedHandler(object sender, SAMLSPServerSessionCreatedEventArgs e); public class SAMLSPServerSessionCreatedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } }
Public Event OnSessionCreated As OnSessionCreatedHandler Public Delegate Sub OnSessionCreatedHandler(sender As Object, e As SAMLSPServerSessionCreatedEventArgs) Public Class SAMLSPServerSessionCreatedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String End Class
Remarks
ConnectionID contains the identifier of the new session, SessionID specifies the ID of the new session.
SessionDestroyed Event (SAMLSPServer Component)
This event is fired when the SP server has closed a session.
Syntax
public event OnSessionDestroyedHandler OnSessionDestroyed; public delegate void OnSessionDestroyedHandler(object sender, SAMLSPServerSessionDestroyedEventArgs e); public class SAMLSPServerSessionDestroyedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } }
Public Event OnSessionDestroyed As OnSessionDestroyedHandler Public Delegate Sub OnSessionDestroyedHandler(sender As Object, e As SAMLSPServerSessionDestroyedEventArgs) Public Class SAMLSPServerSessionDestroyedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String End Class
Remarks
ConnectionID contains the identifier of the closed session.
SessionEvent Event (SAMLSPServer Component)
Notifies the application about SAML session events.
Syntax
public event OnSessionEventHandler OnSessionEvent; public delegate void OnSessionEventHandler(object sender, SAMLSPServerSessionEventEventArgs e); public class SAMLSPServerSessionEventEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string EventText { get; } }
Public Event OnSessionEvent As OnSessionEventHandler Public Delegate Sub OnSessionEventHandler(sender As Object, e As SAMLSPServerSessionEventEventArgs) Public Class SAMLSPServerSessionEventEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property EventText As String End Class
Remarks
component uses this event to notify your code about events that happen within the lifeline of a SAML session. Handling it may be useful for development, logging, and monitoring purposes.
The SessionID parameter specifies the session ID, and the EventText parameter describes the event that happened. Below are a few typical examples of what EventText you can expect to get:
- Start
- AuthnRequestPrepared
- ResponseReceived
- ResourceSupplied
- LogoutRequestPrepared
- LogoutResponseReceived
- LogoutRequestReceived
- LogoutResponsePrepared
- ArtifactResolveRequestReceived
- ArtifactResponsePrepared
- Finish
SessionInfoNeeded Event (SAMLSPServer Component)
This event is fired in OfflineMode to request the session ID for the current flow.
Syntax
public event OnSessionInfoNeededHandler OnSessionInfoNeeded; public delegate void OnSessionInfoNeededHandler(object sender, SAMLSPServerSessionInfoNeededEventArgs e); public class SAMLSPServerSessionInfoNeededEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; set; } }
Public Event OnSessionInfoNeeded As OnSessionInfoNeededHandler Public Delegate Sub OnSessionInfoNeededHandler(sender As Object, e As SAMLSPServerSessionInfoNeededEventArgs) Public Class SAMLSPServerSessionInfoNeededEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public Property SessionID As String End Class
Remarks
SAML protocol is stateful, which means that SAML services need to keep session-related information between connections. When used in online mode - where the components listen and serve connections automatically - the components can use HTTP cookies to track connecting clients and maintain the session store at the background. However, when used in offline mode, the components do not have access to the HTTP layer and live too short for the session store to survive. That is why in offline mode the components rely on the application code to keep the session information for them.
The components use a collection of Session* events to exchange session information with the application:
- SessionCreated is called when the component establishes a new session. In offline mode, the application should associate the session ID with the connected user, for example by returning it as a cookie.
- SessionStateSave : the component passes the session state to the application and expects that the application saves it somewhere to return it back to the component at its request at some point in the future. The session state is an opaque string. The application can use a hash table to store a collection of (SessionID, SessionState) pairs over the lifetime of the SAML service. The server may fire SessionStateSave multiple times for the same SessionID. If this happens, the existing SessionID entry should be overwritten with the fresh session data.
- SessionStateRetrieve : the component passes a session ID to the application and expects it to return the session state saved in the hash table earlier. The application should not delete the state from the hash table, as it may be needed again.
- SessionInfoNeeded (this event): the component expects the application to return the session ID corresponding to the connection ID back to them. This event fires, for example, if the application calls ProcessLogoutRequest but passes an empty SessionID as a parameter.
- SessionDestroyed is called when a session is destroyed. The component can remove the session from the hash table upon receiving this event.
SessionStateRetrieve Event (SAMLSPServer Component)
This event fires to retrieve session state information from the application.
Syntax
public event OnSessionStateRetrieveHandler OnSessionStateRetrieve; public delegate void OnSessionStateRetrieveHandler(object sender, SAMLSPServerSessionStateRetrieveEventArgs e); public class SAMLSPServerSessionStateRetrieveEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string SessionState { get; set; } }
Public Event OnSessionStateRetrieve As OnSessionStateRetrieveHandler Public Delegate Sub OnSessionStateRetrieveHandler(sender As Object, e As SAMLSPServerSessionStateRetrieveEventArgs) Public Class SAMLSPServerSessionStateRetrieveEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public Property SessionState As String End Class
Remarks
The component fires this event to request a session state that was previously provided to the application via the SessionStateSave call.
See the SessionInfoNeeded topic for more details about session management in offline mode.
SessionStateSave Event (SAMLSPServer Component)
This event passes a session state object to the application for safekeeping.
Syntax
public event OnSessionStateSaveHandler OnSessionStateSave; public delegate void OnSessionStateSaveHandler(object sender, SAMLSPServerSessionStateSaveEventArgs e); public class SAMLSPServerSessionStateSaveEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string SessionState { get; } }
Public Event OnSessionStateSave As OnSessionStateSaveHandler Public Delegate Sub OnSessionStateSaveHandler(sender As Object, e As SAMLSPServerSessionStateSaveEventArgs) Public Class SAMLSPServerSessionStateSaveEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property SessionState As String End Class
Remarks
The component fires this event to pass a session state to the application. The application is expected to save the state object (which is an opaque string) in a hash table, and be ready to return it back to the component when it requests it using a SessionStateRetrieve call.
See the SessionInfoNeeded topic for more details about session management in offline mode.
SignatureFound Event (SAMLSPServer Component)
Signifies the start of signature validation.
Syntax
public event OnSignatureFoundHandler OnSignatureFound; public delegate void OnSignatureFoundHandler(object sender, SAMLSPServerSignatureFoundEventArgs e); public class SAMLSPServerSignatureFoundEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public int Scope { get; } public string Signer { get; } public string TargetID { get; } public string TargetType { get; } public string IssuerRDN { get; } public byte[] SerialNumber { get; } public byte[] SubjectKeyID { get; } public string SigMethod { get; } public string DigestMethod { get; } public bool CertFound { get; } public bool Validate { get; set; } }
Public Event OnSignatureFound As OnSignatureFoundHandler Public Delegate Sub OnSignatureFoundHandler(sender As Object, e As SAMLSPServerSignatureFoundEventArgs) Public Class SAMLSPServerSignatureFoundEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property Scope As Integer Public ReadOnly Property Signer As String Public ReadOnly Property TargetID As String Public ReadOnly Property TargetType As String Public ReadOnly Property IssuerRDN As String Public ReadOnly Property SerialNumber As Byte() Public ReadOnly Property SubjectKeyID As Byte() Public ReadOnly Property SigMethod As String Public ReadOnly Property DigestMethod As String Public ReadOnly Property CertFound As Boolean Public Property Validate As Boolean End Class
Remarks
This event tells the application that signature validation is about to start, and provides the details about the signer's certificate via its IssuerRDN, SerialNumber, and SubjectKeyID parameters. It fires for every signature located in the verified message.
The Scope parameter specifies the subject of the signature. This can be the outermost SAML message or an embedded assertion.
| sssUnknown | 0 | The scope of signature is unknown |
| sssMessage | 1 | The signature covers the entire SAML message |
| sssAssertion | 2 | The signature covers an assertion |
| sssBinding | 3 | The signature covers the binding |
The details of the reported signature are populated in the Security object. For assertion signatures, you can update the details by pinning the assertion.
The CertFound is set to True if the component has found the needed certificate in one of the known locations, and to False otherwise, in which case you must provide it manually via KnownCertificates property.
Signature validation consists of two independent stages: cryptographic signature validation and chain validation. SAMLReader only supports signature validation. To validate the chain, grab the signing certificate from the SigningCertificate property and the associated certificates from the Certificates collection, and pass them to the CertificateValidator component to validate its chain.
Use the Validate parameter to tell the reader whether it should validate the signature.
SignatureValidated Event (SAMLSPServer Component)
Reports the signature validation result.
Syntax
public event OnSignatureValidatedHandler OnSignatureValidated; public delegate void OnSignatureValidatedHandler(object sender, SAMLSPServerSignatureValidatedEventArgs e); public class SAMLSPServerSignatureValidatedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public int Scope { get; } public string Signer { get; } public string TargetID { get; } public string TargetType { get; } public string IssuerRDN { get; } public byte[] SerialNumber { get; } public byte[] SubjectKeyID { get; } public string SigMethod { get; } public string DigestMethod { get; } public int ValidationResult { get; set; } }
Public Event OnSignatureValidated As OnSignatureValidatedHandler Public Delegate Sub OnSignatureValidatedHandler(sender As Object, e As SAMLSPServerSignatureValidatedEventArgs) Public Class SAMLSPServerSignatureValidatedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property Scope As Integer Public ReadOnly Property Signer As String Public ReadOnly Property TargetID As String Public ReadOnly Property TargetType As String Public ReadOnly Property IssuerRDN As String Public ReadOnly Property SerialNumber As Byte() Public ReadOnly Property SubjectKeyID As Byte() Public ReadOnly Property SigMethod As String Public ReadOnly Property DigestMethod As String Public Property ValidationResult As Integer End Class
Remarks
This event is fired when the complete XML signature validation process is finished.
The Scope parameter specifies the subject of the signature. This can be the outermost SAML message or an embedded assertion.
| sssUnknown | 0 | The scope of signature is unknown |
| sssMessage | 1 | The signature covers the entire SAML message |
| sssAssertion | 2 | The signature covers an assertion |
| sssBinding | 3 | The signature covers the binding |
| svtValid | 0 | The signature is valid |
| svtUnknown | 1 | Signature validity is unknown |
| svtCorrupted | 2 | The signature is corrupted |
| svtSignerNotFound | 3 | Failed to acquire the signing certificate. The signature cannot be validated. |
| svtFailure | 4 | General failure |
| svtReferenceCorrupted | 5 | Reference corrupted (XML-based signatures only) |
TLSCertValidate Event (SAMLSPServer Component)
Fires when a client certificate needs to be validated.
Syntax
public event OnTLSCertValidateHandler OnTLSCertValidate; public delegate void OnTLSCertValidateHandler(object sender, SAMLSPServerTLSCertValidateEventArgs e); public class SAMLSPServerTLSCertValidateEventArgs : EventArgs { public long ConnectionID { get; } public bool Accept { get; set; } }
Public Event OnTLSCertValidate As OnTLSCertValidateHandler Public Delegate Sub OnTLSCertValidateHandler(sender As Object, e As SAMLSPServerTLSCertValidateEventArgs) Public Class SAMLSPServerTLSCertValidateEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public Property Accept As Boolean End Class
Remarks
The component fires this event to notify the application of an authenticating client. Use the event handler to validate the certificate and pass your decision back to the server component via the Accept parameter.
TLSEstablished Event (SAMLSPServer Component)
Reports the setup of a TLS session.
Syntax
public event OnTLSEstablishedHandler OnTLSEstablished; public delegate void OnTLSEstablishedHandler(object sender, SAMLSPServerTLSEstablishedEventArgs e); public class SAMLSPServerTLSEstablishedEventArgs : EventArgs { public long ConnectionID { get; } }
Public Event OnTLSEstablished As OnTLSEstablishedHandler Public Delegate Sub OnTLSEstablishedHandler(sender As Object, e As SAMLSPServerTLSEstablishedEventArgs) Public Class SAMLSPServerTLSEstablishedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long End Class
Remarks
Subscribe to this event to be notified about the setup of a TLS connection by a connected client.
TLSHandshake Event (SAMLSPServer Component)
Fires when a newly established client connection initiates a TLS handshake.
Syntax
public event OnTLSHandshakeHandler OnTLSHandshake; public delegate void OnTLSHandshakeHandler(object sender, SAMLSPServerTLSHandshakeEventArgs e); public class SAMLSPServerTLSHandshakeEventArgs : EventArgs { public long ConnectionID { get; } public string ServerName { get; } public bool Abort { get; set; } }
Public Event OnTLSHandshake As OnTLSHandshakeHandler Public Delegate Sub OnTLSHandshakeHandler(sender As Object, e As SAMLSPServerTLSHandshakeEventArgs) Public Class SAMLSPServerTLSHandshakeEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property ServerName As String Public Property Abort As Boolean End Class
Remarks
Use this event to get notified about the initiation of the TLS handshake by the remote client. The ServerName parameter specifies the requested host from the client hello message.
TLSPSK Event (SAMLSPServer Component)
Requests a pre-shared key for TLS-PSK.
Syntax
public event OnTLSPSKHandler OnTLSPSK; public delegate void OnTLSPSKHandler(object sender, SAMLSPServerTLSPSKEventArgs e); public class SAMLSPServerTLSPSKEventArgs : EventArgs { public long ConnectionID { get; } public string Identity { get; } public string PSK { get; set; } public string Ciphersuite { get; set; } }
Public Event OnTLSPSK As OnTLSPSKHandler Public Delegate Sub OnTLSPSKHandler(sender As Object, e As SAMLSPServerTLSPSKEventArgs) Public Class SAMLSPServerTLSPSKEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property Identity As String Public Property PSK As String Public Property Ciphersuite As String End Class
Remarks
The component fires this event to report that a client has requested a TLS-PSK negotiation. ConnectionId indicates the unique connection ID that requested the PSK handshake.
Use Identity to look up for the corresponding pre-shared key in the server's database, then assign the key to the PSK parameter. If TLS 1.3 PSK is used, you will also need to assign the Ciphersuite parameter with the cipher suite associated with that identity and their key.
TLSShutdown Event (SAMLSPServer Component)
Reports closure of a TLS session.
Syntax
public event OnTLSShutdownHandler OnTLSShutdown; public delegate void OnTLSShutdownHandler(object sender, SAMLSPServerTLSShutdownEventArgs e); public class SAMLSPServerTLSShutdownEventArgs : EventArgs { public long ConnectionID { get; } }
Public Event OnTLSShutdown As OnTLSShutdownHandler Public Delegate Sub OnTLSShutdownHandler(sender As Object, e As SAMLSPServerTLSShutdownEventArgs) Public Class SAMLSPServerTLSShutdownEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long End Class
Remarks
The component fires this event when a connected client closes their TLS session gracefully. This event is typically followed by a Disconnect, which marks the closure of the underlying TCP session.
UserAuthCompleted Event (SAMLSPServer Component)
Notifies the application about the success of user authentication flow.
Syntax
public event OnUserAuthCompletedHandler OnUserAuthCompleted; public delegate void OnUserAuthCompletedHandler(object sender, SAMLSPServerUserAuthCompletedEventArgs e); public class SAMLSPServerUserAuthCompletedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string AssertionBody { get; } public string Auth { get; } public string NameID { get; } public string NameIDFormat { get; } public string SessionIndex { get; } public string ValidFrom { get; } public string ValidTo { get; } public string RelayState { get; } }
Public Event OnUserAuthCompleted As OnUserAuthCompletedHandler Public Delegate Sub OnUserAuthCompletedHandler(sender As Object, e As SAMLSPServerUserAuthCompletedEventArgs) Public Class SAMLSPServerUserAuthCompletedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property AssertionBody As String Public ReadOnly Property Auth As String Public ReadOnly Property NameID As String Public ReadOnly Property NameIDFormat As String Public ReadOnly Property SessionIndex As String Public ReadOnly Property ValidFrom As String Public ReadOnly Property ValidTo As String Public ReadOnly Property RelayState As String End Class
Remarks
Subscribe to this event to get notified about completion of user authentication flow. The NameID, NameIDFormat, SessionIndex, ValidFrom, and ValidTo parameters contain the session parameters as stated in the assertion, which is provided via the AssertionBody parameter. The Auth parameter contain the authentication mechanism used.
The RelayState matches the original relay state that was used on the initiation stage of the authentication.
UserAuthFailed Event (SAMLSPServer Component)
Notifies the application about failure of user authentication flow.
Syntax
public event OnUserAuthFailedHandler OnUserAuthFailed; public delegate void OnUserAuthFailedHandler(object sender, SAMLSPServerUserAuthFailedEventArgs e); public class SAMLSPServerUserAuthFailedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string RelayState { get; } }
Public Event OnUserAuthFailed As OnUserAuthFailedHandler Public Delegate Sub OnUserAuthFailedHandler(sender As Object, e As SAMLSPServerUserAuthFailedEventArgs) Public Class SAMLSPServerUserAuthFailedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property RelayState As String End Class
Remarks
The component fires this event to notify the application about failed user authentication flow. The RelayState parameter matches the one included with the AuthnRequest message.
UserAuthStart Event (SAMLSPServer Component)
Notifies the application about the start of user authentication flow.
Syntax
public event OnUserAuthStartHandler OnUserAuthStart; public delegate void OnUserAuthStartHandler(object sender, SAMLSPServerUserAuthStartEventArgs e); public class SAMLSPServerUserAuthStartEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public int IdPServiceIndex { get; } public string RelayState { get; set; } }
Public Event OnUserAuthStart As OnUserAuthStartHandler Public Delegate Sub OnUserAuthStartHandler(sender As Object, e As SAMLSPServerUserAuthStartEventArgs) Public Class SAMLSPServerUserAuthStartEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property IdPServiceIndex As Integer Public Property RelayState As String End Class
Remarks
The component invokes this event to signal the start of the user authentication flow. This happens shortly before the component proceeds to generation of AuthnRequest message.
The RelayState is an arbitrary string that will be passed to the IdP and mirrored back with the assertion. It is typically used to remember the URL of the resource or page that kicked in the SAML authentication flow.
UserLogoutCompleted Event (SAMLSPServer Component)
Notifies the application about the completion of user logout flow.
Syntax
public event OnUserLogoutCompletedHandler OnUserLogoutCompleted; public delegate void OnUserLogoutCompletedHandler(object sender, SAMLSPServerUserLogoutCompletedEventArgs e); public class SAMLSPServerUserLogoutCompletedEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public string NameID { get; } public string SessionIndex { get; } public string RelayState { get; } }
Public Event OnUserLogoutCompleted As OnUserLogoutCompletedHandler Public Delegate Sub OnUserLogoutCompletedHandler(sender As Object, e As SAMLSPServerUserLogoutCompletedEventArgs) Public Class SAMLSPServerUserLogoutCompletedEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property NameID As String Public ReadOnly Property SessionIndex As String Public ReadOnly Property RelayState As String End Class
Remarks
Subscribe to this event to be notified about the completion of the logout flow.
UserLogoutStart Event (SAMLSPServer Component)
Notifies the application about the start of user logout flow.
Syntax
public event OnUserLogoutStartHandler OnUserLogoutStart; public delegate void OnUserLogoutStartHandler(object sender, SAMLSPServerUserLogoutStartEventArgs e); public class SAMLSPServerUserLogoutStartEventArgs : EventArgs { public long ConnectionID { get; } public string SessionID { get; } public int IdPServiceIndex { get; } public string NameID { get; } public string SessionIndex { get; } public bool Secondary { get; } public string RelayState { get; set; } }
Public Event OnUserLogoutStart As OnUserLogoutStartHandler Public Delegate Sub OnUserLogoutStartHandler(sender As Object, e As SAMLSPServerUserLogoutStartEventArgs) Public Class SAMLSPServerUserLogoutStartEventArgs Inherits EventArgs Public ReadOnly Property ConnectionID As Long Public ReadOnly Property SessionID As String Public ReadOnly Property IdPServiceIndex As Integer Public ReadOnly Property NameID As String Public ReadOnly Property SessionIndex As String Public ReadOnly Property Secondary As Boolean Public Property RelayState As String End Class
Remarks
Subscribe to this event to get notified about the start of the user logout flow.
The logout process can be initiated on either the SP or IdP side. This event is fired at the earliest opportunity that this fact becomes known to the service provider: from within the InitiateLogout method, ProcessLogoutRequest method, or upon receiving a logout request at the SLS endpoint.
Independently of the timing and the stage of this event, the subsequent flow is the same: the logout protocol is initiated. The application will be notified of the completion of the protocol using the UserLogoutCompleted event. Note that the UserLogoutCompleted event may not fire if the connectivity to the IdP is lost prematurely or the IdP chooses not to respond. Due to that, it is reasonable to consider the user as logged out immediately after the current event fires.
The IdPServiceIndex parameter contains the index of the IdP service in the IdPServices collection. NameID indicates the name identifier of the user that is being logged out, and SessionIndex contain the unique SAML session identifier. The Secondary flag indicates whether the the SP is responding to IdP-initiated logout request.
The RelayState parameter is an optional SP-generated token that the IdP will return back in its LogoutResponse message. This is often set to the destination page where the browser should be redirected upon completion of the signout process.
Certificate Type
Encapsulates an individual X.509 certificate.
Remarks
This type keeps and provides access to X.509 certificate details.
- Bytes
- CA
- CAKeyID
- CertType
- CRLDistributionPoints
- Curve
- Fingerprint
- FriendlyName
- HashAlgorithm
- Issuer
- IssuerRDN
- KeyAlgorithm
- KeyBits
- KeyFingerprint
- KeyUsage
- KeyValid
- OCSPLocations
- OCSPNoCheck
- Origin
- PolicyIDs
- PrivateKeyBytes
- PrivateKeyExists
- PrivateKeyExtractable
- PublicKeyBytes
- Qualified
- QualifiedStatements
- Qualifiers
- SelfSigned
- SerialNumber
- SigAlgorithm
- Source
- Subject
- SubjectAlternativeName
- SubjectKeyID
- SubjectRDN
- Valid
- ValidFrom
- ValidTo
Fields
Bytes
byte[] (read-only)
Default: ""
Returns the raw certificate data in DER format.
CA
bool
Default: False
Indicates whether the certificate has a CA capability. For the certificate to be considered a CA, it must have its Basic Constraints extension set with the CA indicator enabled.
Set this field when generating a new certificate to have its Basic Constraints extension generated automatically.
CAKeyID
byte[] (read-only)
Default: ""
A unique identifier (fingerprint) of the CA certificate's cryptographic key.
Authority Key Identifier is a certificate extension which allows identification of certificates belonging to the same issuer, but with different public keys. It is a de-facto standard to include this extension in all certificates to facilitate chain building.
This setting cannot be set when generating a certificate as it always derives from another certificate property. CertificateManager generates this setting automatically if enough information is available to it: for self-signed certificates, this value is copied from the SubjectKeyID setting, and for lower-level certificates, from the parent certificate's subject key ID extension.
CertType
CertTypes (read-only)
Default: 0
Returns the type of the entity contained in the Certificate object.
A Certificate object can contain two types of cryptographic objects: a ready-to-use X.509 certificate, or a certificate request ("an unsigned certificate"). Certificate requests can be upgraded to full certificates by signing them with a CA certificate.
Use the CertificateManager component to load or create new certificate and certificate requests objects.
CRLDistributionPoints
string
Default: ""
Contains a list of locations of CRL distribution points used to check this certificate's validity. The list is taken from the respective certificate extension.
Use this field when generating a certificate to provide a list of CRL endpoints that should be made part of the new certificate.
The endpoints are provided as a list of CRLF-separated URLs. Note that this differs from the behaviour used in earlier product versions, where the "|" character was used as the location separator.
Curve
string
Default: ""
Specifies the elliptic curve associated with the certificate's public key. This setting only applies to certificates containing EC keys.
| SB_EC_SECP112R1 | SECP112R1 | |
| SB_EC_SECP112R2 | SECP112R2 | |
| SB_EC_SECP128R1 | SECP128R1 | |
| SB_EC_SECP128R2 | SECP128R2 | |
| SB_EC_SECP160K1 | SECP160K1 | |
| SB_EC_SECP160R1 | SECP160R1 | |
| SB_EC_SECP160R2 | SECP160R2 | |
| SB_EC_SECP192K1 | SECP192K1 | |
| SB_EC_SECP192R1 | SECP192R1 | |
| SB_EC_SECP224K1 | SECP224K1 | |
| SB_EC_SECP224R1 | SECP224R1 | |
| SB_EC_SECP256K1 | SECP256K1 | |
| SB_EC_SECP256R1 | SECP256R1 | |
| SB_EC_SECP384R1 | SECP384R1 | |
| SB_EC_SECP521R1 | SECP521R1 | |
| SB_EC_SECT113R1 | SECT113R1 | |
| SB_EC_SECT113R2 | SECT113R2 | |
| SB_EC_SECT131R1 | SECT131R1 | |
| SB_EC_SECT131R2 | SECT131R2 | |
| SB_EC_SECT163K1 | SECT163K1 | |
| SB_EC_SECT163R1 | SECT163R1 | |
| SB_EC_SECT163R2 | SECT163R2 | |
| SB_EC_SECT193R1 | SECT193R1 | |
| SB_EC_SECT193R2 | SECT193R2 | |
| SB_EC_SECT233K1 | SECT233K1 | |
| SB_EC_SECT233R1 | SECT233R1 | |
| SB_EC_SECT239K1 | SECT239K1 | |
| SB_EC_SECT283K1 | SECT283K1 | |
| SB_EC_SECT283R1 | SECT283R1 | |
| SB_EC_SECT409K1 | SECT409K1 | |
| SB_EC_SECT409R1 | SECT409R1 | |
| SB_EC_SECT571K1 | SECT571K1 | |
| SB_EC_SECT571R1 | SECT571R1 | |
| SB_EC_PRIME192V1 | PRIME192V1 | |
| SB_EC_PRIME192V2 | PRIME192V2 | |
| SB_EC_PRIME192V3 | PRIME192V3 | |
| SB_EC_PRIME239V1 | PRIME239V1 | |
| SB_EC_PRIME239V2 | PRIME239V2 | |
| SB_EC_PRIME239V3 | PRIME239V3 | |
| SB_EC_PRIME256V1 | PRIME256V1 | |
| SB_EC_C2PNB163V1 | C2PNB163V1 | |
| SB_EC_C2PNB163V2 | C2PNB163V2 | |
| SB_EC_C2PNB163V3 | C2PNB163V3 | |
| SB_EC_C2PNB176W1 | C2PNB176W1 | |
| SB_EC_C2TNB191V1 | C2TNB191V1 | |
| SB_EC_C2TNB191V2 | C2TNB191V2 | |
| SB_EC_C2TNB191V3 | C2TNB191V3 | |
| SB_EC_C2ONB191V4 | C2ONB191V4 | |
| SB_EC_C2ONB191V5 | C2ONB191V5 | |
| SB_EC_C2PNB208W1 | C2PNB208W1 | |
| SB_EC_C2TNB239V1 | C2TNB239V1 | |
| SB_EC_C2TNB239V2 | C2TNB239V2 | |
| SB_EC_C2TNB239V3 | C2TNB239V3 | |
| SB_EC_C2ONB239V4 | C2ONB239V4 | |
| SB_EC_C2ONB239V5 | C2ONB239V5 | |
| SB_EC_C2PNB272W1 | C2PNB272W1 | |
| SB_EC_C2PNB304W1 | C2PNB304W1 | |
| SB_EC_C2TNB359V1 | C2TNB359V1 | |
| SB_EC_C2PNB368W1 | C2PNB368W1 | |
| SB_EC_C2TNB431R1 | C2TNB431R1 | |
| SB_EC_NISTP192 | NISTP192 | |
| SB_EC_NISTP224 | NISTP224 | |
| SB_EC_NISTP256 | NISTP256 | |
| SB_EC_NISTP384 | NISTP384 | |
| SB_EC_NISTP521 | NISTP521 | |
| SB_EC_NISTB163 | NISTB163 | |
| SB_EC_NISTB233 | NISTB233 | |
| SB_EC_NISTB283 | NISTB283 | |
| SB_EC_NISTB409 | NISTB409 | |
| SB_EC_NISTB571 | NISTB571 | |
| SB_EC_NISTK163 | NISTK163 | |
| SB_EC_NISTK233 | NISTK233 | |
| SB_EC_NISTK283 | NISTK283 | |
| SB_EC_NISTK409 | NISTK409 | |
| SB_EC_NISTK571 | NISTK571 | |
| SB_EC_GOSTCPTEST | GOSTCPTEST | |
| SB_EC_GOSTCPA | GOSTCPA | |
| SB_EC_GOSTCPB | GOSTCPB | |
| SB_EC_GOSTCPC | GOSTCPC | |
| SB_EC_GOSTCPXCHA | GOSTCPXCHA | |
| SB_EC_GOSTCPXCHB | GOSTCPXCHB | |
| SB_EC_BRAINPOOLP160R1 | BRAINPOOLP160R1 | |
| SB_EC_BRAINPOOLP160T1 | BRAINPOOLP160T1 | |
| SB_EC_BRAINPOOLP192R1 | BRAINPOOLP192R1 | |
| SB_EC_BRAINPOOLP192T1 | BRAINPOOLP192T1 | |
| SB_EC_BRAINPOOLP224R1 | BRAINPOOLP224R1 | |
| SB_EC_BRAINPOOLP224T1 | BRAINPOOLP224T1 | |
| SB_EC_BRAINPOOLP256R1 | BRAINPOOLP256R1 | |
| SB_EC_BRAINPOOLP256T1 | BRAINPOOLP256T1 | |
| SB_EC_BRAINPOOLP320R1 | BRAINPOOLP320R1 | |
| SB_EC_BRAINPOOLP320T1 | BRAINPOOLP320T1 | |
| SB_EC_BRAINPOOLP384R1 | BRAINPOOLP384R1 | |
| SB_EC_BRAINPOOLP384T1 | BRAINPOOLP384T1 | |
| SB_EC_BRAINPOOLP512R1 | BRAINPOOLP512R1 | |
| SB_EC_BRAINPOOLP512T1 | BRAINPOOLP512T1 | |
| SB_EC_CURVE25519 | CURVE25519 | |
| SB_EC_CURVE448 | CURVE448 |
Fingerprint
string (read-only)
Default: ""
Contains the fingerprint (a hash imprint) of this certificate.
While there is no formal standard defining what a fingerprint is, a SHA1 hash of the certificate's DER-encoded body is typically used.
FriendlyName
string (read-only)
Default: ""
Contains an associated alias (friendly name) of the certificate. The friendly name is not a property of a certificate: it is maintained by the certificate media rather than being included in its DER representation. Windows certificate stores are one example of media that does support friendly names.
HashAlgorithm
string
Default: ""
Provides means to set the hash algorithm to be used in the subsequent operation on the certificate (such as generation or key signing). It is not a property of a certificate; use SigAlgorithm to find out the hash algorithm that is part of the certificate signature.
| SB_HASH_ALGORITHM_SHA1 | SHA1 | |
| SB_HASH_ALGORITHM_SHA224 | SHA224 | |
| SB_HASH_ALGORITHM_SHA256 | SHA256 | |
| SB_HASH_ALGORITHM_SHA384 | SHA384 | |
| SB_HASH_ALGORITHM_SHA512 | SHA512 | |
| SB_HASH_ALGORITHM_MD2 | MD2 | |
| SB_HASH_ALGORITHM_MD4 | MD4 | |
| SB_HASH_ALGORITHM_MD5 | MD5 | |
| SB_HASH_ALGORITHM_RIPEMD160 | RIPEMD160 | |
| SB_HASH_ALGORITHM_CRC32 | CRC32 | |
| SB_HASH_ALGORITHM_SSL3 | SSL3 | |
| SB_HASH_ALGORITHM_GOST_R3411_1994 | GOST1994 | |
| SB_HASH_ALGORITHM_WHIRLPOOL | WHIRLPOOL | |
| SB_HASH_ALGORITHM_POLY1305 | POLY1305 | |
| SB_HASH_ALGORITHM_SHA3_224 | SHA3_224 | |
| SB_HASH_ALGORITHM_SHA3_256 | SHA3_256 | |
| SB_HASH_ALGORITHM_SHA3_384 | SHA3_384 | |
| SB_HASH_ALGORITHM_SHA3_512 | SHA3_512 | |
| SB_HASH_ALGORITHM_BLAKE2S_128 | BLAKE2S_128 | |
| SB_HASH_ALGORITHM_BLAKE2S_160 | BLAKE2S_160 | |
| SB_HASH_ALGORITHM_BLAKE2S_224 | BLAKE2S_224 | |
| SB_HASH_ALGORITHM_BLAKE2S_256 | BLAKE2S_256 | |
| SB_HASH_ALGORITHM_BLAKE2B_160 | BLAKE2B_160 | |
| SB_HASH_ALGORITHM_BLAKE2B_256 | BLAKE2B_256 | |
| SB_HASH_ALGORITHM_BLAKE2B_384 | BLAKE2B_384 | |
| SB_HASH_ALGORITHM_BLAKE2B_512 | BLAKE2B_512 | |
| SB_HASH_ALGORITHM_SHAKE_128 | SHAKE_128 | |
| SB_HASH_ALGORITHM_SHAKE_256 | SHAKE_256 | |
| SB_HASH_ALGORITHM_SHAKE_128_LEN | SHAKE_128_LEN | |
| SB_HASH_ALGORITHM_SHAKE_256_LEN | SHAKE_256_LEN |
Issuer
string (read-only)
Default: ""
The common name of the certificate issuer (CA), typically a company name. This is part of a larger set of credentials available via IssuerRDN.
IssuerRDN
string
Default: ""
A list of Property=Value pairs that uniquely identify the certificate issuer.
Example: /C=US/O=Nationwide CA/CN=Web Certification Authority
KeyAlgorithm
string
Default: "0"
Specifies the public key algorithm of this certificate.
| SB_CERT_ALGORITHM_ID_RSA_ENCRYPTION | rsaEncryption | |
| SB_CERT_ALGORITHM_MD2_RSA_ENCRYPTION | md2withRSAEncryption | |
| SB_CERT_ALGORITHM_MD5_RSA_ENCRYPTION | md5withRSAEncryption | |
| SB_CERT_ALGORITHM_SHA1_RSA_ENCRYPTION | sha1withRSAEncryption | |
| SB_CERT_ALGORITHM_ID_DSA | id-dsa | |
| SB_CERT_ALGORITHM_ID_DSA_SHA1 | id-dsa-with-sha1 | |
| SB_CERT_ALGORITHM_DH_PUBLIC | dhpublicnumber | |
| SB_CERT_ALGORITHM_SHA224_RSA_ENCRYPTION | sha224WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA256_RSA_ENCRYPTION | sha256WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA384_RSA_ENCRYPTION | sha384WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA512_RSA_ENCRYPTION | sha512WithRSAEncryption | |
| SB_CERT_ALGORITHM_ID_RSAPSS | id-RSASSA-PSS | |
| SB_CERT_ALGORITHM_ID_RSAOAEP | id-RSAES-OAEP | |
| SB_CERT_ALGORITHM_RSASIGNATURE_RIPEMD160 | ripemd160withRSA | |
| SB_CERT_ALGORITHM_ID_ELGAMAL | elGamal | |
| SB_CERT_ALGORITHM_SHA1_ECDSA | ecdsa-with-SHA1 | |
| SB_CERT_ALGORITHM_RECOMMENDED_ECDSA | ecdsa-recommended | |
| SB_CERT_ALGORITHM_SHA224_ECDSA | ecdsa-with-SHA224 | |
| SB_CERT_ALGORITHM_SHA256_ECDSA | ecdsa-with-SHA256 | |
| SB_CERT_ALGORITHM_SHA384_ECDSA | ecdsa-with-SHA384 | |
| SB_CERT_ALGORITHM_SHA512_ECDSA | ecdsa-with-SHA512 | |
| SB_CERT_ALGORITHM_EC | id-ecPublicKey | |
| SB_CERT_ALGORITHM_SPECIFIED_ECDSA | ecdsa-specified | |
| SB_CERT_ALGORITHM_GOST_R3410_1994 | id-GostR3410-94 | |
| SB_CERT_ALGORITHM_GOST_R3410_2001 | id-GostR3410-2001 | |
| SB_CERT_ALGORITHM_GOST_R3411_WITH_R3410_1994 | id-GostR3411-94-with-GostR3410-94 | |
| SB_CERT_ALGORITHM_GOST_R3411_WITH_R3410_2001 | id-GostR3411-94-with-GostR3410-2001 | |
| SB_CERT_ALGORITHM_SHA1_ECDSA_PLAIN | ecdsa-plain-SHA1 | |
| SB_CERT_ALGORITHM_SHA224_ECDSA_PLAIN | ecdsa-plain-SHA224 | |
| SB_CERT_ALGORITHM_SHA256_ECDSA_PLAIN | ecdsa-plain-SHA256 | |
| SB_CERT_ALGORITHM_SHA384_ECDSA_PLAIN | ecdsa-plain-SHA384 | |
| SB_CERT_ALGORITHM_SHA512_ECDSA_PLAIN | ecdsa-plain-SHA512 | |
| SB_CERT_ALGORITHM_RIPEMD160_ECDSA_PLAIN | ecdsa-plain-RIPEMD160 | |
| SB_CERT_ALGORITHM_WHIRLPOOL_RSA_ENCRYPTION | whirlpoolWithRSAEncryption | |
| SB_CERT_ALGORITHM_ID_DSA_SHA224 | id-dsa-with-sha224 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA256 | id-dsa-with-sha256 | |
| SB_CERT_ALGORITHM_SHA3_224_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-512 | |
| SB_CERT_ALGORITHM_SHA3_224_ECDSA | id-ecdsa-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_ECDSA | id-ecdsa-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_ECDSA | id-ecdsa-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_ECDSA | id-ecdsa-with-sha3-512 | |
| SB_CERT_ALGORITHM_SHA3_224_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-512 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA3_224 | id-dsa-with-sha3-224 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA3_256 | id-dsa-with-sha3-256 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b512 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_ECDSA | id-ecdsa-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_ECDSA | id-ecdsa-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_ECDSA | id-ecdsa-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_ECDSA | id-ecdsa-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_ECDSA | id-ecdsa-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_ECDSA | id-ecdsa-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_ECDSA | id-ecdsa-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_ECDSA | id-ecdsa-with-blake2b512 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b512 | |
| SB_CERT_ALGORITHM_ID_DSA_BLAKE2S_224 | id-dsa-with-blake2s224 | |
| SB_CERT_ALGORITHM_ID_DSA_BLAKE2S_256 | id-dsa-with-blake2s256 | |
| SB_CERT_ALGORITHM_EDDSA_ED25519 | id-Ed25519 | |
| SB_CERT_ALGORITHM_EDDSA_ED448 | id-Ed448 | |
| SB_CERT_ALGORITHM_EDDSA_ED25519_PH | id-Ed25519ph | |
| SB_CERT_ALGORITHM_EDDSA_ED448_PH | id-Ed448ph | |
| SB_CERT_ALGORITHM_EDDSA | id-EdDSA | |
| SB_CERT_ALGORITHM_EDDSA_SIGNATURE | id-EdDSA-sig | |
| SB_CERT_ALGORITHM_MLDSA_44 | id-ml-dsa-44 | |
| SB_CERT_ALGORITHM_MLDSA_65 | id-ml-dsa-65 | |
| SB_CERT_ALGORITHM_MLDSA_87 | id-ml-dsa-87 | |
| SB_CERT_ALGORITHM_HASH_MLDSA_44_SHA512 | id-hash-ml-dsa-44-with-sha512 | |
| SB_CERT_ALGORITHM_HASH_MLDSA_65_SHA512 | id-hash-ml-dsa-65-with-sha512 | |
| SB_CERT_ALGORITHM_HASH_MLDSA_87_SHA512 | id-hash-ml-dsa-87-with-sha512 |
Use the KeyBits, Curve, and PublicKeyBytes fields to get more details about the key the certificate contains.
KeyBits
int (read-only)
Default: 0
Returns the length of the public key in bits.
This value indicates the length of the principal cryptographic parameter of the key, such as the length of the RSA modulus or ECDSA field. The key data returned by the PublicKeyBytes or PrivateKeyBytes field would typically contain auxiliary values, and therefore be longer.
KeyFingerprint
string (read-only)
Default: ""
Returns a SHA1 fingerprint of the public key contained in the certificate.
Note that the key fingerprint is different from the certificate fingerprint accessible via the Fingerprint field. The key fingeprint uniquely identifies the public key, and so can be the same for multiple certificates containing the same key.
KeyUsage
int
Default: 0
Indicates the purposes of the key contained in the certificate, in the form of an OR'ed flag set.
This value is a bit mask of the following values:
| ckuUnknown | 0x00000 | Unknown key usage |
| ckuDigitalSignature | 0x00001 | Digital signature |
| ckuNonRepudiation | 0x00002 | Non-repudiation |
| ckuKeyEncipherment | 0x00004 | Key encipherment |
| ckuDataEncipherment | 0x00008 | Data encipherment |
| ckuKeyAgreement | 0x00010 | Key agreement |
| ckuKeyCertSign | 0x00020 | Certificate signing |
| ckuCRLSign | 0x00040 | Revocation signing |
| ckuEncipherOnly | 0x00080 | Encipher only |
| ckuDecipherOnly | 0x00100 | Decipher only |
| ckuServerAuthentication | 0x00200 | Server authentication |
| ckuClientAuthentication | 0x00400 | Client authentication |
| ckuCodeSigning | 0x00800 | Code signing |
| ckuEmailProtection | 0x01000 | Email protection |
| ckuTimeStamping | 0x02000 | Timestamping |
| ckuOCSPSigning | 0x04000 | OCSP signing |
| ckuSmartCardLogon | 0x08000 | Smartcard logon |
| ckuKeyPurposeClientAuth | 0x10000 | Kerberos - client authentication |
| ckuKeyPurposeKDC | 0x20000 | Kerberos - KDC |
Set this field before generating the certificate to propagate the key usage flags to the new certificate.
KeyValid
bool (read-only)
Default: False
Returns True if the certificate's key is cryptographically valid, and False otherwise.
OCSPLocations
string
Default: ""
Locations of OCSP services that can be used to check this certificate's validity in real time, as recorded by the CA.
Set this field before calling the certificate manager's Generate method to propagate it to the new certificate.
The OCSP locations are provided as a list of CRLF-separated URLs. Note that this differs from the behaviour used in earlier product versions, where the "|" character was used as the location separator.
OCSPNoCheck
bool
Default: False
Accessor to the value of the certificate's ocsp-no-check extension.
Origin
int (read-only)
Default: 0
Returns the location that the certificate was taken or loaded from.
PolicyIDs
string
Default: ""
Contains identifiers (OIDs) of the applicable certificate policies.
The Certificate Policies extension identifies a sequence of policies under which the certificate has been issued, and which regulate its usage.
Set this field when generating a certificate to propagate the policies information to the new certificate.
The policies are provided as a list of CRLF-separated entries. Note that this differs from the behaviour used in earlier product versions, where the "|" character was used as the policy element separator.
PrivateKeyBytes
byte[] (read-only)
Default: ""
Returns the certificate's private key in DER-encoded format. It is normal for this field to be empty if the private key is non-exportable, which, for example, is typical for certificates originating from hardware security devices.
PrivateKeyExists
bool (read-only)
Default: False
Indicates whether the certificate has a usable private key associated with it. If it is set to True, the certificate can be used for private key operations, such as signing or decryption.
This field is independent from PrivateKeyBytes, and can be set to True even if the former is empty. This would imply that the private key is non-exportable, but still can be used for cryptographic operations.
PrivateKeyExtractable
bool (read-only)
Default: False
Indicates whether the private key is extractable (exportable).
PublicKeyBytes
byte[] (read-only)
Default: ""
Contains the certificate's public key in DER format.
This typically would contain an ASN.1-encoded public key value. The exact format depends on the type of the public key contained in the certificate.
Qualified
bool (read-only)
Default: False
Indicates whether the certificate is qualified.
This property is set to True if the certificate is confirmed by a Trusted List to be qualified.
QualifiedStatements
QualifiedStatementsTypes
Default: 0
Returns a simplified qualified status of the certificate.
Qualifiers
string (read-only)
Default: ""
A list of qualifiers.
Contains a comma-separated list of qualifier aliases for the certificate, for example QCP-n-qscd,QCWithSSCD.
SelfSigned
bool (read-only)
Default: False
Indicates whether the certificate is self-signed (root) or signed by an external CA.
SerialNumber
byte[]
Default: ""
Returns the certificate's serial number.
The serial number is a binary string that uniquely identifies a certificate among others issued by the same CA. According to the X.509 standard, the (issuer, serial number) pair should be globally unique to facilitate chain building.
SigAlgorithm
string (read-only)
Default: ""
Indicates the algorithm that was used by the CA to sign this certificate.
A signature algorithm typically combines hash and public key algorithms together, such as sha256WithRSAEncryption or ecdsa-with-SHA256.
Source
PKISources (read-only)
Default: 0
Returns the source (location or disposition) of a cryptographic primitive entity, such as a certificate, CRL, or OCSP response.
Subject
string (read-only)
Default: ""
The common name of the certificate holder, typically an individual's name, a URL, an e-mail address, or a company name. This is part of a larger set of credentials available via SubjectRDN.
SubjectAlternativeName
string
Default: ""
Returns or sets the value of the Subject Alternative Name extension of the certificate.
Subject alternative names are used to provide additional names that are impractical to store in the main SubjectRDN field. For example, it is often used to store all the domain names that a TLS certificate is authorized to protect.
The alternative names are provided as a list of CRLF-separated entries. Note that this differs from the behaviour used in earlier product versions, where the "|" character was used as the element separator.
SubjectKeyID
byte[]
Default: ""
Contains a unique identifier of the certificate's cryptographic key.
Subject Key Identifier is a certificate extension which allows a specific public key to be associated with a certificate holder. Typically, subject key identifiers of CA certificates are recorded as respective CA key identifiers in the subordinate certificates that they issue, which facilitates chain building.
The SubjectKeyID and CAKeyID fields of self-signed certificates typically contain identical values, as in that specific case, the issuer and the subject are the same entity.
SubjectRDN
string
Default: ""
A list of Property=Value pairs that uniquely identify the certificate holder (subject).
Depending on the purpose of the certificate and the policies of the CA that issued it, the values included in the subject record may differ drastically and contain business or personal names, web URLs, email addresses, and other data.
Example: /C=US/O=Oranges and Apples, Inc./OU=Accounts Receivable/1.2.3.4.5=Value with unknown OID/CN=Margaret Watkins.
Valid
bool (read-only)
Default: False
Indicates whether or not the signature over the certificate or the request is valid and matches the public key contained in the CA certificate/request.
ValidFrom
string
Default: ""
The time point at which the certificate becomes valid, in UTC.
ValidTo
string
Default: ""
The time point at which the certificate expires, in UTC.
Constructors
public Certificate(byte[] bytes, int startIndex, int count, string password);
Public Certificate(ByVal Bytes As Byte(), ByVal StartIndex As Integer, ByVal Count As Integer, ByVal Password As String)
Loads the X.509 certificate from a memory buffer. Bytes is a buffer containing the raw certificate data. StartIndex and Count specify the starting position and number of bytes to be read from the buffer, respectively. Password is a password encrypting the certificate.
Loads the X.509 certificate from a memory buffer.
CertBytes is a buffer containing the raw certificate data. CertStartIndex and CertCount specify the starting position and number of bytes to be read from the buffer, respectively.
KeyBytes is a buffer containing the private key data. KeyStartIndex and KeyCount specify the starting position and number of bytes to be read from the buffer, respectively.
Password is a password encrypting the certificate.
public Certificate(byte[] bytes, int startIndex, int count);
Public Certificate(ByVal Bytes As Byte(), ByVal StartIndex As Integer, ByVal Count As Integer)
Loads the X.509 certificate from a memory buffer. Bytes is a buffer containing the raw certificate data. StartIndex and Count specify the starting position and number of bytes to be read from the buffer, respectively.
public Certificate(string path, string password);
Public Certificate(ByVal Path As String, ByVal Password As String)
Loads the X.509 certificate from a file. Path specifies the full path to the file containing the certificate data. Password is a password encrypting the certificate.
public Certificate(string certPath, string keyPath, string password);
Public Certificate(ByVal CertPath As String, ByVal KeyPath As String, ByVal Password As String)
Loads the X.509 certificate from a file. CertPath specifies the full path to the file containing the certificate data. KeyPath specifies the full path to the file containing the private key. Password is a password encrypting the certificate.
public Certificate(string path);
Public Certificate(ByVal Path As String)
Loads the X.509 certificate from a file. Path specifies the full path to the file containing the certificate data.
public Certificate(System.IO.Stream stream);
Public Certificate(ByVal Stream As System.IO.Stream)
Loads the X.509 certificate from a stream. Stream is a stream containing the certificate data.
public Certificate(System.IO.Stream stream, string password);
Public Certificate(ByVal Stream As System.IO.Stream, ByVal Password As String)
Loads the X.509 certificate from a stream. Stream is a stream containing the certificate data. Password is a password encrypting the certificate.
public Certificate(System.IO.Stream certStream, System.IO.Stream keyStream, string password);
Public Certificate(ByVal CertStream As System.IO.Stream, ByVal KeyStream As System.IO.Stream, ByVal Password As String)
Loads the X.509 certificate from a stream. CertStream is a stream containing the certificate data. KeyStream is a stream containing the private key. Password is a password encrypting the certificate.
public Certificate();
Public Certificate()
Creates a new object with default field values.
CryptoKey Type
This container represents a cryptographic key.
Remarks
This type is a universal placeholder for cryptographic keys.
Fields
Algorithm
string
Default: ""
The algorithm of the cryptographic key. A cryptokey object may hold either symmetric, MAC, or public key. Public key algorithms: RSA, ECDSA, Elgamal, DH, EdDSA, ML-DSA.
| SB_SYMMETRIC_ALGORITHM_RC4 | RC4 | |
| SB_SYMMETRIC_ALGORITHM_DES | DES | |
| SB_SYMMETRIC_ALGORITHM_3DES | 3DES | |
| SB_SYMMETRIC_ALGORITHM_RC2 | RC2 | |
| SB_SYMMETRIC_ALGORITHM_AES128 | AES128 | |
| SB_SYMMETRIC_ALGORITHM_AES192 | AES192 | |
| SB_SYMMETRIC_ALGORITHM_AES256 | AES256 | |
| SB_SYMMETRIC_ALGORITHM_IDENTITY | Identity | |
| SB_SYMMETRIC_ALGORITHM_BLOWFISH | Blowfish | |
| SB_SYMMETRIC_ALGORITHM_CAST128 | CAST128 | |
| SB_SYMMETRIC_ALGORITHM_IDEA | IDEA | |
| SB_SYMMETRIC_ALGORITHM_TWOFISH | Twofish | |
| SB_SYMMETRIC_ALGORITHM_TWOFISH128 | Twofish128 | |
| SB_SYMMETRIC_ALGORITHM_TWOFISH192 | Twofish192 | |
| SB_SYMMETRIC_ALGORITHM_TWOFISH256 | Twofish256 | |
| SB_SYMMETRIC_ALGORITHM_CAMELLIA | Camellia | |
| SB_SYMMETRIC_ALGORITHM_CAMELLIA128 | Camellia128 | |
| SB_SYMMETRIC_ALGORITHM_CAMELLIA192 | Camellia192 | |
| SB_SYMMETRIC_ALGORITHM_CAMELLIA256 | Camellia256 | |
| SB_SYMMETRIC_ALGORITHM_SERPENT | Serpent | |
| SB_SYMMETRIC_ALGORITHM_SERPENT128 | Serpent128 | |
| SB_SYMMETRIC_ALGORITHM_SERPENT192 | Serpent192 | |
| SB_SYMMETRIC_ALGORITHM_SERPENT256 | Serpent256 | |
| SB_SYMMETRIC_ALGORITHM_SEED | SEED | |
| SB_SYMMETRIC_ALGORITHM_RABBIT | Rabbit | |
| SB_SYMMETRIC_ALGORITHM_SYMMETRIC | Generic | |
| SB_SYMMETRIC_ALGORITHM_GOST_28147_1989 | GOST-28147-1989 | |
| SB_SYMMETRIC_ALGORITHM_CHACHA20 | ChaCha20 |
| SB_HASH_ALGORITHM_SHA1 | SHA1 | |
| SB_HASH_ALGORITHM_SHA224 | SHA224 | |
| SB_HASH_ALGORITHM_SHA256 | SHA256 | |
| SB_HASH_ALGORITHM_SHA384 | SHA384 | |
| SB_HASH_ALGORITHM_SHA512 | SHA512 | |
| SB_HASH_ALGORITHM_MD2 | MD2 | |
| SB_HASH_ALGORITHM_MD4 | MD4 | |
| SB_HASH_ALGORITHM_MD5 | MD5 | |
| SB_HASH_ALGORITHM_RIPEMD160 | RIPEMD160 | |
| SB_HASH_ALGORITHM_CRC32 | CRC32 | |
| SB_HASH_ALGORITHM_SSL3 | SSL3 | |
| SB_HASH_ALGORITHM_GOST_R3411_1994 | GOST1994 | |
| SB_HASH_ALGORITHM_WHIRLPOOL | WHIRLPOOL | |
| SB_HASH_ALGORITHM_POLY1305 | POLY1305 | |
| SB_HASH_ALGORITHM_SHA3_224 | SHA3_224 | |
| SB_HASH_ALGORITHM_SHA3_256 | SHA3_256 | |
| SB_HASH_ALGORITHM_SHA3_384 | SHA3_384 | |
| SB_HASH_ALGORITHM_SHA3_512 | SHA3_512 | |
| SB_HASH_ALGORITHM_BLAKE2S_128 | BLAKE2S_128 | |
| SB_HASH_ALGORITHM_BLAKE2S_160 | BLAKE2S_160 | |
| SB_HASH_ALGORITHM_BLAKE2S_224 | BLAKE2S_224 | |
| SB_HASH_ALGORITHM_BLAKE2S_256 | BLAKE2S_256 | |
| SB_HASH_ALGORITHM_BLAKE2B_160 | BLAKE2B_160 | |
| SB_HASH_ALGORITHM_BLAKE2B_256 | BLAKE2B_256 | |
| SB_HASH_ALGORITHM_BLAKE2B_384 | BLAKE2B_384 | |
| SB_HASH_ALGORITHM_BLAKE2B_512 | BLAKE2B_512 | |
| SB_HASH_ALGORITHM_SHAKE_128 | SHAKE_128 | |
| SB_HASH_ALGORITHM_SHAKE_256 | SHAKE_256 | |
| SB_HASH_ALGORITHM_SHAKE_128_LEN | SHAKE_128_LEN | |
| SB_HASH_ALGORITHM_SHAKE_256_LEN | SHAKE_256_LEN |
Bits
int (read-only)
Default: 0
The length of the key in bits.
Curve
string
Default: ""
This property specifies the name of the curve the EC key is built on.
Exportable
bool (read-only)
Default: False
Returns True if the key is exportable (can be serialized into an array of bytes), and False otherwise.
Fingerprint
string (read-only)
Default: ""
Contains the fingerprint (a hash imprint) of this key.
ID
byte[]
Default: ""
Provides access to a storage-specific key identifier. Key identifiers are used by cryptographic providers to refer to a particular key and/or distinguish between different keys. They are typically unique within a storage, but there is no guarantee that a particular cryptoprovider will conform to that (or will assign any key IDs at all).
IV
byte[]
Default: ""
The initialization vector (IV) of a symmetric key. This is normally a public part of a symmetric key, the idea of which is to introduce randomness to the encrypted data and/or serve as a first block in chaining ciphers.
Key
byte[] (read-only)
Default: ""
The byte array representation of the key. This may not be available for non-Exportable keys.
Nonce
byte[]
Default: ""
A nonce value associated with a key. It is similar to IV, but its only purpose is to introduce randomness.
Private
bool (read-only)
Default: False
Returns True if the object hosts a private key, and False otherwise.
Public
bool (read-only)
Default: False
Returns True if the object hosts a public key, and False otherwise.
Subject
byte[]
Default: ""
Returns the key subject. This is a cryptoprovider-dependent value, which normally aims to provide some user-friendly insight into the key owner.
Symmetric
bool (read-only)
Default: False
Returns True if the object contains a symmetric key, and False otherwise.
Valid
bool (read-only)
Default: False
Returns True if this key is valid. The term Valid highly depends on the kind of the key being stored. A symmetric key is considered valid if its length fits the algorithm being set. The validity of an RSA key also ensures that the RSA key elements (primes, exponents, and modulus) are consistent.
Constructors
Creates an empty crypto key object.
ExternalCrypto Type
Specifies the parameters of external cryptographic calls.
Remarks
External cryptocalls are used in a Distributed Cryptography (DC) subsystem, which allows the delegation of security operations to the remote agent. For instance, it can be used to compute the signature value on the server, while retaining the client's private key locally.
- AsyncDocumentID
- CustomParams
- Data
- ExternalHashCalculation
- HashAlgorithm
- KeyID
- KeySecret
- Method
- Mode
- PublicKeyAlgorithm
Fields
AsyncDocumentID
string
Default: ""
Specifies an optional document ID for SignAsyncBegin() and SignAsyncEnd() calls.
Use this property when working with multi-signature DCAuth requests and responses to uniquely identify documents signed within a larger batch. On the completion stage, this value helps the signing component identify the correct signature in the returned batch of responses.
If using batched requests, make sure to set this property to the same value on both the pre-signing (SignAsyncBegin) and completion (SignAsyncEnd) stages.
CustomParams
string
Default: ""
Custom parameters to be passed to the signing service (uninterpreted).
Data
string
Default: ""
Additional data to be included in the async state and mirrored back by the requestor.
ExternalHashCalculation
bool
Default: False
Specifies whether the message hash is to be calculated at the external endpoint. Please note that this mode is not supported by the DCAuth component.
If set to true, the component will pass a few kilobytes of to-be-signed data from the document to the OnExternalSign event. This only applies when SignExternal() is called.
HashAlgorithm
string
Default: "SHA256"
Specifies the request's signature hash algorithm.
| SB_HASH_ALGORITHM_SHA1 | SHA1 | |
| SB_HASH_ALGORITHM_SHA224 | SHA224 | |
| SB_HASH_ALGORITHM_SHA256 | SHA256 | |
| SB_HASH_ALGORITHM_SHA384 | SHA384 | |
| SB_HASH_ALGORITHM_SHA512 | SHA512 | |
| SB_HASH_ALGORITHM_MD2 | MD2 | |
| SB_HASH_ALGORITHM_MD4 | MD4 | |
| SB_HASH_ALGORITHM_MD5 | MD5 | |
| SB_HASH_ALGORITHM_RIPEMD160 | RIPEMD160 | |
| SB_HASH_ALGORITHM_CRC32 | CRC32 | |
| SB_HASH_ALGORITHM_SSL3 | SSL3 | |
| SB_HASH_ALGORITHM_GOST_R3411_1994 | GOST1994 | |
| SB_HASH_ALGORITHM_WHIRLPOOL | WHIRLPOOL | |
| SB_HASH_ALGORITHM_POLY1305 | POLY1305 | |
| SB_HASH_ALGORITHM_SHA3_224 | SHA3_224 | |
| SB_HASH_ALGORITHM_SHA3_256 | SHA3_256 | |
| SB_HASH_ALGORITHM_SHA3_384 | SHA3_384 | |
| SB_HASH_ALGORITHM_SHA3_512 | SHA3_512 | |
| SB_HASH_ALGORITHM_BLAKE2S_128 | BLAKE2S_128 | |
| SB_HASH_ALGORITHM_BLAKE2S_160 | BLAKE2S_160 | |
| SB_HASH_ALGORITHM_BLAKE2S_224 | BLAKE2S_224 | |
| SB_HASH_ALGORITHM_BLAKE2S_256 | BLAKE2S_256 | |
| SB_HASH_ALGORITHM_BLAKE2B_160 | BLAKE2B_160 | |
| SB_HASH_ALGORITHM_BLAKE2B_256 | BLAKE2B_256 | |
| SB_HASH_ALGORITHM_BLAKE2B_384 | BLAKE2B_384 | |
| SB_HASH_ALGORITHM_BLAKE2B_512 | BLAKE2B_512 | |
| SB_HASH_ALGORITHM_SHAKE_128 | SHAKE_128 | |
| SB_HASH_ALGORITHM_SHAKE_256 | SHAKE_256 | |
| SB_HASH_ALGORITHM_SHAKE_128_LEN | SHAKE_128_LEN | |
| SB_HASH_ALGORITHM_SHAKE_256_LEN | SHAKE_256_LEN |
KeyID
string
Default: ""
The ID of the pre-shared key used for DC request authentication.
Asynchronous DCAuth-driven communication requires that parties authenticate each other with a secret pre-shared cryptographic key. This provides an extra protection layer for the protocol and diminishes the risk of the private key becoming abused by foreign parties. Use this property to provide the pre-shared key identifier, and use KeySecret to pass the key itself.
The same KeyID/KeySecret pair should be used on the DCAuth side for the signing requests to be accepted.
Note: The KeyID/KeySecret scheme is very similar to the AuthKey scheme used in various Cloud service providers to authenticate users.
Example:
signer.ExternalCrypto.KeyID = "MainSigningKey";
signer.ExternalCrypto.KeySecret = "abcdef0123456789";
KeySecret
string
Default: ""
The pre-shared key used for DC request authentication. This key must be set and match the key used by the DCAuth counterpart for the scheme to work.
Read more about configuring authentication in the KeyID topic.
Method
AsyncSignMethods
Default: 0
Specifies the asynchronous signing method. This is typically defined by the DC server capabilities and setup.
Available options:
| asmdPKCS1 | 0 |
| asmdPKCS7 | 1 |
Mode
ExternalCryptoModes
Default: 0
Specifies the external cryptography mode.
Available options:
| ecmDefault | The default value (0) |
| ecmDisabled | Do not use DC or external signing (1) |
| ecmGeneric | Generic external signing with the OnExternalSign event (2) |
| ecmDCAuth | DCAuth signing (3) |
| ecmDCAuthJSON | DCAuth signing in JSON format (4) |
PublicKeyAlgorithm
string
Default: ""
Provide the public key algorithm here if the certificate is not available on the pre-signing stage.
| SB_CERT_ALGORITHM_ID_RSA_ENCRYPTION | rsaEncryption | |
| SB_CERT_ALGORITHM_MD2_RSA_ENCRYPTION | md2withRSAEncryption | |
| SB_CERT_ALGORITHM_MD5_RSA_ENCRYPTION | md5withRSAEncryption | |
| SB_CERT_ALGORITHM_SHA1_RSA_ENCRYPTION | sha1withRSAEncryption | |
| SB_CERT_ALGORITHM_ID_DSA | id-dsa | |
| SB_CERT_ALGORITHM_ID_DSA_SHA1 | id-dsa-with-sha1 | |
| SB_CERT_ALGORITHM_DH_PUBLIC | dhpublicnumber | |
| SB_CERT_ALGORITHM_SHA224_RSA_ENCRYPTION | sha224WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA256_RSA_ENCRYPTION | sha256WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA384_RSA_ENCRYPTION | sha384WithRSAEncryption | |
| SB_CERT_ALGORITHM_SHA512_RSA_ENCRYPTION | sha512WithRSAEncryption | |
| SB_CERT_ALGORITHM_ID_RSAPSS | id-RSASSA-PSS | |
| SB_CERT_ALGORITHM_ID_RSAOAEP | id-RSAES-OAEP | |
| SB_CERT_ALGORITHM_RSASIGNATURE_RIPEMD160 | ripemd160withRSA | |
| SB_CERT_ALGORITHM_ID_ELGAMAL | elGamal | |
| SB_CERT_ALGORITHM_SHA1_ECDSA | ecdsa-with-SHA1 | |
| SB_CERT_ALGORITHM_RECOMMENDED_ECDSA | ecdsa-recommended | |
| SB_CERT_ALGORITHM_SHA224_ECDSA | ecdsa-with-SHA224 | |
| SB_CERT_ALGORITHM_SHA256_ECDSA | ecdsa-with-SHA256 | |
| SB_CERT_ALGORITHM_SHA384_ECDSA | ecdsa-with-SHA384 | |
| SB_CERT_ALGORITHM_SHA512_ECDSA | ecdsa-with-SHA512 | |
| SB_CERT_ALGORITHM_EC | id-ecPublicKey | |
| SB_CERT_ALGORITHM_SPECIFIED_ECDSA | ecdsa-specified | |
| SB_CERT_ALGORITHM_GOST_R3410_1994 | id-GostR3410-94 | |
| SB_CERT_ALGORITHM_GOST_R3410_2001 | id-GostR3410-2001 | |
| SB_CERT_ALGORITHM_GOST_R3411_WITH_R3410_1994 | id-GostR3411-94-with-GostR3410-94 | |
| SB_CERT_ALGORITHM_GOST_R3411_WITH_R3410_2001 | id-GostR3411-94-with-GostR3410-2001 | |
| SB_CERT_ALGORITHM_SHA1_ECDSA_PLAIN | ecdsa-plain-SHA1 | |
| SB_CERT_ALGORITHM_SHA224_ECDSA_PLAIN | ecdsa-plain-SHA224 | |
| SB_CERT_ALGORITHM_SHA256_ECDSA_PLAIN | ecdsa-plain-SHA256 | |
| SB_CERT_ALGORITHM_SHA384_ECDSA_PLAIN | ecdsa-plain-SHA384 | |
| SB_CERT_ALGORITHM_SHA512_ECDSA_PLAIN | ecdsa-plain-SHA512 | |
| SB_CERT_ALGORITHM_RIPEMD160_ECDSA_PLAIN | ecdsa-plain-RIPEMD160 | |
| SB_CERT_ALGORITHM_WHIRLPOOL_RSA_ENCRYPTION | whirlpoolWithRSAEncryption | |
| SB_CERT_ALGORITHM_ID_DSA_SHA224 | id-dsa-with-sha224 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA256 | id-dsa-with-sha256 | |
| SB_CERT_ALGORITHM_SHA3_224_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-sha3-512 | |
| SB_CERT_ALGORITHM_SHA3_224_ECDSA | id-ecdsa-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_ECDSA | id-ecdsa-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_ECDSA | id-ecdsa-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_ECDSA | id-ecdsa-with-sha3-512 | |
| SB_CERT_ALGORITHM_SHA3_224_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-224 | |
| SB_CERT_ALGORITHM_SHA3_256_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-256 | |
| SB_CERT_ALGORITHM_SHA3_384_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-384 | |
| SB_CERT_ALGORITHM_SHA3_512_ECDSA_PLAIN | id-ecdsa-plain-with-sha3-512 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA3_224 | id-dsa-with-sha3-224 | |
| SB_CERT_ALGORITHM_ID_DSA_SHA3_256 | id-dsa-with-sha3-256 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_RSA_ENCRYPTION | id-rsassa-pkcs1-v1_5-with-blake2b512 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_ECDSA | id-ecdsa-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_ECDSA | id-ecdsa-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_ECDSA | id-ecdsa-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_ECDSA | id-ecdsa-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_ECDSA | id-ecdsa-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_ECDSA | id-ecdsa-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_ECDSA | id-ecdsa-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_ECDSA | id-ecdsa-with-blake2b512 | |
| SB_CERT_ALGORITHM_BLAKE2S_128_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s128 | |
| SB_CERT_ALGORITHM_BLAKE2S_160_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s160 | |
| SB_CERT_ALGORITHM_BLAKE2S_224_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s224 | |
| SB_CERT_ALGORITHM_BLAKE2S_256_ECDSA_PLAIN | id-ecdsa-plain-with-blake2s256 | |
| SB_CERT_ALGORITHM_BLAKE2B_160_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b160 | |
| SB_CERT_ALGORITHM_BLAKE2B_256_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b256 | |
| SB_CERT_ALGORITHM_BLAKE2B_384_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b384 | |
| SB_CERT_ALGORITHM_BLAKE2B_512_ECDSA_PLAIN | id-ecdsa-plain-with-blake2b512 | |
| SB_CERT_ALGORITHM_ID_DSA_BLAKE2S_224 | id-dsa-with-blake2s224 | |
| SB_CERT_ALGORITHM_ID_DSA_BLAKE2S_256 | id-dsa-with-blake2s256 | |
| SB_CERT_ALGORITHM_EDDSA_ED25519 | id-Ed25519 | |
| SB_CERT_ALGORITHM_EDDSA_ED448 | id-Ed448 | |
| SB_CERT_ALGORITHM_EDDSA_ED25519_PH | id-Ed25519ph | |
| SB_CERT_ALGORITHM_EDDSA_ED448_PH | id-Ed448ph | |
| SB_CERT_ALGORITHM_EDDSA | id-EdDSA | |
| SB_CERT_ALGORITHM_EDDSA_SIGNATURE | id-EdDSA-sig | |
| SB_CERT_ALGORITHM_MLDSA_44 | id-ml-dsa-44 | |
| SB_CERT_ALGORITHM_MLDSA_65 | id-ml-dsa-65 | |
| SB_CERT_ALGORITHM_MLDSA_87 | id-ml-dsa-87 | |
| SB_CERT_ALGORITHM_HASH_MLDSA_44_SHA512 | id-hash-ml-dsa-44-with-sha512 | |
| SB_CERT_ALGORITHM_HASH_MLDSA_65_SHA512 | id-hash-ml-dsa-65-with-sha512 | |
| SB_CERT_ALGORITHM_HASH_MLDSA_87_SHA512 | id-hash-ml-dsa-87-with-sha512 |
Constructors
public ExternalCrypto();
Public ExternalCrypto()
Creates a new ExternalCrypto object with default field values.
SAMLEntity Type
Represents SAML entity details.
Remarks
This type is a container for SAML SP or IdP entity parameters. These are often referred to as service metadata.
- ContactPerson
- EncryptionKey
- EncryptionMethods
- EntityID
- Flags
- IdPSSOLink
- NameIDFormats
- OrganizationDisplayName
- OrganizationLang
- OrganizationName
- OrganizationURL
- SignatureValidationResult
- Signed
- SignedWith
- SigningKey
- ValidUntil
Fields
ContactPerson
string
Default: ""
The contact person or persons for the entity.
SAML assumes that more than one contact person can be specified. Each line of this potentially multi-line property contains one such record.
Each record contains a semicolon-separated list of contact person parameters, for example:
Company=My Company;EmailAddress=info@company.com;TelephoneNumber=+012345678;Type=other Company=My Company;EmailAddress=info@company.com;TelephoneNumber=+012345678;Type=technical;Extension.https://spid.gov.it/saml-extensions.VATNumber=IT122345678
You can use LoadNameValuePairs and SaveNameValuePairs methods of the Utils class to process content of this property.
EncryptionKey
string
Default: ""
Contains the entity's encryption key.
This setting returns the entity's public encryption key. In most cases this is in the form of a DER-encoded X.509 certificate. This property cannot be set in code; it is either taken from the processed metadata file (for other-party settings), or derived from the locally set EncryptionCertificate setting (for this-party settings).
Requests sent to the endpoint can be encrypted with the provided key or certificate.
EncryptionMethods
string
Default: ""
Specifies the list of encryption methods supported by the entity.
This setting contains a list of encryption methods, in form of XML-ENC URLs separated with newline characters, supported by the entity. These can be considered when encrypting messages destined for this entity.
Examples of algorithms supported by this property:
- http://www.w3.org/2009/xmlenc11#aes128-gcm
- http://www.w3.org/2001/04/xmlenc#aes256-cbc
EntityID
string
Default: ""
Represents the SAML entity ID.
Use this property to read or set the unique SAML entity ID. This is often the URI of the web endpoint (such as https://sp.myserver.com).
Flags
int
Default: 0
Adjusts secondary entity properties.
Use this bit mask property to adjust certain secondary settings. The following flags are supported:
- 1 - sefRequireSignedRequests - the provider expects the consumers to sign requests they send in.
IdPSSOLink
string
Default: ""
Contains a local server page link that triggers SAML authentication to the SP.
This property specifies the web link that initiates the transfer of SAML authentication fact to the SP.
One scenario where this property can be used is triggering the assertion dispatch in IdP-initiated SSO flows. Navigating to the link will make the IdP server generate the authentication assertion (if the user had been authenticated) and forward this assertion to the respective service provider.
NameIDFormats
string
Default: ""
The list of NameID formats supported by this entity.
Use this setting to get or set the list of NameID formats supported by the entity.
Use SAML notation for the formats:
- urn:oasis:names:tc:SAML:2.0:nameid-format:transient
- urn:oasis:names:tc:SAML:2.0:nameid-format:persistent
- urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress
OrganizationDisplayName
string
Default: ""
The friendly name of the organization that maintains the entity.
Use this setting to get or set the user-friendly name of the organization that maintains the SAML entity.
OrganizationLang
string
Default: ""
The language preferred by the organization.
This optional setting can be used to adjust the preferred language of the owning organization.
OrganizationName
string
Default: ""
The name of the organization that maintains the entity.
Use this setting to get or set the name of the organization that maintains the SAML entity.
OrganizationURL
string
Default: ""
The web URL of the organization that maintains the entity.
Use this setting to get or set the web address of the organization responsible for this SAML entity.
SignatureValidationResult
SignatureValidities (read-only)
Default: 0
The outcome of the cryptographic signature validation.
The following signature validity values are supported:
| svtValid | 0 | The signature is valid |
| svtUnknown | 1 | Signature validity is unknown |
| svtCorrupted | 2 | The signature is corrupted |
| svtSignerNotFound | 3 | Failed to acquire the signing certificate. The signature cannot be validated. |
| svtFailure | 4 | General failure |
| svtReferenceCorrupted | 5 | Reference corrupted (XML-based signatures only) |
Signed
bool (read-only)
Default: False
Specifies whether the SAML entity information is or should be signed.
Check this property to find out whether the metadata was signed by the sender, or set this property to true to indicate that the created metadata should be signed.
SignedWith
string (read-only)
Default: ""
Contains the certificate or key that was used to sign the settings (metadata) document.
This setting returns the public part of the metadata signing key. In most cases this is in the form of a DER-encoded X.509 certificate.
The value of this property is retrieved from the metadata file when it is loaded with the ImportSettings call. If the metadata is signed, you can check the integrity of the signature using the SignatureValidationResult setting.
SigningKey
string
Default: ""
Contains the entity's signing key.
This setting returns the public part of the entity's signing key. In most cases this is in the form of a PKCS#1 RSA or ECDSA key.
The signing key is used to sign message conveyed over Redirect binding. Redirect signatures are simpler than SAML message signatures and are made with raw keys rather than certificates.
ValidUntil
string
Default: ""
Specifies the expiration time of the SAML entity information.
This setting only makes sense when the information was loaded or is going to be saved to a metadata XML.
Constructors
public SAMLEntity();
Public SAMLEntity()
Creates a new SAMLEntity object.
SAMLSecuritySettings Type
Represents SAML security settings for the message being viewed/edited.
Remarks
This type is a container for SAML security parameters.
Fields
CanonicalizationMethod
string
Default: ""
The canonicalization method to use in the signature.
The URI of the canonicalization method to use in the signature (e.g. http://www.w3.org/TR/xml-exc-c14n/)
DigestMethod
string
Default: ""
The digest method to use.
The URI of the digest method to use for signing, as defined in XMLDSIG or XMLENC: http://www.w3.org/2000/09/xmldsig#sha256.
EncryptionMethod
string
Default: "AES256"
The encryption method used to encrypt the assertion.
This property contains the encryption algorithm used to encrypt the XML assertion.
Supported values:
| SB_XML_ENCRYPTION_ALGORITHM_RC4 | RC4 | |
| SB_XML_ENCRYPTION_ALGORITHM_DES | DES | |
| SB_XML_ENCRYPTION_ALGORITHM_3DES | 3DEST | |
| SB_XML_ENCRYPTION_ALGORITHM_AES128 | AES128 | |
| SB_XML_ENCRYPTION_ALGORITHM_AES192 | AES192 | |
| SB_XML_ENCRYPTION_ALGORITHM_AES256 | AES256 | |
| SB_XML_ENCRYPTION_ALGORITHM_CAMELLIA128 | Camellia128 | |
| SB_XML_ENCRYPTION_ALGORITHM_CAMELLIA192 | Camellia192 | |
| SB_XML_ENCRYPTION_ALGORITHM_CAMELLIA256 | Camellia256 | |
| SB_XML_ENCRYPTION_ALGORITHM_SEED | SEED |
Flags
int
Default: 1
Provides access to secondary security parameters and tweaks.
This property is a bitwise combination of zero or more flags. The following flags are currently supported: The following flags can be used with any SAML component (although they may not apply in all modes of use):
| ssfSignatureAfterIssuer | 1 | Place the Signature tag after the issuer tag in the XML document |
| ssfSignatureBeforeDescriptor | 2 | Place the Signature tag before the entity descriptor tag in the XML metadata |
| ssfKeyDataIssuerSerial | 4 | Include the IssuerSerial key data element |
| ssfKeyDataSKI | 8 | Include the SubjectKeyIdentifier key data element |
| ssfKeyDataSubjectName | 16 | Include the SubjectName key data element |
| ssfKeyDataCertificate | 32 | Include the Certificate key data element |
| ssfKeyDataCRL | 64 | Include the CRL key data element |
| ssfSignAuthnRequests | 65536 | Sign authentication requests (SP only) |
| ssfSignArtifactResolveRequests | 131072 | Sign artifact resolve requests |
| ssfSignLogoutRequests | 262144 | Sign logout requests |
| ssfSignAssertions | 524288 | Sign outgoing assertions (IdP only) |
| ssfSignResponses | 1048576 | Sign all responses (IdP only) |
| ssfEncryptAssertions | 2097152 | Encrypt generated assertions (IdP only) |
SigMethod
string
Default: ""
The signature method to use.
The URI specifying the signature method to use for signing, for example http://www.w3.org/2001/04/xmldsig-more#rsa-sha256.
SignaturePolicy
SAMLSignaturePolicies
Default: 0
Specifies the signature validation policy.
Use this property to specify the signature validation policy for the component.
Constructors
public SAMLSecuritySettings();
Public SAMLSecuritySettings()
Creates a new SAMLSecuritySettings object.
SAMLServiceInfo Type
Represents SAML service details.
Remarks
This type is a container for SAML SP or IdP endpoint service parameters.
Fields
BindingType
SAMLBindingTypes (read-only)
Default: 0
Specifies the type of SAML binding that this endpoint accepts.
Use this property to specify the binding type to use with this endpoint.
EntityID
string (read-only)
Default: ""
Represents the SAML entity ID.
Use this property to read or set the unique SAML entity ID. This is often the URI of the web endpoint (such as https://sp.myserver.com).
Location
string (read-only)
Default: ""
The location (URL) of the endpoint.
Priority
int
Default: -1
The priority of the endpoint in relation to other endpoints with the same Location.
Indicates the relative priority of the endpoint. Use this setting to adjust priority of certain binding types before others. When composing the metadata XML, the endpoint with the highest priority gets described with a Default attribute.
Leave all priorities at -1 to omit generation of the Default attribute.
Service
int (read-only)
Default: 0
The kind of the service being provided at this endpoint.
The Service setting returns the kind of the service that is being provided at this endpoint. Typical SP services are AssertionConsumerService and ArtifactResolutionService. Typical IdP services are SingleSignOnService, SingleLogoutService, and ArtifactResolutionService.
ServiceIndex
int (read-only)
Default: 0
The index of this endpoint.
For endpoints that can accept requests via multiple bindings, Index is used to distinguish between individual endpoint specifiers.
Constructors
public SAMLServiceInfo();
Public SAMLServiceInfo()
Creates a new SAMLServiceInfo object.
SocketSettings Type
A container for the socket settings.
Remarks
This type is a container for socket-layer parameters.
- DNSMode
- DNSPort
- DNSQueryTimeout
- DNSServers
- DNSTotalTimeout
- IncomingSpeedLimit
- LocalAddress
- LocalPort
- OutgoingSpeedLimit
- Timeout
- UseIPv6
Fields
DNSMode
DNSResolveModes
Default: 0
Selects the DNS resolver to use: the component's (secure) built-in one, or the one provided by the system.
| dmAuto | 0 |
| dmPlatform | 1 |
| dmOwn | 2 |
| dmOwnSecure | 3 |
DNSPort
int
Default: 0
Specifies the port number to be used for sending queries to the DNS server.
DNSQueryTimeout
int
Default: 0
The timeout (in milliseconds) for each DNS query. The value of 0 indicates an infinite timeout.
DNSServers
string
Default: ""
The addresses of DNS servers to use for address resolution, separated by commas or semicolons.
DNSTotalTimeout
int
Default: 0
The timeout (in milliseconds) for the whole resolution process. The value of 0 indicates an infinite timeout.
IncomingSpeedLimit
int
Default: 0
The maximum number of bytes to read from the socket, per second.
LocalAddress
string
Default: ""
The local network interface to bind the socket to.
LocalPort
int
Default: 0
The local port number to bind the socket to.
OutgoingSpeedLimit
int
Default: 0
The maximum number of bytes to write to the socket, per second.
Timeout
int
Default: 60000
The maximum period of waiting, in milliseconds, after which the socket operation is considered unsuccessful.
If Timeout is set to 0, a socket operation will expire after the system-default timeout (2 hrs 8 min for TCP stack).
UseIPv6
bool
Default: False
Enables or disables IP protocol version 6.
Constructors
public SocketSettings();
Public SocketSettings()
Creates a new SocketSettings object.
TLSConnectionInfo Type
Contains information about a network connection.
Remarks
Use this property to check various details of the network connection. These include the total amounts of data transferred, the availability of TLS, and its parameters.
- AEADCipher
- ChainValidationDetails
- ChainValidationResult
- Ciphersuite
- ClientAuthenticated
- ClientAuthRequested
- ConnectionEstablished
- ConnectionID
- DigestAlgorithm
- EncryptionAlgorithm
- Exportable
- ID
- KeyExchangeAlgorithm
- KeyExchangeKeyBits
- NamedECCurve
- PFSCipher
- PreSharedIdentity
- PreSharedIdentityHint
- PublicKeyBits
- RemoteAddress
- RemotePort
- ResumedSession
- SecureConnection
- ServerAuthenticated
- SignatureAlgorithm
- SymmetricBlockSize
- SymmetricKeyBits
- TotalBytesReceived
- TotalBytesSent
- ValidationLog
- Version
Fields
AEADCipher
bool (read-only)
Default: False
Indicates whether the encryption algorithm used is an AEAD cipher.
ChainValidationDetails
int (read-only)
Default: 0
The details of a certificate chain validation outcome. They may often suggest the reasons that contributed to the overall validation result.
Returns a bit mask of the following options:
| cvrBadData | 0x0001 | One or more certificates in the validation path are malformed |
| cvrRevoked | 0x0002 | One or more certificates are revoked |
| cvrNotYetValid | 0x0004 | One or more certificates are not yet valid |
| cvrExpired | 0x0008 | One or more certificates are expired |
| cvrInvalidSignature | 0x0010 | A certificate contains a non-valid digital signature |
| cvrUnknownCA | 0x0020 | A CA certificate for one or more certificates has not been found (chain incomplete) |
| cvrCAUnauthorized | 0x0040 | One of the CA certificates are not authorized to act as CA |
| cvrCRLNotVerified | 0x0080 | One or more CRLs could not be verified |
| cvrOCSPNotVerified | 0x0100 | One or more OCSP responses could not be verified |
| cvrIdentityMismatch | 0x0200 | The identity protected by the certificate (a TLS endpoint or an e-mail addressee) does not match what is recorded in the certificate |
| cvrNoKeyUsage | 0x0400 | A mandatory key usage is not enabled in one of the chain certificates |
| cvrBlocked | 0x0800 | One or more certificates are blocked |
| cvrFailure | 0x1000 | General validation failure |
| cvrChainLoop | 0x2000 | Chain loop: one of the CA certificates recursively signs itself |
| cvrWeakAlgorithm | 0x4000 | A weak algorithm is used in one of certificates or revocation elements |
| cvrUserEnforced | 0x8000 | The chain was considered invalid following intervention from a user code |
ChainValidationResult
ChainValidities (read-only)
Default: 0
The outcome of a certificate chain validation routine.
Available options:
| cvtValid | 0 | The chain is valid |
| cvtValidButUntrusted | 1 | The chain is valid, but the root certificate is not trusted |
| cvtInvalid | 2 | The chain is not valid (some of certificates are revoked, expired, or contain an invalid signature) |
| cvtCantBeEstablished | 3 | The validity of the chain cannot be established because of missing or unavailable validation information (certificates, CRLs, or OCSP responses) |
Use the ValidationLog property to access the detailed validation log.
Ciphersuite
string (read-only)
Default: ""
The cipher suite employed by this connection.
For TLS connections, this property returns the ciphersuite that was/is employed by the connection.
ClientAuthenticated
bool (read-only)
Default: False
Specifies whether client authentication was performed during this connection.
ClientAuthRequested
bool (read-only)
Default: False
Specifies whether client authentication was requested during this connection.
ConnectionEstablished
bool (read-only)
Default: False
Indicates whether the connection has been established fully.
ConnectionID
byte[] (read-only)
Default: ""
The unique identifier assigned to this connection.
DigestAlgorithm
string (read-only)
Default: ""
The digest algorithm used in a TLS-enabled connection.
EncryptionAlgorithm
string (read-only)
Default: ""
The symmetric encryption algorithm used in a TLS-enabled connection.
Exportable
bool (read-only)
Default: False
Indicates whether a TLS connection uses a reduced-strength exportable cipher.
ID
long (read-only)
Default: -1
The client connection's unique identifier. This value is used throughout to refer to a particular client connection.
KeyExchangeAlgorithm
string (read-only)
Default: ""
The key exchange algorithm used in a TLS-enabled connection.
KeyExchangeKeyBits
int (read-only)
Default: 0
The length of the key exchange key of a TLS-enabled connection.
NamedECCurve
string (read-only)
Default: ""
The elliptic curve used in this connection.
PFSCipher
bool (read-only)
Default: False
Indicates whether the chosen ciphersuite provides perfect forward secrecy (PFS).
PreSharedIdentity
string
Default: ""
Specifies the identity used when the PSK (Pre-Shared Key) key-exchange mechanism is negotiated.
PreSharedIdentityHint
string (read-only)
Default: ""
A hint professed by the server to help the client select the PSK identity to use.
PublicKeyBits
int (read-only)
Default: 0
The length of the public key.
RemoteAddress
string (read-only)
Default: ""
The client's IP address.
RemotePort
int (read-only)
Default: 0
The remote port of the client connection.
ResumedSession
bool (read-only)
Default: False
Indicates whether a TLS-enabled connection was spawned from another TLS connection
SecureConnection
bool (read-only)
Default: False
Indicates whether TLS or SSL is enabled for this connection.
ServerAuthenticated
bool (read-only)
Default: False
Indicates whether server authentication was performed during a TLS-enabled connection.
SignatureAlgorithm
string (read-only)
Default: ""
The signature algorithm used in a TLS handshake.
SymmetricBlockSize
int (read-only)
Default: 0
The block size of the symmetric algorithm used.
SymmetricKeyBits
int (read-only)
Default: 0
The key length of the symmetric algorithm used.
TotalBytesReceived
long (read-only)
Default: 0
The total number of bytes received over this connection.
TotalBytesSent
long (read-only)
Default: 0
The total number of bytes sent over this connection.
ValidationLog
string (read-only)
Default: ""
Contains the server certificate's chain validation log. This information may be very useful in investigating chain validation failures.
Version
string (read-only)
Default: ""
Indicates the version of SSL/TLS protocol negotiated during this connection.
Constructors
public TLSConnectionInfo();
Public TLSConnectionInfo()
Creates a new TLSConnectionInfo object.
TLSSettings Type
A container for TLS connection settings.
Remarks
The TLS (Transport Layer Security) protocol provides security for information exchanged over insecure connections such as TCP/IP.
- AutoValidateCertificates
- BaseConfiguration
- Ciphersuites
- ClientAuth
- ECCurves
- Extensions
- ForceResumeIfDestinationChanges
- PreSharedIdentity
- PreSharedKey
- PreSharedKeyCiphersuite
- RenegotiationAttackPreventionMode
- RevocationCheck
- SSLOptions
- TLSMode
- UseExtendedMasterSecret
- UseSessionResumption
- Versions
Fields
AutoValidateCertificates
bool
Default: True
Specifies whether server-side TLS certificates should be validated automatically using internal validation rules.
BaseConfiguration
SecureTransportPredefinedConfigurations
Default: 0
Selects the base configuration for the TLS settings. Several profiles are offered and tuned up for different purposes, such as high security or higher compatibility.
| stpcDefault | 0 | |
| stpcCompatible | 1 | |
| stpcComprehensiveInsecure | 2 | |
| stpcHighlySecure | 3 |
Ciphersuites
string
Default: ""
A list of ciphersuites separated with commas or semicolons. Each ciphersuite in the list may be prefixed with a minus sign (-) to indicate that the ciphersuite should be disabled rather than enabled. Besides the specific ciphersuite modifiers, this property supports the all (and -all) aliases, allowing all ciphersuites to be blanketly enabled or disabled at once.
Note: the list of ciphersuites provided to this property alters the baseline list of ciphersuites as defined by BaseConfiguration. Remember to start your ciphersuite string with -all; if you need to only enable a specific fixed set of ciphersuites. The list of supported ciphersuites is provided below:
- NULL_NULL_NULL
- RSA_NULL_MD5
- RSA_NULL_SHA
- RSA_RC4_MD5
- RSA_RC4_SHA
- RSA_RC2_MD5
- RSA_IDEA_MD5
- RSA_IDEA_SHA
- RSA_DES_MD5
- RSA_DES_SHA
- RSA_3DES_MD5
- RSA_3DES_SHA
- RSA_AES128_SHA
- RSA_AES256_SHA
- DH_DSS_DES_SHA
- DH_DSS_3DES_SHA
- DH_DSS_AES128_SHA
- DH_DSS_AES256_SHA
- DH_RSA_DES_SHA
- DH_RSA_3DES_SHA
- DH_RSA_AES128_SHA
- DH_RSA_AES256_SHA
- DHE_DSS_DES_SHA
- DHE_DSS_3DES_SHA
- DHE_DSS_AES128_SHA
- DHE_DSS_AES256_SHA
- DHE_RSA_DES_SHA
- DHE_RSA_3DES_SHA
- DHE_RSA_AES128_SHA
- DHE_RSA_AES256_SHA
- DH_ANON_RC4_MD5
- DH_ANON_DES_SHA
- DH_ANON_3DES_SHA
- DH_ANON_AES128_SHA
- DH_ANON_AES256_SHA
- RSA_RC2_MD5_EXPORT
- RSA_RC4_MD5_EXPORT
- RSA_DES_SHA_EXPORT
- DH_DSS_DES_SHA_EXPORT
- DH_RSA_DES_SHA_EXPORT
- DHE_DSS_DES_SHA_EXPORT
- DHE_RSA_DES_SHA_EXPORT
- DH_ANON_RC4_MD5_EXPORT
- DH_ANON_DES_SHA_EXPORT
- RSA_CAMELLIA128_SHA
- DH_DSS_CAMELLIA128_SHA
- DH_RSA_CAMELLIA128_SHA
- DHE_DSS_CAMELLIA128_SHA
- DHE_RSA_CAMELLIA128_SHA
- DH_ANON_CAMELLIA128_SHA
- RSA_CAMELLIA256_SHA
- DH_DSS_CAMELLIA256_SHA
- DH_RSA_CAMELLIA256_SHA
- DHE_DSS_CAMELLIA256_SHA
- DHE_RSA_CAMELLIA256_SHA
- DH_ANON_CAMELLIA256_SHA
- PSK_RC4_SHA
- PSK_3DES_SHA
- PSK_AES128_SHA
- PSK_AES256_SHA
- DHE_PSK_RC4_SHA
- DHE_PSK_3DES_SHA
- DHE_PSK_AES128_SHA
- DHE_PSK_AES256_SHA
- RSA_PSK_RC4_SHA
- RSA_PSK_3DES_SHA
- RSA_PSK_AES128_SHA
- RSA_PSK_AES256_SHA
- RSA_SEED_SHA
- DH_DSS_SEED_SHA
- DH_RSA_SEED_SHA
- DHE_DSS_SEED_SHA
- DHE_RSA_SEED_SHA
- DH_ANON_SEED_SHA
- SRP_SHA_3DES_SHA
- SRP_SHA_RSA_3DES_SHA
- SRP_SHA_DSS_3DES_SHA
- SRP_SHA_AES128_SHA
- SRP_SHA_RSA_AES128_SHA
- SRP_SHA_DSS_AES128_SHA
- SRP_SHA_AES256_SHA
- SRP_SHA_RSA_AES256_SHA
- SRP_SHA_DSS_AES256_SHA
- ECDH_ECDSA_NULL_SHA
- ECDH_ECDSA_RC4_SHA
- ECDH_ECDSA_3DES_SHA
- ECDH_ECDSA_AES128_SHA
- ECDH_ECDSA_AES256_SHA
- ECDHE_ECDSA_NULL_SHA
- ECDHE_ECDSA_RC4_SHA
- ECDHE_ECDSA_3DES_SHA
- ECDHE_ECDSA_AES128_SHA
- ECDHE_ECDSA_AES256_SHA
- ECDH_RSA_NULL_SHA
- ECDH_RSA_RC4_SHA
- ECDH_RSA_3DES_SHA
- ECDH_RSA_AES128_SHA
- ECDH_RSA_AES256_SHA
- ECDHE_RSA_NULL_SHA
- ECDHE_RSA_RC4_SHA
- ECDHE_RSA_3DES_SHA
- ECDHE_RSA_AES128_SHA
- ECDHE_RSA_AES256_SHA
- ECDH_ANON_NULL_SHA
- ECDH_ANON_RC4_SHA
- ECDH_ANON_3DES_SHA
- ECDH_ANON_AES128_SHA
- ECDH_ANON_AES256_SHA
- RSA_NULL_SHA256
- RSA_AES128_SHA256
- RSA_AES256_SHA256
- DH_DSS_AES128_SHA256
- DH_RSA_AES128_SHA256
- DHE_DSS_AES128_SHA256
- DHE_RSA_AES128_SHA256
- DH_DSS_AES256_SHA256
- DH_RSA_AES256_SHA256
- DHE_DSS_AES256_SHA256
- DHE_RSA_AES256_SHA256
- DH_ANON_AES128_SHA256
- DH_ANON_AES256_SHA256
- RSA_AES128_GCM_SHA256
- RSA_AES256_GCM_SHA384
- DHE_RSA_AES128_GCM_SHA256
- DHE_RSA_AES256_GCM_SHA384
- DH_RSA_AES128_GCM_SHA256
- DH_RSA_AES256_GCM_SHA384
- DHE_DSS_AES128_GCM_SHA256
- DHE_DSS_AES256_GCM_SHA384
- DH_DSS_AES128_GCM_SHA256
- DH_DSS_AES256_GCM_SHA384
- DH_ANON_AES128_GCM_SHA256
- DH_ANON_AES256_GCM_SHA384
- ECDHE_ECDSA_AES128_SHA256
- ECDHE_ECDSA_AES256_SHA384
- ECDH_ECDSA_AES128_SHA256
- ECDH_ECDSA_AES256_SHA384
- ECDHE_RSA_AES128_SHA256
- ECDHE_RSA_AES256_SHA384
- ECDH_RSA_AES128_SHA256
- ECDH_RSA_AES256_SHA384
- ECDHE_ECDSA_AES128_GCM_SHA256
- ECDHE_ECDSA_AES256_GCM_SHA384
- ECDH_ECDSA_AES128_GCM_SHA256
- ECDH_ECDSA_AES256_GCM_SHA384
- ECDHE_RSA_AES128_GCM_SHA256
- ECDHE_RSA_AES256_GCM_SHA384
- ECDH_RSA_AES128_GCM_SHA256
- ECDH_RSA_AES256_GCM_SHA384
- PSK_AES128_GCM_SHA256
- PSK_AES256_GCM_SHA384
- DHE_PSK_AES128_GCM_SHA256
- DHE_PSK_AES256_GCM_SHA384
- RSA_PSK_AES128_GCM_SHA256
- RSA_PSK_AES256_GCM_SHA384
- PSK_AES128_SHA256
- PSK_AES256_SHA384
- PSK_NULL_SHA256
- PSK_NULL_SHA384
- DHE_PSK_AES128_SHA256
- DHE_PSK_AES256_SHA384
- DHE_PSK_NULL_SHA256
- DHE_PSK_NULL_SHA384
- RSA_PSK_AES128_SHA256
- RSA_PSK_AES256_SHA384
- RSA_PSK_NULL_SHA256
- RSA_PSK_NULL_SHA384
- RSA_CAMELLIA128_SHA256
- DH_DSS_CAMELLIA128_SHA256
- DH_RSA_CAMELLIA128_SHA256
- DHE_DSS_CAMELLIA128_SHA256
- DHE_RSA_CAMELLIA128_SHA256
- DH_ANON_CAMELLIA128_SHA256
- RSA_CAMELLIA256_SHA256
- DH_DSS_CAMELLIA256_SHA256
- DH_RSA_CAMELLIA256_SHA256
- DHE_DSS_CAMELLIA256_SHA256
- DHE_RSA_CAMELLIA256_SHA256
- DH_ANON_CAMELLIA256_SHA256
- ECDHE_ECDSA_CAMELLIA128_SHA256
- ECDHE_ECDSA_CAMELLIA256_SHA384
- ECDH_ECDSA_CAMELLIA128_SHA256
- ECDH_ECDSA_CAMELLIA256_SHA384
- ECDHE_RSA_CAMELLIA128_SHA256
- ECDHE_RSA_CAMELLIA256_SHA384
- ECDH_RSA_CAMELLIA128_SHA256
- ECDH_RSA_CAMELLIA256_SHA384
- RSA_CAMELLIA128_GCM_SHA256
- RSA_CAMELLIA256_GCM_SHA384
- DHE_RSA_CAMELLIA128_GCM_SHA256
- DHE_RSA_CAMELLIA256_GCM_SHA384
- DH_RSA_CAMELLIA128_GCM_SHA256
- DH_RSA_CAMELLIA256_GCM_SHA384
- DHE_DSS_CAMELLIA128_GCM_SHA256
- DHE_DSS_CAMELLIA256_GCM_SHA384
- DH_DSS_CAMELLIA128_GCM_SHA256
- DH_DSS_CAMELLIA256_GCM_SHA384
- DH_anon_CAMELLIA128_GCM_SHA256
- DH_anon_CAMELLIA256_GCM_SHA384
- ECDHE_ECDSA_CAMELLIA128_GCM_SHA256
- ECDHE_ECDSA_CAMELLIA256_GCM_SHA384
- ECDH_ECDSA_CAMELLIA128_GCM_SHA256
- ECDH_ECDSA_CAMELLIA256_GCM_SHA384
- ECDHE_RSA_CAMELLIA128_GCM_SHA256
- ECDHE_RSA_CAMELLIA256_GCM_SHA384
- ECDH_RSA_CAMELLIA128_GCM_SHA256
- ECDH_RSA_CAMELLIA256_GCM_SHA384
- PSK_CAMELLIA128_GCM_SHA256
- PSK_CAMELLIA256_GCM_SHA384
- DHE_PSK_CAMELLIA128_GCM_SHA256
- DHE_PSK_CAMELLIA256_GCM_SHA384
- RSA_PSK_CAMELLIA128_GCM_SHA256
- RSA_PSK_CAMELLIA256_GCM_SHA384
- PSK_CAMELLIA128_SHA256
- PSK_CAMELLIA256_SHA384
- DHE_PSK_CAMELLIA128_SHA256
- DHE_PSK_CAMELLIA256_SHA384
- RSA_PSK_CAMELLIA128_SHA256
- RSA_PSK_CAMELLIA256_SHA384
- ECDHE_PSK_CAMELLIA128_SHA256
- ECDHE_PSK_CAMELLIA256_SHA384
- ECDHE_PSK_RC4_SHA
- ECDHE_PSK_3DES_SHA
- ECDHE_PSK_AES128_SHA
- ECDHE_PSK_AES256_SHA
- ECDHE_PSK_AES128_SHA256
- ECDHE_PSK_AES256_SHA384
- ECDHE_PSK_NULL_SHA
- ECDHE_PSK_NULL_SHA256
- ECDHE_PSK_NULL_SHA384
- ECDHE_RSA_CHACHA20_POLY1305_SHA256
- ECDHE_ECDSA_CHACHA20_POLY1305_SHA256
- DHE_RSA_CHACHA20_POLY1305_SHA256
- PSK_CHACHA20_POLY1305_SHA256
- ECDHE_PSK_CHACHA20_POLY1305_SHA256
- DHE_PSK_CHACHA20_POLY1305_SHA256
- RSA_PSK_CHACHA20_POLY1305_SHA256
- AES128_GCM_SHA256
- AES256_GCM_SHA384
- CHACHA20_POLY1305_SHA256
- AES128_CCM_SHA256
- AES128_CCM8_SHA256
ClientAuth
ClientAuthTypes
Default: 0
Enables or disables certificate-based client authentication.
Set this property to true to tune up the client authentication type:
| ccatNoAuth | 0 | |
| ccatRequestCert | 1 | |
| ccatRequireCert | 2 |
ECCurves
string
Default: ""
Defines the elliptic curves to enable.
Extensions
string
Default: ""
Provides access to TLS extensions.
ForceResumeIfDestinationChanges
bool
Default: False
Whether to force TLS session resumption when the destination address changes.
PreSharedIdentity
string
Default: ""
Defines the identity used when the PSK (Pre-Shared Key) key-exchange mechanism is negotiated.
PreSharedKey
string
Default: ""
Contains the pre-shared key for the PSK (Pre-Shared Key) key-exchange mechanism, encoded with base16.
PreSharedKeyCiphersuite
string
Default: ""
Defines the ciphersuite used for PSK (Pre-Shared Key) negotiation.
RenegotiationAttackPreventionMode
RenegotiationAttackPreventionModes
Default: 2
Selects the renegotiation attack prevention mechanism.
The following options are available:
| crapmCompatible | 0 | TLS 1.0 and 1.1 compatibility mode (renegotiation indication extension is disabled). |
| crapmStrict | 1 | Renegotiation attack prevention is enabled and enforced. |
| crapmAuto | 2 | Automatically choose whether to enable or disable renegotiation attack prevention. |
RevocationCheck
RevocationCheckKinds
Default: 1
Specifies the kind(s) of revocation check to perform.
Revocation checking is necessary to ensure the integrity of the chain and obtain up-to-date certificate validity and trustworthiness information.
| crcNone | 0 | No revocation checking. |
| crcAuto | 1 | Automatic mode selection. Currently this maps to crcAnyOCSPOrCRL, but it may change in the future. |
| crcAllCRL | 2 | All provided CRL endpoints will be checked, and all checks must succeed. |
| crcAllOCSP | 3 | All provided OCSP endpoints will be checked, and all checks must succeed. |
| crcAllCRLAndOCSP | 4 | All provided CRL and OCSP endpoints will be checked, and all checks must succeed. |
| crcAnyCRL | 5 | All provided CRL endpoints will be checked, and at least one check must succeed. |
| crcAnyOCSP | 6 | All provided OCSP endpoints will be checked, and at least one check must succeed. |
| crcAnyCRLOrOCSP | 7 | All provided CRL and OCSP endpoints will be checked, and at least one check must succeed. CRL endpoints are checked first. |
| crcAnyOCSPOrCRL | 8 | All provided CRL and OCSP endpoints will be checked, and at least one check must succeed. OCSP endpoints are checked first. |
This setting controls the way the revocation checks are performed for every certificate in the chain. Typically certificates come with two types of revocation information sources: CRL (certificate revocation lists) and OCSP responders. CRLs are static objects periodically published by the CA at some online location. OCSP responders are active online services maintained by the CA that can provide up-to-date information on certificate statuses in near real time.
There are some conceptual differences between the two. CRLs are normally larger in size. Their use involves some latency because there is normally some delay between the time when a certificate was revoked and the time the subsequent CRL mentioning that is published. The benefits of CRL is that the same object can provide statuses for all certificates issued by a particular CA, and that the whole technology is much simpler than OCSP (and thus is supported by more CAs).
This setting lets you adjust the validation course by including or excluding certain types of revocation sources from the validation process. The crcAnyOCSPOrCRL setting (give preference to the faster OCSP route and only demand one source to succeed) is a good choice for most typical validation environments. The "crcAll*" modes are much stricter, and may be used in scenarios where bulletproof validity information is essential.
NOTE: If no CRL or OCSP endpoints are provided by the CA, the revocation check will be considered successful. This is because the CA chose not to supply revocation information for its certificates, meaning they are considered irrevocable.
NOTE: Within each of the above settings, if any retrieved CRL or OCSP response indicates that the certificate has been revoked, the revocation check fails.
SSLOptions
int
Default: 16
Various SSL (TLS) protocol options, set of
| cssloExpectShutdownMessage | 0x001 | Wait for the close-notify message when shutting down the connection |
| cssloOpenSSLDTLSWorkaround | 0x002 | (DEPRECATED) Use a DTLS version workaround when talking to very old OpenSSL versions |
| cssloDisableKexLengthAlignment | 0x004 | Do not align the client-side PMS by the RSA modulus size. It is unlikely that you will ever need to adjust it. |
| cssloForceUseOfClientCertHashAlg | 0x008 | Enforce the use of the client certificate hash algorithm. It is unlikely that you will ever need to adjust it. |
| cssloAutoAddServerNameExtension | 0x010 | Automatically add the server name extension when known |
| cssloAcceptTrustedSRPPrimesOnly | 0x020 | Accept trusted SRP primes only |
| cssloDisableSignatureAlgorithmsExtension | 0x040 | Disable (do not send) the signature algorithms extension. It is unlikely that you will ever need to adjust it. |
| cssloIntolerateHigherProtocolVersions | 0x080 | (server option) Do not allow fallback from TLS versions higher than currently enabled |
| cssloStickToPrefCertHashAlg | 0x100 | Stick to preferred certificate hash algorithms |
| cssloNoImplicitTLS12Fallback | 0x200 | Disable implicit TLS 1.3 to 1.2 fallbacks |
| cssloUseHandshakeBatches | 0x400 | Send the handshake message as large batches rather than individually |
TLSMode
SSLModes
Default: 0
Specifies the TLS mode to use.
| smDefault | 0 | |
| smNoTLS | 1 | Do not use TLS |
| smExplicitTLS | 2 | Connect to the server without any encryption and then request an SSL session. |
| smImplicitTLS | 3 | Connect to the specified port, and establish the SSL session at once. |
| smMixedTLS | 4 | Connect to the specified port, and establish the SSL session at once, but allow plain data. |
UseExtendedMasterSecret
bool
Default: False
Enables the Extended Master Secret Extension, as defined in RFC 7627.
UseSessionResumption
bool
Default: False
Enables or disables the TLS session resumption capability.
Versions
int
Default: 16
The SSL/TLS versions to enable by default.
| csbSSL2 | 0x01 | SSL 2 |
| csbSSL3 | 0x02 | SSL 3 |
| csbTLS1 | 0x04 | TLS 1.0 |
| csbTLS11 | 0x08 | TLS 1.1 |
| csbTLS12 | 0x10 | TLS 1.2 |
| csbTLS13 | 0x20 | TLS 1.3 |
Constructors
public TLSSettings();
Public TLSSettings()
Creates a new TLSSettings object.
Config Settings (SAMLSPServer Component)
The component accepts one or more of the following configuration settings. Configuration settings are similar in functionality to properties, but they are rarely used. In order to avoid "polluting" the property namespace of the component, access to these internal properties is provided through the Config method.SAMLSPServer Config Settings
Base Config Settings
You can switch this property off to improve performance if your project only uses known, good private keys.
Supported values are:
| off | No caching (default) | |
| local | Local caching | |
| global | Global caching |
This setting only applies to sessions negotiated with TLS version 1.3.
Supported Values:
| auto | Use hardware cryptography if available; otherwise, fall back to software-based cryptography (default). |
| enable | Always attempt to use hardware cryptography. If unavailable, exception will be thrown. |
| disable | Do not use hardware cryptography. |
Supported values are:
| file | File | |
| console | Console | |
| systemlog | System Log (supported for Android only) | |
| debugger | Debugger (supported for VCL for Windows and .Net) |
Supported values are:
| time | Current time | |
| level | Level | |
| package | Package name | |
| module | Module name | |
| class | Class name | |
| method | Method name | |
| threadid | Thread Id | |
| contenttype | Content type | |
| content | Content | |
| all | All details |
Supported filter names are:
| exclude-package | Exclude a package specified in the value | |
| exclude-module | Exclude a module specified in the value | |
| exclude-class | Exclude a class specified in the value | |
| exclude-method | Exclude a method specified in the value | |
| include-package | Include a package specified in the value | |
| include-module | Include a module specified in the value | |
| include-class | Include a class specified in the value | |
| include-method | Include a method specified in the value |
| none | No flush (caching only) | |
| immediate | Immediate flush (real-time logging) | |
| maxcount | Flush cached entries upon reaching LogMaxEventCount entries in the cache. |
Supported values are:
| none | None (by default) | |
| fatal | Severe errors that cause premature termination. | |
| error | Other runtime errors or unexpected conditions. | |
| warning | Use of deprecated APIs, poor use of API, 'almost' errors, other runtime situations that are undesirable or unexpected, but not necessarily "wrong". | |
| info | Interesting runtime events (startup/shutdown). | |
| debug | Detailed information on flow of through the system. | |
| trace | More detailed information. |
The default value of this setting is 100.
| none | No rotation | |
| deleteolder | Delete older entries from the cache upon reaching LogMaxEventCount | |
| keepolder | Keep older entries in the cache upon reaching LogMaxEventCount (newer entries are discarded) |
Supported Values:
| certificate | Enables caching of certificates. |
| crl | Enables caching of Certificate Revocation Lists (CRLs). |
| ocsp | Enables caching of OCSP (Online Certificate Status Protocol) responses. |
Example (default value):
PKICache=certificate,crl,ocsp
In this example, the component caches certificates, CRLs, and OCSP responses.
The default value is an empty string - no cached PKI data is stored on disk.
Example:
PKICachePath=C:\Temp\cache
In this example, the cached PKI data is stored in the C:\Temp\cache directory.
Supported values are:
| none | No static DNS rules (default) | |
| local | Local static DNS rules | |
| global | Global static DNS rules |
This setting only applies to certificates originating from a Windows system store.
The property accepts comma-separated values where the first descriptor name is used when the OID is mapped, and subsequent values act as aliases for parsing.
Syntax:
Config("XMLRDNDescriptorName[OID]=PrimaryName,Alias1,Alias2");
Where:
OID: The Object Identifier from the certificate's IssuerRDN or SubjectRDN that you want to map.
PrimaryName: The main descriptor name used in the XML signature when the OID is encountered.
Alias1, Alias2, ...: Optional alternative names recognized during parsing.
Usage Examples:
Map OID 2.5.4.5 to SERIALNUMBER:
Config("XMLRDNDescriptorName[2.5.4.5]=SERIALNUMBER");
Map OID 1.2.840.113549.1.9.1 to E, with aliases EMAIL and EMAILADDRESS:
Config("XMLRDNDescriptorName[1.2.840.113549.1.9.1]=E,EMAIL,EMAILADDRESS");
Trappable Errors (SAMLSPServer Component)
SAMLSPServer Errors
| 1048577 | Invalid parameter (SB_ERROR_INVALID_PARAMETER) |
| 1048578 | Invalid configuration (SB_ERROR_INVALID_SETUP) |
| 1048579 | Invalid state (SB_ERROR_INVALID_STATE) |
| 1048580 | Invalid value (SB_ERROR_INVALID_VALUE) |
| 1048581 | Private key not found (SB_ERROR_NO_PRIVATE_KEY) |
| 1048582 | Cancelled by the user (SB_ERROR_CANCELLED_BY_USER) |
| 1048583 | The file was not found (SB_ERROR_NO_SUCH_FILE) |
| 1048584 | Unsupported feature or operation (SB_ERROR_UNSUPPORTED_FEATURE) |
| 1048585 | General error (SB_ERROR_GENERAL_ERROR) |
| 30408705 | Invalid binding name (SB_ERROR_SAML_INVALID_BINDING_NAME) |
| 30408706 | Invalid SAML binding type (SB_ERROR_SAML_INVALID_BINDING_TYPE) |
| 30408707 | Base directory not set (SB_ERROR_SAML_SP_BASE_DIRECTORY_NOT_SET) |
| 30408708 | Invalid parameter (SB_ERROR_SAML_INVALID_PARAM) |
| 30408709 | Invalid input data (SB_ERROR_SAML_INVALID_DATA) |
| 30408710 | Data is not loaded (SB_ERROR_SAML_NOT_LOADED) |
| 30408711 | New document is not created (SB_ERROR_SAML_NOT_CREATED) |
| 30408716 | Endpoint of unsupported type encountered or cannot find appropriate IdP service (SB_ERROR_SAML_INVALID_SERVICE) |
| 30408717 | Multiple endpoints of the same kind are not supported (SB_ERROR_SAML_MULTIPLE_ENDPOINTS_NOT_SUPPORTED) |
| 30408718 | Failed to process the request (SB_ERROR_SAML_PROCESSING_FAILED) |
| 30408719 | Session not found (SB_ERROR_SAML_SESSION_NOT_FOUND) |